Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Progress Software MOVEit Vulnerability Allows Privilege Escalation - Progress Software identified a high-severity vulnerability CVE-2024-6576 in MOVEit Transfer that can lead to privilege escalation. The vulnerability affects MOVEit Transfer versions from 2023.0.0 to 2023.0.11, 2023.1.0 to 2023.1.6, and 2024.0.0 to 2024.0.2.
CVE-2024-7352 allows Remote Code Execution affecting PDF-XChange Editor – This vulnerability allows remote attackers to execute arbitrary code on affected installations of PDF-XChange Editor. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
CVE-2024-7234 Privilege Escalation affecting AVG - AVG Antivirus Free contains a vulnerability that has been deemed critical. This vulnerability results in privilege escalation when an unknown input is manipulated. Information on potential countermeasures is lacking. Switching out the product for an equivalent one is advised.
Potential Threats
WASP Stealer Delivered by Threat Actors Impersonating Zoom - On July 31, 2024, security researcher JAMESWT shared samples of fake Zoom installers containing the WASP stealer on MalwareBazaar. Also known as W4SP, WASP is an information stealer that primarily targets Discord accounts, passwords, cryptocurrency wallets, and other sensitive data.
Predator Spyware - On July 31, 2024, Insikt Group reported new infrastructure related to Predator spyware. Predator is sophisticated spyware that infects both Android and iPhone devices using various methods, including zero-day vulnerabilities in popular browsers and operating systems.
New BingoMod RAT Masks as Legitimate Application and Wipes Data - BingoMod, a new Android-based banking remote access trojan, is infecting mobile devices to conduct unauthorised money transfers. As reported by Security Firm Cleafy on July 31, 2024, the malware is disguised as antivirus software and is distributed through smishing.
General News
Spyware remained undetected on Google app store - A sophisticated cyber espionage tool known as Mandrake has been found in five apps that were available for download on Google Play for nearly two years, targeting users in Canada, Germany, Italy, Mexico, Spain, Peru and the U.K.
Android Malware Campaign Infects Devices in 113 Countries - On July 29, 2024, Zimperium reported an ongoing campaign distributing Android malware through Telegram bots and malicious advertisements imitating Google Play. The campaign has been targeting Android devices across 113 countries intending to steal one-time passwords (OTPs) for financial gain.
Hackers directly email customers of immigration firm after damaging cyberattack - Sable International, which has offices in the U.K., Australia and South Africa, released several statements this week about a “sophisticated” cyberattack that caused a range of issues, including emailing customers about the incident, likely to put pressure on the firm to pay a ransom.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
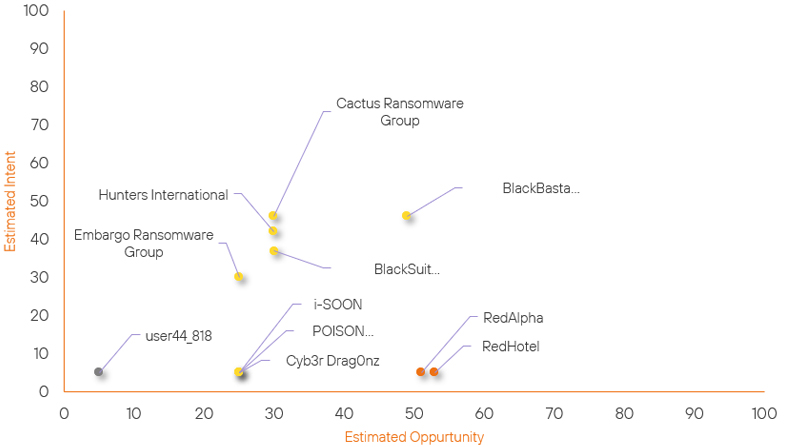
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| RedHotel | New | → | Moderate | (53) | ↑ 53 | (5) | ↑ 5 |
| RedAlpha | New | → | Moderate | (51) | ↑ 51 |
(5) | ↑ 5 |
| Embargo Ransomware Group | New | → | Basic | (25) | ↑ 25 | (30) | ↑ 30 |
| i-SOON | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
| POISON CARP | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
| Cyb3r Drag0nz | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
| BlackBasta Ransomware | Basic | → | Basic | (49) | ↑ 9 | (46) | ↑ 1 |
| user44_818 | New | → | Limited | (5) | ↑ 5 | (5) | ↑ 5 |
| BlackSuit Ransomware | Basic | → | Basic | (30) | → 0 | (37) | ↑ 2 |
