Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Threat Actors Exploiting CVE-2024-40891 in Zyxel CPE Series - GreyNoise reports active exploitation of CVE-2024-40891, which allows arbitrary command execution via service accounts. Over 1,500 vulnerable devices remain online, with 854 attack attempts traced to Taiwan. Users should monitor Zyxel advisories for patches, filter unusual Telnet requests, and restrict admin access to trusted IPs to mitigate risks.
Threat Actors Target SimpleHelp RMM After Vulnerability Disclosure - Arctic Wolf has observed a campaign targeting SimpleHelp RMM software just days after Horizon3 disclosed vulnerabilities (CVE-2024-57726, CVE-2024-57727, CVE-2024-57728). While exploitation is unconfirmed, threat actors have used unauthorised servers and tools such as 'net' and 'nltest' to gather system data. Users should update SimpleHelp, remove unused clients, and implement network segmentation to reduce exposure.
NVIDIA Urges Users to Patch Critical GPU Driver Vulnerabilities - NVIDIA has issued critical security updates for its GPU Display Driver and Virtual GPU software, addressing several vulnerabilities, including CVE-2024-0149, which exposes Linux users to the risk of remote file access and data leakage. Other flaws may lead to denial of service or code execution. Users are urged to update their drivers immediately to prevent potential exploitation.
Potential Threats
New Aquabotv3 Malware Variant Targets Mitel SIP Phones - Akamai has identified a new Aquabotv3 botnet variant exploiting CVE-2024-41710 in Mitel SIP phones, enabling remote code execution and root access via unsanitised HTTP POST requests. The malware introduces a "report_kill" function to notify its command-and-control server when terminated. It installs via a malicious shell script and supports multiple architectures, including x86, ARM, and MIPS.
Linux Version of SystemBC RAT Shared on X - ANY.RUN has reported a Linux version of the SystemBC RAT targeting corporate networks, cloud infrastructures, and IoT devices. This variant employs advanced evasion tactics, making detection harder than its Windows counterpart. The RAT uses encrypted communication for persistence and covert access.
Google Services Number and Subdomain Used in Targeted Phishing Attempt - Attackers leveraged Google’s automated services number and a legitimate subdomain to impersonate Google Workspace support in a phishing attempt. The attacker, posing as "Chloe", sent a convincing email that bypassed security checks, tricking victims into disclosing sensitive information. Google has not commented, but users are advised to verify support requests through official channels and enhance security awareness.
General News
WhatsApp accuses Paragon of targeting about 90 users with spyware - WhatsApp notified victims and took action to prevent further intrusions. WhatsApp has accused the surveillance firm Paragon of targeting approximately 90 users—including journalists and civil society members—with spyware. The attack involved a malicious PDF, which WhatsApp successfully disrupted. Paragon, founded by former Israeli intelligence officers, was identified as the source. WhatsApp has notified victims and taken action to prevent further intrusions.
Italy blocks Chinese AI tool DeepSeek over privacy concerns - Italy’s data protection authority, Garante, has banned the Chinese AI company DeepSeek after it claimed exemption from European privacy laws. Authorities are investigating DeepSeek’s data collection practices, particularly regarding personal data stored on Chinese servers.
