Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Threat Actors Actively Exploiting Fortinet Authentication Bypass Vulnerability Tracked As CVE-2024-55591 - Threat actors are actively exploiting CVE-2024-55591, an authentication bypass zero-day vulnerability in FortiOS (7.0.0 through 7.0.16 )and FortiProxy (7.0.0 through 7.0.19 and 7.2.0 through 7.2.12).
Researcher Discloses DDoS Vulnerability in OpenAI's ChatGPT API - A vulnerability in OpenAI's ChatGPT API, which currently does not possess a CVE identifier, allows potential Distributed Denial-of-Service (DDoS) attacks through improper handling of requests. Security researcher Benjamin Flesch identified that the API fails to detect duplicate hyperlinks and does not limit the number of hyperlinks per request. This can trigger the ChatGPT crawler, which collects web data to improve responses and send excessive requests from Microsoft Azure, potentially overloading the target website.
Microsoft Patches UEFI Secure Boot Flaw CVE-2024-7344 Affecting Microsoft-signed Applications - On January 14, 2025, Microsoft patched a vulnerability affecting products under Microsoft-signed applications, tracked as CVE-2024-7344. CVE-2024-7344 is a UEFI secure boot bypass flaw with a medium severity rating (CVSS v3 6.5). The vulnerability stems from Microsoft-signed applications using a configured PE loader that allows the loading of any UEFI binary, allowing threat actors to deploy malicious UEFI bootkits if exploited.
Potential Threats
Microsoft 365 Passwords Targeted in FastHTTP Attacks - On January 6, 2025, threat actors started exploiting the FastHTTP Go library to conduct high-speed brute-force attacks against Microsoft 365 accounts via the Azure Active Directory Graph API. According to a January 13, 2025 report by SpearTip, these attacks, FastHTTP's lower latency capabilities to automate large-scale login attempts.
Lumma Stealer Campaign Using Fake CAPTCHAS To Run Malicious Scripts - On January 13, 2025, CERT-AGID shared an exploitation method demonstrated by Lumma Stealer malware using fake CAPTCHA challenges. The attack begins with victims receiving phishing emails regarding alleged security vulnerabilities in their GitHub repositories, urging them to click on a malicious link.
DigitalPulse Proxyware Distributed Through Advertising Pages - On January 13, 2025, AhnLab Security Emergency Response Center (ASEC) reported that DigitalPulse proxyware is being distributed through advertising pages on freeware websites. This campaign uses AutoClicker, software that masquerades as a legitimate automatic mouse-clicker GUI embedded with malicious strings for downloader functionality, to download and install DigitalPulse. DigitalPulse would then hijack the victim's network bandwidth for external profit.
General News
UK Domain Registry Nominet Confirmed Ivanti Zero-Day Used to Breach Networks - On January 9, 2024, Nominet, a UK-based domain registry company, confirmed that an unidentified threat actor gained unauthorised access to its network by exploiting a zero-day vulnerability affecting Connect Secure, a VPN solution from Ivanti. Nominet noted that there was no evidence of data compromise or malware deployment.
FTC cracks down on GoDaddy for cybersecurity failings - The web hosting giant GoDaddy will be required to bolster its cybersecurity program to address years-long deficiencies, the Federal Trade Commission (FTC) announced on Wednesday. GoDaddy’s failure to use industry-standard security measures led to what the FTC called “several major security breaches” between 2019 and 2022. The agency also alleges that GoDaddy deceived its customers about how adequately it safeguards its web hosting product.
UK proposes banning hospitals and schools from making ransomware payments - The United Kingdom proposed on Tuesday a major overhaul of how the country responds to ransomware attacks, including by banning public sector bodies from making extortion payments and requiring all victims to report incidents to the government.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
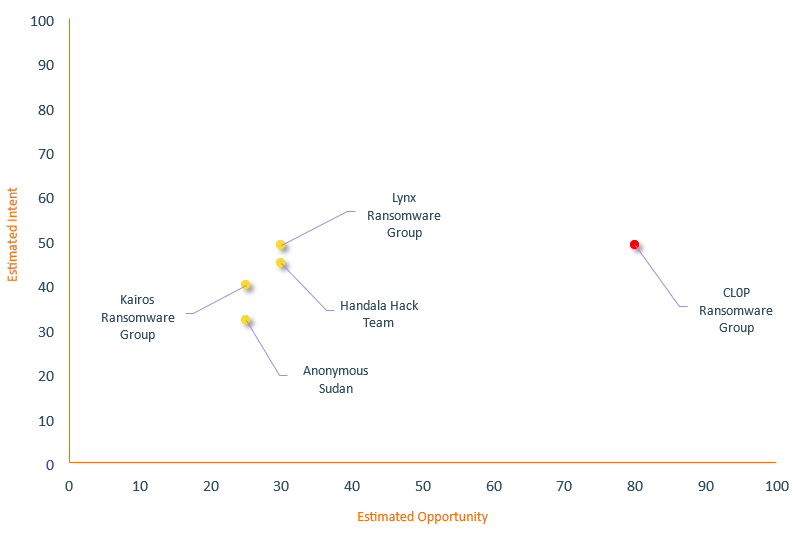
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| CL0P Ransomware Group | High | → | High | (80) | → 0 | (49) | ↑ 14 |
| Lynx Ransomware Group | Basic | → | Basic | (30) | → 0 | (49) | ↑ 9 |
| Handala Hack Team | Basic | → | Basic | (30) | → 0 | (45) | ↑ 5 |
| Kairos Ransomware Group | Basic | → | Basic | (25) | → 0 | (40) | ↑ 5 |
| Anonymous Sudan | Basic | → | Basic | (25) | → 0 | (32) | ↓ 5 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| UNC5337 | ▲ | Adware | ▲ | CVE-2024-49138 | ▲ | Hewlett Packard Enterprise Co. | ▲ |
| TAG-110 (UAC-0063) | ▲ | Zero Day Exploit | ▲ | CVE-2022-21894 | ▲ | Trump Media & Technology Group | ▲ |
| RansomHouse Group | ▲ | Credential Stuffing | ▲ | CVE-2024-49113 | ▲ | Apple iTunes | ▲ |
| Revenants | ▲ | XWorm | ▲ | CVE-2020-2883 | ▲ | Cursor | ▲ |
| Nigerian Hackers | ▲ | Spear Phishing | ▲ | CVE-2024-53691 | ▲ | ▲ | |
Prominent Information Security Events
DigitalPulse Proxyware Distributed Through Advertising Pages.
