Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
High-Severity Kernel Vulnerability in Android, Actively Exploited - Google disclosed CVE-2024-53104, a privilege escalation flaw in Android’s USB Video Class (UVC) driver. Due to improper frame parsing, it allows a buffer overflow, enabling arbitrary code execution or denial-of-service (DoS). Exploitation requires physical access via malicious USB devices to escalate privileges or extract data. CISA has added it to the Known Exploited Vulnerabilities (KEV) catalogue, and Google released a patch on February 5, 2025.
Critical RCE Vulnerability in Microsoft Outlook Exploited in Attacks - CVE-2024-21413 is a critical vulnerability in Microsoft Outlook that allows attackers to craft malicious file paths using the “file://” protocol. When users click on these links, Outlook’s security fails to block them, allowing attackers to steal NTLM credentials and execute remote code. CISA confirmed active exploitation on February 6, 2025, and added it to the KEV catalogue. Microsoft has released patches, and CISA urges organisations to apply them by February 27, 2025.
PoC Exploit for CVE-2025-21293 in Microsoft Active Directory Domain Services - A security researcher released a Proof-of-Concept (PoC) exploit for CVE-2025-21293 on GitHub. This high-severity vulnerability in Active Directory Domain Services (AD DS) arises from excessive privileges granted to the "Network Configuration Operators" group, enabling attackers to escalate privileges to SYSTEM via malicious Performance Counter DLLs. Microsoft patched the flaw in its January 2025 security update, and organisations are urged to apply the fix to mitigate exploitation risks.
Potential Threats
Malicious Apps Using OCR to Steal Cryptocurrency Keys Target Android and iOS Users - Researchers at Kaspersky report that the 'SparkCat' malware campaign has infected over 242,000 apps on Google Play and the Apple App Store. Active since March 2024, the malware uses OCR technology to steal cryptocurrency recovery keys. It communicates with a C2 server via a custom Rust-based protocol, marking the first known instance of OCR spyware in Apple’s official marketplace.
ELF/Sshdinjector.A!tr Malware Targets Linux-Based Devices - Fortinet's analysis reveals that ELF/Sshdinjector.A!tr, a Linux-based malware linked to the DaggerFly espionage group, infects network appliances and IoT devices by compromising the SSH daemon. First detected in November 2024, it uses a dropper and a malicious SSH library (libsshd.so) to establish persistence and enable remote command execution. The malware communicates with a C2 server, exfiltrating system data and enabling various malicious actions. Fortinet identified multiple malicious components, including x6 (dropper) and libsshd.so, associated with the attack.
Re-registration of Abandoned AWS S3 Buckets Facilitating Supply Chain Attacks - Watchtowr reported a PoC attack showing how re-registering abandoned AWS S3 buckets can facilitate supply chain attacks. Researchers found 150 abandoned buckets, repopulated them with malware, and observed millions of HTTPS requests from organisations. These buckets could unknowingly distribute malicious files, such as software updates and precompiled binaries, potentially compromising software development environments or injecting malicious code into unverified .pom files used by developers.
General News
UK Orders Apple to Unlock Encrypted Data - The UK government has secretly ordered Apple to unlock encrypted iPhones for a criminal investigation. Apple, known for resisting such requests to protect user privacy, faces growing pressure to balance security concerns with privacy rights.
Private Equity Firm to Acquire SolarWinds for $4.4 Billion - Turn/River Capital has agreed to purchase SolarWinds in an all-cash deal, transitioning the company to private ownership.
