Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
PoC Exploit for 7-Zip Vulnerability CVE-2025-0411 - On January 22, 2025, a security researcher released a Proof-of-Concept (PoC) exploit for CVE-2025-0411 on GitHub. CVE-2025-0411 is a Mark-of-the-Web (MotW) Security Bypass flaw that affecting 7-Zip versions 24.08 and earlier. MotW is a Windows security feature that detects files originating from untrusted sources.
SonicWall RCE Vulnerability, CVE-2025-23006, Exploited as Zero-Day - On January 22, 2025, SonicWall disclosed a critical pre-authentication deserialisation vulnerability CVE-2025-23006 in its Secure Mobile Access (SMA) 1000 series Appliance Management Console (AMC) and Central Management Console (CMC). SonicWall has received reports of active exploitation of this flaw as a zero-day in active attacks.
CISA Warn of Threat Actors Still Actively Exploiting Four Patched Ivanti Vulnerabilities - On January 22, 2025, The Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) reported that threat actors are still actively exploiting four Ivanti Vulnerabilities. The vulnerabilities affect Ivanti Cloud Service Appliance (CSA) version 4.6x (prior to build 519) and CSA version 5.0.1 and below.
Potential Threats
Threat Actors Abuses Bing Ads in Malvertising Campaign to Distribute Malware - On January 23, 2025, Palo Alto Network’s Unit 42 reported a malvertising campaign wherein threat actors targeted Microsoft Teams users with Bing advertisements. The malicious advertisements promoted a fake Microsoft Teams website to deploy malware on Windows systems.
Two Ransomware Campaigns Using Email Bombing, Microsoft Teams Vishing - On January 21, 2025, Sophos X-Ops identified two ransomware campaigns they are tracking as two threat groups, STAC5143 and STAC5777, that exploit Microsoft Office 365 features to infiltrate organisations. STAC5143 and STAC5777 gain initial access through email bombing, fake tech support, social engineering, and legitimate Office 365 services like Teams and Quick Assist.
Qakbot Returns With New BackConnect Module - On January 20, 2025, security researchers Joshua Platt, Jason Reaves, and Jonathan McCay published a write-up detailing the resurgence of Qakbot, a modular information-stealing malware active since 2007. According to the researchers, despite the takedown of Qakbot’s operation in May 2024, Qakbot operators resumed activity with new techniques and capabilities, such as a new BackConnect malware module.
General News
Five Indicted in US for Supporting North Korea Through IT Worker Scheme - On January 23, 2025, the United States Department of Justice disclosed the indictment of five people in a conspiracy to employ North Korean citizens as remote information technology workers for American firms. The group operated US-based laptop farms using employer-provided devices to trick companies into believing they had hired a US absed worker.
LinkedIn sued for allegedly training AI models with private messages without consent - LinkedIn Premium customers are suing the social media platform, alleging that it shared their private messages with third parties without their consent in order to train artificial intelligence models. Last August, LinkedIn “ostensibly” offered users the ability to enable a new privacy feature dictating whether their personal data could be shared, but turned permissions on by default, alleges the proposed class action lawsuit, filed in a California federal court.