Smiths Group Acknowledges Unauthorised Access in Cyberattack - UK-based engineering firm Smiths Group reported a cybersecurity breach on 28 January 2025. Unauthorised access was detected, prompting the company to isolate affected systems and activate business continuity measures. Further details have not yet been disclosed.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
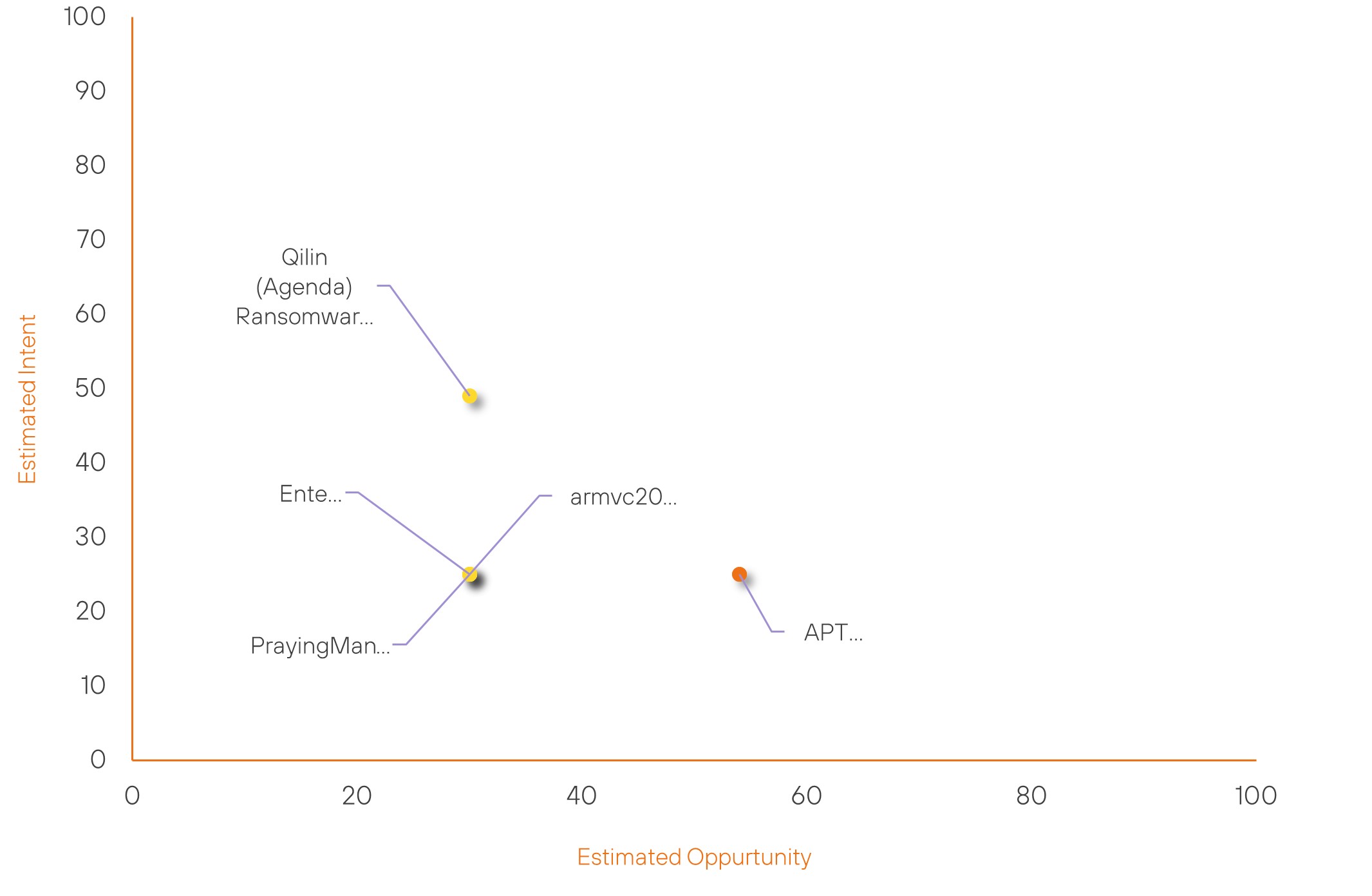
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| APT10 | Moderate | → | Moderate | (54) | ↓ 1 | (25) | → 0 |
| Enter0 | New | → | Basic | (30) | ↑ 30 | (25) | ↑ 25 |
| armvc2000 | New | → | Basic | (30) | ↑ 30 | (25) | ↑ 25 |
| Qilin (Agenda) Ransomware Group | Basic | → | Basic | (30) | ↓ 5 | (49) | → 0 |
| PrayingMantis | Basic | → | Basic | (30) | ↓ 5 | (25) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| APT33 | ▲ | Shamoon Wiper (Disttrack) | ▲ | BrakTooth | ▲ | DataRobot, Inc | ▲ |
| INDOHAXSEC | ▲ | Zero Day Exploit | ▲ | CVE-2014-0160 (Heartbleed) | ▲ | WhatsApp Inc. | ▲ |
| Handala Hack Team | ▲ | Banking Trojan | ▲ | CVE-2024-20720 | ▲ | WhatsApp Inc. | ▲ |
| PlushDaemon | ▲ | Credential Stuffing | ▲ | CVE-2024-44243 | ▲ | BeyondTrust Software Corp | ▲ |
| Eagle Cyber Crew | ▲ | Stealc | ▲ | CVE-2025-24118 | ▲ | BeyondTrust Software Corp | ▲ |
Prominent Information Security Events
New Aquabotv3 Malware Variant Targets Mitel SIP Phones
Source: Insikt Group, Akamai | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - e06c3f5c32aaa422e66056290eb566065afe2ce611fe019f3ba804af939ac1a3
IOC: Domain - fuerer-net[.]ru
IOC: IP – 91[.]92[.]243[.]233
IOC: CVE-2024-41710 | CVVS Score: 8.5 | Recorded Future Risk Score: Very Critical - 99
On 28 January 2025, the Akamai Security Intelligence and Response Team (SIRT) identified Aquabotv3, a new variant of the Aquabot botnet, actively exploiting CVE-2024-41710. This command injection vulnerability in Mitel SIP phones allows authenticated attackers to execute remote code, facilitating botnet expansion and DDoS attacks. Affected devices include the Mitel 6800, 6900, and 6900w Series SIP Phones.
Aquabotv3 leverages a proof-of-concept (PoC) exploit released in August 2024, which targets 8021xsupport.html, a vulnerable endpoint in Mitel devices. The malware injects malicious code into /nvdata/etc/local.cfg, ensuring persistence through a remote shell script (bin.sh) executed at boot. It also introduces a report_kill() function, which notifies its command-and-control (C2) server when an infected device receives a termination signal.