UK Launches Cyber Monitoring Centre to Create a "Digital Richter Scale" for Cyberattacks - The UK has unveiled a new Cyber Monitoring Centre designed to measure and track the impact of cyberattacks, much like a Richter scale does for earthquakes. The centre will collect data from both the private and public sectors to assess and respond to cyber risks more effectively.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
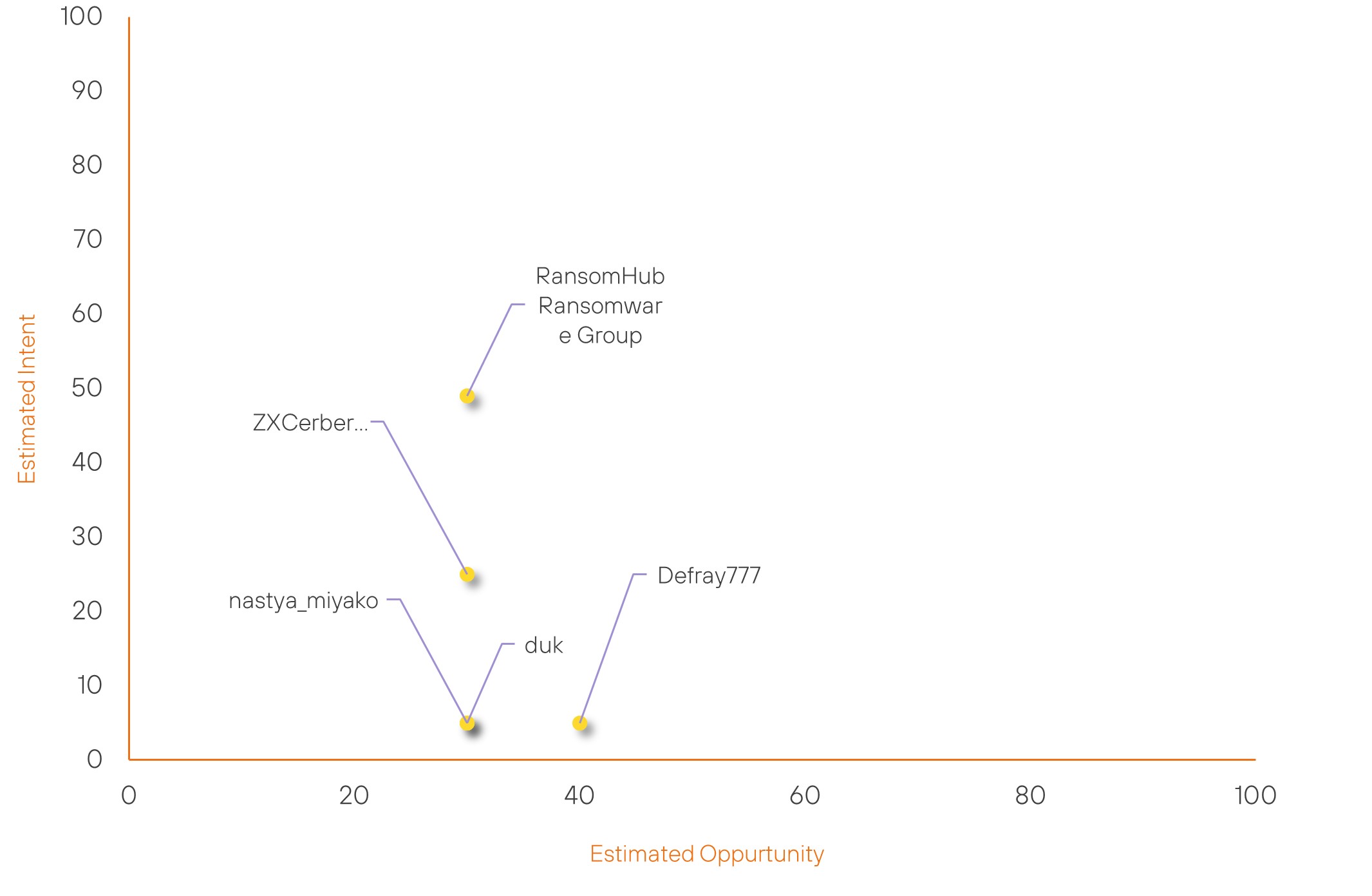
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| ZXCerberus | New | → | Basic | (30) | ↑ 30 | (25) | ↑ 25 |
| Defray777 | New | → | Basic | (40) | ↑ 40 | (5) | ↑ 5 |
| duk | New | → | Basic | (30) | ↑ 30 | (5) | ↑ 5 |
| nastya_miyako | New | → | Basic | (30) | ↑ 30 | (5) | ↑ 5 |
| RansomHub Ransomware Group | Basic | → | Basic | (30) | ↓ 15 | (49) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Handala Hack Team | ▲ | BadIIS | ▲ | CVE-2017-17215 | ▲ | Electronics | ▲ |
| Egyptian hackers | ▲ | Clop Ransomware | ▲ | CVE-2024-57968 | ▲ | Apple | ▲ |
| DragonRank | ▲ | Social Engineering | ▲ | CVE-2017-11882 | ▲ | ▲ | |
| Iranian Hackersn | ▲ | Android application package | ▲ | CVE-2024-12754 | ▲ | Mobile Device Technology | ▲ |
| PlushDaemon | ▲ | Botnet | ▲ | CVE-2025-0411 | ▲ | GitHub | ▲ |
Prominent Information Security Events
Malicious Apps Using OCR to Steal Cryptocurrency Keys Target Android and iOS Users
Source: Insikt Group, Cyber Security News | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - 19d781da353747c7b1dfacd3f9b5c6c82855e168e48b113884f4d6186fd5dc20
IOC: SHA256 - da5847e69180b860d086141513757c0278624ce186856fec8b3a6429ac46bf4a
IOC: Domain - uploads.99ai[.]world
IOC: URL - https://dmbucket102.s3.ap-northeast-1[.]amazonaws[.]com
On 5 February 2025, Kaspersky researchers uncovered SparkCat, a malware campaign exploiting OCR technology to steal cryptocurrency recovery keys from images. Active since March 2024, SparkCat infected over 242,000 apps on Google Play and the Apple App Store, making it the first known instance of OCR-based spyware in Apple's official marketplace.
The malware communicates with a command-and-control (C2) server via a custom Rust-based protocol, encrypting data using AES-256 and AES-GCM_SIV before transmission. It targets various app categories, including food delivery and AI tools, scanning images for seed phrases to facilitate cryptocurrency theft.
