Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
CVE-2024-7600 - Arbitrary File Deletion in Logsign SecOps – This vulnerability allows an authenticated remote attacker to delete arbitrary files on the Logsign Unified SecOps Platform. By exploiting this flaw, an attacker with valid credentials can perform destructive actions with root privileges, leading to severe risks to the system's integrity and availability.
CVE-2024-20452 – Buffer Overflow in Cisco Small Business SPA300 Series and SPA500 Series IP Phones – This vulnerability’s inadequate bounds checking allows unauthenticated attackers to send specially crafted HTTP packets, potentially resulting in arbitrary command execution with root privileges on Cisco Small Business SPA300 and SPA500 Series IP Phones.
CVE-2024-7586 – Information Disclosure in GitLab Enterprise Edition – This vulnerability allows unauthorised access to potentially sensitive information through webhook deletion audit logs. This issue can lead to the exposure of confidential data and credentials in GitLab Enterprise Edition versions 17.0.0 through 17.2.1.
Potential Threats
Disinformation Campaign Targets Android Users - A campaign manipulates Google search results to redirect Android users to fake sites on Microsoft Azure and OVH, spreading malware and spam.
SystemBC Malware in Social Engineering Campaign - Active since June 20, 2024, this campaign uses AnyDesk to distribute SystemBC malware, suspected to be linked to the BlackBasta Ransomware Group, targeting users to steal credentials and escalate privileges.
New Gafgyt Botnet Variant for GPU Crypto Mining - On August 14, 2024, Aqua Nautilus reported a Gafgyt botnet variant exploiting weak SSH passwords to deploy XMRig for GPU-based Monero mining in cloud environments.
General News
Massive AWS Cyber Attack Compromises 230 Million Environments - On August 17, 2024, Cybersecurity News reported a significant cyber-attack affecting Amazon Web Services (AWS). The breach exposed over 230 million environments, potentially leading to extensive data theft and service disruptions. AWS is investigating the incident and advising customers on immediate protective measures to mitigate the impact.
Microsoft Mandates MFA for Azure Accounts to Enhance Security - Microsoft has announced that multi-factor authentication (MFA) will be required for all Azure accounts from October to enhance security and prevent unauthorised access.
CISA Warns of Exploited Critical SolarWinds RCE Vulnerability - CISA has issued a warning about a critical Remote Code Execution (RCE) vulnerability in SolarWinds products. This flaw, tracked as CVE-2024-28986, is actively being exploited in attacks. It affects SolarWinds Web Help Desk (WHD) and can allow attackers to execute arbitrary code with elevated privileges. CISA advises immediate patching to mitigate the risk of compromise.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
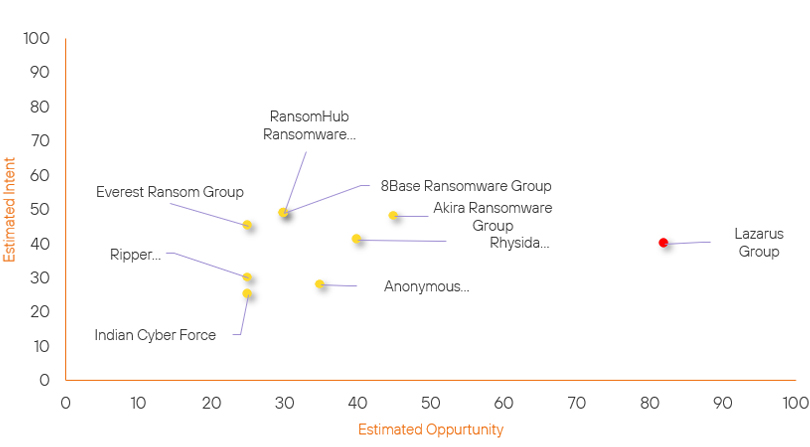
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Rhysida Ransomware Group | Basic | → | Basic | (40) | → 0 | (41) | ↑ 5 |
| Akira Ransomware Group | Basic | → | Basic | (45) | ↑ 5 |
(48) | → 0 |
| RipperSec | Basic | → | Basic | (25) | → 0 | (30) | ↑ 5 |
| RansomHub Ransomware Group | Basic | → | Basic | (30) | ↑ 5 | (49) | → 0 |
| Lazarus Group | High | → | High | (82) | ↑ 1 | (40) | → 0 |
| Anonymous Sudan | Basic | → | Basic | (35) | → 0 | (28) | ↓ 1 |
| Indian Cyber Force | Basic | → | Basic | (25) | → 0 | (25) | ↓ 5 |
| Everest Ransom Group | Basic | → | Basic | (25) | ↓ 5 | (45) | → 0 |
| 8Base Ransomware Group | Basic | → | Basic | (30) | ↓ 5 | (49) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Mad Liberator | ▲ | Cross site scripting | ▲ | CVE-2024-38193 | ▲ | Government of the United Kingdom | ▲ |
| HUNT3R | ▲ | ALPHV Ransomware | ▲ | CVE-2024-38063 | ▲ | Foreign and Commonwealth Office (UK) | ▲ |