Beyond Mitel phones, Aquabotv3 exploits additional vulnerabilities, including those found in TP-Link devices, IoT firmware, Dasan routers, Linksys E-Series, and Hadoop YARN RCE flaws. The malware establishes C2 communication via TCP, enabling remote command execution.
To mitigate risk, organisations should apply the latest firmware updates to patch CVE-2024-41710 and secure affected devices. Restricting access to 8021xsupport.html and monitoring network activity for unusual traffic are also recommended.
Linux Version of SystemBC RAT Shared on X
Source: Insikt Group, ANY.RUN | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - de1091252ebf2ed617e300c40a2c56ccac8a3e1b5c7f0e87a1cc3636766abe51
IOC: IP - 79[.]110[.]62[.]198
IOC: Domain – cluster.amazonaws[.]work
On 28 January 2025, ANY.RUN reported a Linux version of the SystemBC RAT, a proxy malware that enables stealthy lateral movement within compromised networks. This variant targets corporate networks, cloud infrastructures, and IoT devices, providing persistent access while employing advanced evasion tactics, making detection significantly harder than its Windows counterpart.
The Linux SystemBC RAT facilitates movement within networks by using proxy capabilities and encrypted C2 communication via a custom protocol. This ensures continued access to the attacker’s infrastructure across both Windows and Linux environments.
Insikt Group obtained two SystemBC RAT Linux samples shared by ANY.RUN.
- Sample 1: Packed with UPX, reads system info from /proc, and connects to a specific IP address for C2 communication.
- Sample 2: Queries kernel information, manages systemd services, and sends a DNS request over HTTPS, prompting for a password.
To mitigate the risk of SystemBC RAT infections, organisations should monitor for unusual outbound traffic to known C2 domains and IPs, restrict unauthorised use of systemd services, and apply endpoint detection and response (EDR) rules to flag SystemBC-like behaviours.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-40891 – To mitigate risks, users should monitor Zyxel advisories for patches, filter unusual Telnet requests, and restrict admin access to trusted IPs.
- CVE-2024-57726, CVE-2024-57727, CVE-2024-57728 – Users should update SimpleHelp, remove unused clients, and secure their networks to mitigate risks.
- CVE-2024-0149 – To mitigate risk, users should update their GPU drivers to the latest versions.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