The malicious apps contained compromised SDKs and were distributed through both official and unofficial sources. Researchers warn that SparkCat may evolve to target sensitive data beyond cryptocurrency wallets.
Users should carefully review app permissions, avoid unverified downloads, and monitor their accounts for unauthorised transactions.
ELF/Sshdinjector.A!tr Malware Targets Linux-Based Devices
Source: Insikt Group, Fortinet | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - 94e8540ea39893b6be910cfee0331766e4a199684b0360e367741facca74191f
IOC: SHA256 - 0e2ed47c0a1ba3e1f07711fb90ac8d79cb3af43e82aa4151e5c7d210c96baebb
IOC: IP - 45.125.64[.]200
IOC: Domain – hxxp://223.165.4[.]175:81/x6
On 4 February 2025, Fortinet identified ELF/Sshdinjector.A!tr, a Linux-based malware targeting network appliances and IoT devices. Linked to the Lunar Peek espionage campaign by the DaggerFly group (TAG-102), the malware injects a malicious SSH library (libsshd.so) to gain persistence and execute remote commands.
The malware includes a dropper (x6) that verifies root privileges before initiating infection. If successful, it replaces system binaries (ls, netstat, crond) with trojanised versions to evade detection. The primary payload (libsshd.so) creates backdoor functionality, allowing attackers to execute commands, exfiltrate data, and establish persistence.
ELF/Sshdinjector.A!tr communicates with a hardcoded C2 server (45.125.64[.]200) over ports 33200 and 33223. It collects system information, user credentials, and network activity while enabling remote control of compromised devices. Sandbox analysis linked the malware to DarkWood due to its credential harvesting and system enumeration tactics.
To mitigate risks, organisations should update firmware, monitor SSH activity, restrict access, and implement network segmentation.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-53104 – Users should update their Android devices to the latest version, which includes the patch released by Google on February 5, 2025.
- CVE-2024-21413 – To mitigate the risk, users should update Microsoft Outlook to the latest version, applying the patch provided by Microsoft.
- CVE-2025-21293 – Users should apply the security update released by Microsoft in January 2025 to mitigate the risk of exploitation
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