Source: Insikt Group, AhnLab Security Emergency Response Center | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - 6607cf20ece3a804ac9c23d291c1139fef6d4591051dcb4232356f5b1a95b41f
IOC: MD5 - 08a5b638c95b7bf98182e35c9535cbf5
IOC: URL – hxxps[:]//a[.]pairnewtags[.]com/pid/s[.]js
IOC: URL - hxxps[:]//filerit[.]com/pi-240924[.]ps1
IOC: URL - hxxps[:]//raw[.]githubusercontent[.]com/Evastrea/5Ag3R4ObWH/main/GKPXAP[.]exe
On January 13, 2025, AhnLab Security Emergency Response Center (ASEC) reported that DigitalPulse proxyware is being distributed through advertising pages on freeware websites. This campaign uses AutoClicker, software that masquerades as a legitimate automatic mouse-clicker GUI embedded with malicious strings for downloader functionality, to download and install DigitalPulse. DigitalPulse would then hijack the victim's network bandwidth for external profit.
DigitalPulse has previously been implicated in proxyjacking campaigns, and was allegedly responsible for the infection of more than 400,000 Windows systems during 2023. The current campaign differentiates itself by signing DigitalPulse payloads with a certificate using the name "Netlink Connect"; however the underlying malware characteristics remain consistent with earlier instances.
DigitalPulse has reportedly been distributed in a recent campaign by enticing users to access freeware download pages, which redirect them to malvertising webpages where they would download AutoClicker. Technical analysis reveals that AutoClicker employs multiple anti-analysis measures, including:
- Analysing web browser history file sizes to ensure they reach a believable threshold
- Inspecting loaded DLLs for sandbox and security-related files
- Querying system firmware for strings associated with virtualised environments and debugging software
Lumma Stealer Campaign Using Fake CAPTCHAS To Run Malicious Scripts.
Source: Insikt Group, CERT-AGID | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - baa0f226181c0189354592ed8155b1b7081dfc056f3a2beca4ff335c86635734
IOC: SHA256 - 0567b98365f8f5e5a3adf508dc7234ea7b50270a8106c3a66a0da96f38058118
On January 13, 2025, CERT-AGID shared an exploitation method demonstrated by Lumma Stealer malware using fake CAPTCHA challenges. The attack begins with victims receiving phishing emails regarding alleged security vulnerabilities in their GitHub repositories, urging them to click on a malicious link.
This link redirects victims to a compromised legitimate Italian domain running an outdated version of WordPress. The attackers embedded a Base64-encoded JavaScript into the homepage of this domain, which generates a deceptive CAPTCHA challenge exclusively for visitors using Windows operating systems.
When victims interact with the CAPTCHA, they are instructed to execute a provided PowerShell script using the Windows Run function (WIN+R). The script, consisting of 10MB of obfuscated code, downloads and executes a payload from a remote server. The script employs anti-sandbox techniques to bypass detection in automated sandbox environments, requiring manual analysis to understand its operations. The decryption of the embedded Base64-encoded payload reveals another PowerShell script that eventually extracts the Lumma Stealer executable.
Lumma Stealer connects to ROT15-encoded C2 domains sourced from a Steam Community profile. Data gathered from the victim environment is exfiltrated to the C2 servers. This data includes credentials, wallets, and personal information and facilitates malware updates and additional payloads.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-55591 –
- FortiOS 7.0 - Upgrade to 7.0.17 or above
- FortiProxy 7.2 - Upgrade to 7.2.13 or above
- FortiProxy 7.0 - Upgrade to 7.0.20 or above
- CVE-2024-7344 – Install the provided Security Update/Monthly Rollup provided by Microsoft
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