| Hunters International | Basic | → | Basic | (30) | → 0 | (42) | ↑ 2 |
| Cactus Ransomware Group | Basic | → | Basic | (30) | → 0 | (46) | ↑ 1 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Anonymous | ▲ | DDoS | ▲ | CVE-2024-27878 | ▲ | Venezuela | ▲ |
| Daggerfly | ▲ | SLUBStick | ▲ | CVE-2024-38100 | ▲ | Japanese Defense Industry | ▲ |
| RedGolf | ▲ | DNS Spoofing | ▲ | CVE-2018-0824 | ▲ | Mitsubishi Group | ▲ |
| Handala | ▲ | STRRAT | ▲ | CVE-2019-12760 | ▲ | Nicolas Maduro | ▲ |
| BlueDelta | ▲ | Backdoor | ▲ | CWE-287 (Improper Authentication) | ▲ | Key Tronic Corporation | ▲ |
Prominent Information Security Events
WASP Stealer Zoom Impersonation.
Source: Insikt Group, MalwareBazaar | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256: 05b260fc440595c0fd56db2fc45dce370b0699f2063213d272cf752081e59ca1
IOC: SHA256: 986703784ca9da132c5f34dfcc59b805efb1d25e2b0bdd796b274f0ea8df5db7
IOC: SHA256: 3c34aa1bcc610f61ae1fe84cc074b6b70b837f11f8ce0f89f802880673c12e3d
IOC: IP: 103[.]167[.]84[.]233
On July 31, 2024, security researcher JAMESWT shared samples of fake Zoom installers that contain the WASP stealer on MalwareBazaar. WASP, also known as W4SP, is an information stealer that primarily targets Discord accounts, passwords, cryptocurrency wallets, and other sensitive data.
Sandbox analysis detected the WASP stealer sample as malicious because it exhibited defence evasion, discovery, execution, privilege escalation, and steelware capabilities.
Once executed, the WASP stealer sample performs the following actions on a victim’s machine:
- Conducts API hooking, DLL Injection, and reflective portable execution (PE) injection
- Detects debuggers
- Checks for Uninstall key entries in the Windows registry to enumerate installed applications
- Uses the Task Scheduler COM API to execute at a specified time
- Searches for mail accounts
- Checks for available system drives
- Drops and executes “Zoom_workspace.hta” inside the %temp% directory
Insikt Group's static code analysis of Zoom_workspace.hta revealed it contains an encoded string that decodes to JavaScript that:
- Connects to WMI to list and block certain processes
- Drops and executes DownloadAndRun.ps1
DownloadAndRun.ps1 was then analysed and revealed it conducts the following actions:
- Authenticates to a remote network share using provided credentials
- Checks for and copies Zoom_workspace.exe if it exists
- Executes the file and creates a startup shortcut
- Disconnects from the remote share
MOVEit Privilege Escalation.
Source: Insikt Group, Progress | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-6576 | CVVS Score: 7.3 | Recorded Future Risk Score: Medium – 32
Progress Software identified a high-severity vulnerability, CVE-2024-6576, in MOVEit Transfer that can lead to privilege escalation. The vulnerability affects MOVEit Transfer versions 2023.0.0 to 2023.0.11, 2023.1.0 to 2023.1.6, and 2024.0.0 to 2024.0.2.
Progress Software has released patches to fix this issue which include versions 2024.0.3, 2023.1.7, or 2023.0.12.
According to Progress’ advisory on July 29, 2024, MOVEit Cloud users are already protected, as their systems have already been updated to the patched version.
The upgrade process requires downloading the fixed version from the Progress Community portal and installing it using the full installer, which may cause a temporary disruption. Additionally, organisations should monitor their MOVEit Transfer logs for suspicious activity.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- MOVEit– Update to versions 2024.0.3, 2023.1.7, or 2023.0.12 for
- PDF-XChange Editor – Update to version 10.3.0.386 to fix the issue.
We also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
