Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Google Chrome CVE-2024-4058 - Google Patches Four Vulnerabilities Affecting Chrome, Including Critical-Severity Vulnerability CVE-2024-4058 - Google advises users to update their Chrome browser to the latest Chrome 124 version.
CrushFTP VFS Sandbox Escape - CrushFTP vulnerability known as CrushFTP VFS Sandbox Escape – CISA recommended action is to apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
WordPress Plugins – Vulnerabilities were uncovered in various WordPress plugins (HT Mega, Phlox theme, Carousel Slider, 2Checkout Payment Gateway for WooCommerce, WP Cookie Consent) – Updates for the five plugins have been released and should be applied.
Potential Threats
Cisco Zero Day exploit – Cisco Talos published findings about an espionage campaign, ArcaneDoor, targeting perimeter devices including Cisco Adaptive Security Appliances (ASA) and Firepower Threat Defense (FTD) with zero-day vulnerabilities.
APT28/Forest Blizzard group – Microsoft observed the group using a post-compromised tool GooseEgg to exploit Windows flow known as CVE-2022-3828, which effects Windows Print Spooler service.
Deep Fake Social Engineering - LastPass, the password manager application, has issued a warning that one of its employees fell victim to a social engineering attack involving an audio deepfake, which imitated the voice of the company's CEO.
General News
Over 150 Websites Hosted on Weebly Found to be Using BlackHat SEO Poisoning - On April 24, 2024, Zscaler reported that over 150 fraudulent websites hosted on Weebly, a popular web hosting platform, were used to manipulate search engine results and spread malware.
Trend Micro, Interpol Collaborate to Take Down Grandoreiro Banking Trojan - Grandoreiro is a banking trojan that primarily targets users in Latin America and Europe, spreading through phishing emails and malicious attachments.
MITRE research and prototyping network breached via Ivanti zero-days - MITRE has been breached by attackers via two zero-day vulnerabilities (CVE-2023-46805, CVE-2024-21887) in Ivanti's Connect Secure VPN devices.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
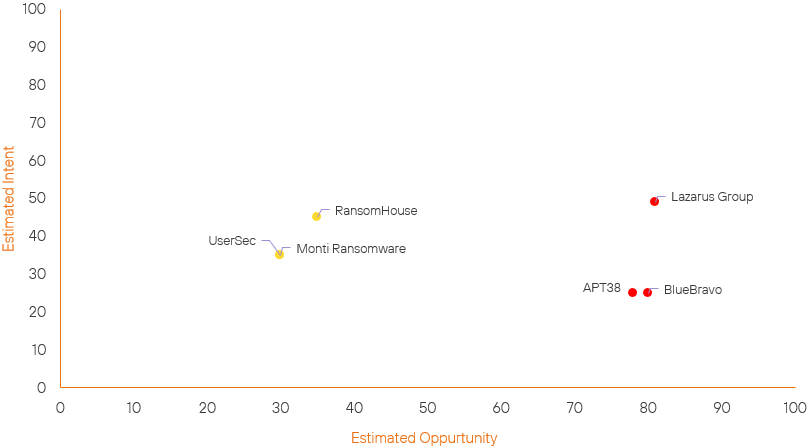
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| RansomHouse Group | Basic | → | Basic | → 0 | (35) | ↑ 5 | (45) |
| Lazarus Group | High | → | High | → 0 | (81) | ↑ 4 | (49) |
| APT38 | High | → | High | ↑ 1 | (78) | → 0 | (25) |
| BlueBravo | High | → | High | ↑ 2 | (80) | → 0 | (25) |
| Monti Ransomware Group | Basic | → | Basic | ↓ 5 | (30) | → 0 | (35) |
| UserSec | Basic | → | Basic | → 0 | (30) | ↓ 14 | (35) |
Prominent Information Security Events
CrushFTP CVE-2024-4040.
Source: NVD, CrowdStrike, Rapid7 | Global Vulnerability Risk, New Critical or Pre NVD Vulnerabilities
Intelligence Cards: Global Vulnerability Monitoring
CVVS Score: 9.8 | Recorded Future Risk Score: Critical - 99
On April 23, 2024, security researcher Simon Garrelou, affiliated with Airbus Community Emergency Response Team (CERT), published Python-based proof-of-concept (PoC) scanner scripts for CVE-2024-4040. CVE-2024-4040 is a critical zero-day sandbox escape vulnerability affecting the CrushFTP versions before 10.7.1 and 11.1.0.
Information from CrowdStrike and Rapid7 detailed how CVE-2024-4040 has been actively exploited in the wild and has affected multiple entities in the United States. This vulnerability is an unauthenticated server-side template injection (SSTI) flaw, which allows unauthenticated threat actors to escape a user’s virtual file system (VFS) and download system files. Aside from reading arbitrary files as root, this vulnerability allows threat actors to bypass authentication for administrator account access and achieve full remote code execution (RCE), which could potentially result in a complete server compromise.
The vulnerability has been fixed in versions 10.7.1 and 11.1.0 of CrushFTP. It is recommended to promptly update to these latest versions to mitigate the risk associated with the vulnerability.
Cisco FTD & ASA CVE.
Source: Cisco Talos | Zero Day Exploit Spike
Intelligence Cards: Trending Attack Methods
CVE-2024-20353 - CVVS Score: 8.6 | Recorded Future Risk Score:
Critical - 99
CVE-2024-20359 - CVVS Score: 6.0 | Recorded Future Risk Score:
Critical - 99
On April 24, 2024, Cisco Talos published findings about an espionage campaign, ArcaneDoor, targeting perimeter devices, including Cisco Adaptive Security Appliances (ASA) and Cisco Firepower Threat Defense (FTD) with zero-day vulnerabilities. While the initial access vector remains unidentified, Cisco assesses that the campaign is attributed to the previously unknown threat actor UAT4356 by Cisco Talos and STORM-1849 by Microsoft that uses CVE-2024-20353 and CVE-2024-20359 to compromise Cisco Adaptive Security Appliances (ASA).
This likely state-sponsored operation affects critical sectors such as telecommunications and energy and has escalated since early indications in November 2023; activities were noted between December 2023 and January 2024. The threat actors employ malware, including Line Dancer, a memory-resident shellcode interpreter, to execute and maintain their malicious activities and Line Runner — a persistent backdoor to establish persistence.
CVE-2024-20353 allows an unauthenticated, remote attacker to cause a denial of service (DoS) condition on the device. This vulnerability occurs due to incomplete error checking when parsing an HTTP header. An attacker can exploit this vulnerability by sending a crafted HTTP request to a targeted web server on the affected device, causing the device to reload unexpectedly.
CVE-2024-20359 allows an authenticated, local attacker to execute arbitrary code with root-level privileges. This vulnerability is caused by improper validation of a file when it is read from system flash memory. An attacker can exploit this vulnerability by copying a crafted file to the file system of the affected device. After the device reloads, the injected code can alter system behaviour and allow the attacker to execute arbitrary code on the device.
Both vulnerabilities have been actively exploited, and Cisco has released software updates to address them. It is crucial for organisations using Cisco ASA and FTD software to apply the necessary updates to mitigate the risk associated with these vulnerabilities.
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular we would recommend applying the following patches should they apply:
- Patch 1
- Patch 2
- Etc
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing these searching and hunting activities within your environment.