| ANTIFA | ▲ | DDoS | ▲ | CVE-2024-29745 | ▲ | Professional and commercial services | ▲ |
| APT42 | ▲ | ShrinkLocker | ▲ | CVE-2024-32896 | ▲ | Mitsubishi | ▲ |
| Iranian Hackers | ▲ | Social Engineering | ▲ | CVE-2023-30013 | ▲ | The Washington Times LLC | ▲ |
Prominent Information Security Events
Disinformation Campaign Targets Android Users Using Azure and Google Search
Source: Insikt Group, Bleeping Computer | Intelligence
Intelligence Cards: Intelligence & Reports
IOC: flashnews2.s3.uk.io.cloud.ovh.net
IOC: celebradar.blob.core.windows.net
IOC: sopnews.blob.core.windows.net
IOC: applebulletin.blob.core.windows.net
On August 17, 2024, BleepingComputer reported a new disinformation campaign that targets Android users by manipulating search results through Microsoft's Azure and Google's platforms. This campaign involves sophisticated tactics to mislead users and distribute malware.
The attackers exploit Google’s notification system to manipulate search results. This means they use this system to push malicious sites higher in the search rankings, leading users to deceptive and fraudulent content. The malicious sites are hosted on Microsoft Azure blob storage and OVH cloud services, which are typically used for legitimate purposes. By exploiting these platforms, attackers can disguise their sites as legitimate articles or resources, making them more convincing to users.
Once users land on these fraudulent sites, they encounter scripts designed to perform several malicious actions. These include redirecting users to other harmful sites, deploying malware payloads, and facilitating phishing attacks through obfuscated JavaScript and other deceptive techniques. The campaign specifically targets Android users, taking advantage of the operating system’s widespread use and potential vulnerabilities.
The fraudulent sites are crafted to exploit these weaknesses, putting users at significant risk of malware infection and data theft. To protect against these threats, users should be cautious of unexpected search results and verify the authenticity of websites before interacting with them. Additionally, keeping browsers, software, and security tools up to date is essential to mitigate the risk and safeguard against such malicious campaigns.
Buffer Overflow in Cisco Small Business SPA300 Series and SPA500 Series IP Phones.
Source: Insikt Group, Cisco | Informational
Intelligence Cards: Intelligence & Reports
CVE-2024-20452 | CVVS Score: 9.8| Recorded Future Risk Score: High –71
CVE-2024-20452 is a critical cyber vulnerability affecting Cisco Small Business SPA300 and SPA500 Series IP Phones.
The vulnerability is primarily due to inadequate bounds checking, which can lead to a buffer overflow. An attacker can exploit this vulnerability without needing authentication, making it particularly dangerous. By delivering specially crafted HTTP packets, they can overrun a buffer and gain control over the device.
Successful exploitation can result in the execution of arbitrary commands at the root privilege level, potentially compromising the device's functionality and security.
Cisco has said it does not intend to release software updates to address the flaws, as the appliances have reached end-of-life (EoL) status, necessitating that users transition to newer models. Therefore, it is recommended that users replace the affected products with suitable alternatives to mitigate the risk.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- CVE-2024-20452 - Replace the affected products with suitable alternatives to mitigate the risk.
- CVE-2024-7600 – Update the affected products to Logsign Unified SecOps Platform 6.4.23 is recommended to mitigate the issue
- CVE-2024-7586 – Update to the latest patched versions available from the vendor’s website.
We also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