PayPal penalised $2 million over data breach involving 35K Social Security numbers - Digital payments giant PayPal will pay a $2 million penalty after a December 2022 cybersecurity incident that leaked thousands of Social Security numbers, New York state regulators said Thursday.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
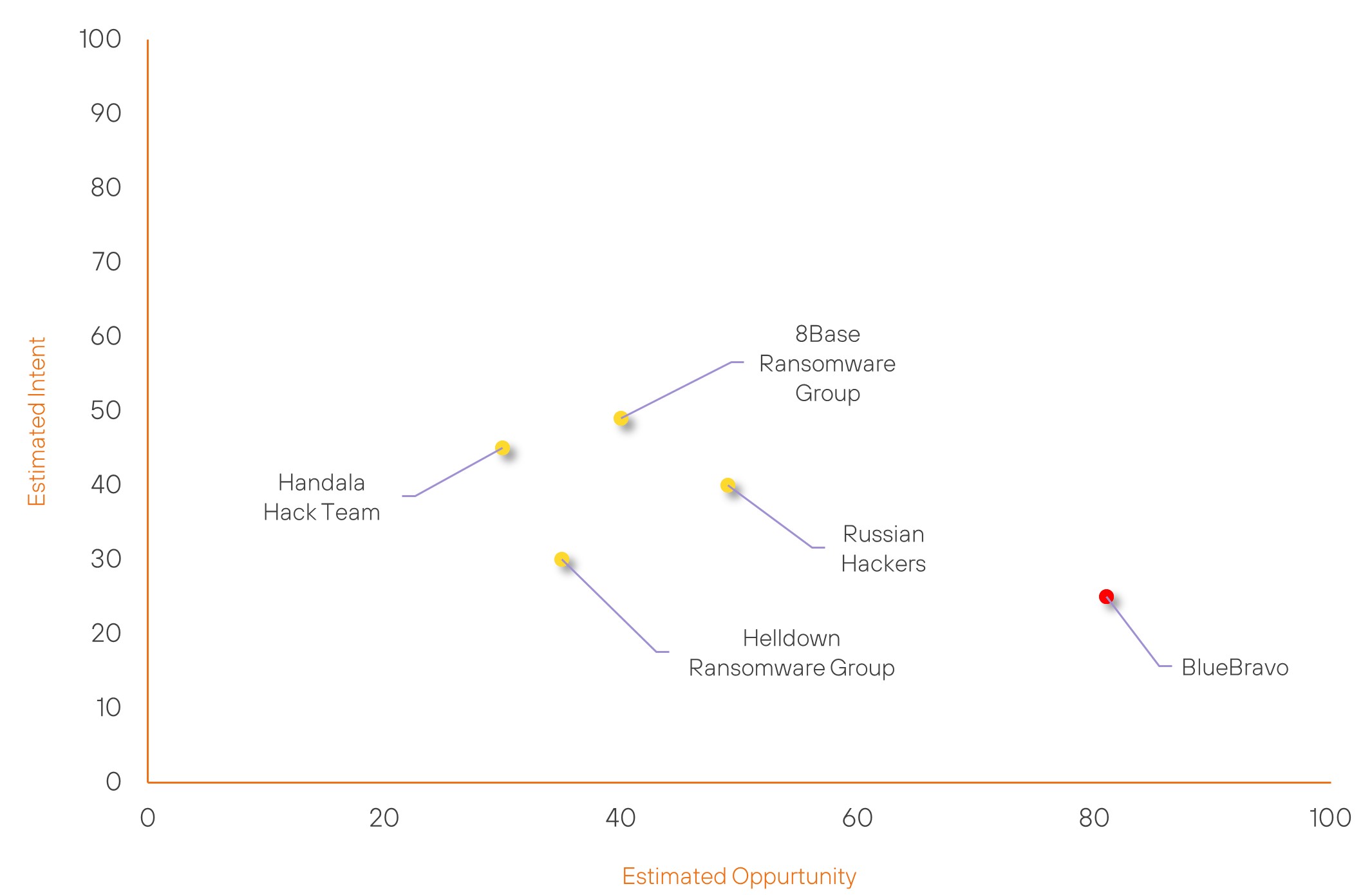
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| BlueBravo | High | → | High | (81) | → 0 | (25) | ↓ 5 |
| 8Base Ransomware Group | Basic | → | Basic | (40) | ↑ 5 | (49) | → 0 |
| Russian Hackers | Basic | → | Basic | (49) | → 0 | (40) | ↓ 5 |
| Handala Hack Team | Basic | → | Basic | (30) | → 0 | (45) | ↑ 5 |
| Helldown Ransomware Group | Basic | → | Basic | (35) | ↑ 5 | (30) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| APT33 | ▲ | Shamoon Wiper (Disttrack) | ▲ | CVE-2014-0160 (Heartbleed) | ▲ | TalkTalk Telecom Group | ▲ |
| UNC5337 | ▲ | Botnet | ▲ | CVE-2025-0411 | ▲ | Sony Group Corp | ▲ |
| Handala Hack Team | ▲ | Spear Phishing | ▲ | CVE-2025-21333 | ▲ | Insurance | ▲ |
| Iranian Hackers | ▲ | FireScam | ▲ | CVE-2024-3400 | ▲ | Strava | ▲ |
| Revenants | ▲ | PNGPlug | ▲ | CVE-2025-20128 | ▲ | Slashdot | ▲ |
Prominent Information Security Events
Two Ransomware Campaigns Using Email Bombing, Microsoft Teams Vishing.
Source: Insikt Group, Sophos X-Ops | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - ea2b3bf32cc27e959e19c365fa2f6e5310ef2e76d3d0ed2df3fb5945f9afc9e7
IOC: SHA256 - 8abc8c92ebfe78f54e7488a467d1b6e90d28382067b49a954e31133691112eba
IOC: IP – 195.123.241[.]24:443
On January 21, 2025, Sophos X-Ops identified two ransomware campaigns they are tracking as two threat groups, STAC5143 and STAC5777, that exploit Microsoft Office 365 features to infiltrate organisations. STAC5143 and STAC5777 gain initial access through email bombing, fake tech support, social engineering, and legitimate Office 365 services like Teams and Quick Assist.
STAC5143 begins its attack with email bombing and a fake Teams call from an account impersonating IT support to create a sense of urgency for the victim. Once access is granted, attackers use Teams' remote desktop control feature to open a command shell and deploy and execute Java-based malware and deploy Python payloads like RPivot backdoors. They establish command-and-control (C2) via ProtonVPN with DLL side-loading, enabling network reconnaissance and credential theft. Sophos notes that this activity overlaps with Storm-1811, and assesses there is a possible link between this activity and the FIN7 threat group.
STAC5777, which overlaps with Storm-1811, initiates a similar entry point with email bombing and social engineering through Teams but guides victims to install Microsoft Quick Assist to gain remote control. The group used web browsers to download different malicious compressed files and payloads in an archived directory. The threat actor then uncompressed the files into the OneDrive update folder, which contained malicious files that were then deployed using the legitimate OneDriveStandaloneUpdater[.]exe. After establishing command and control (C2) through VPS-hosted IPs, they perform network discovery, move laterally via VPN, RDP, and WinRM, and attempt to disable endpoint protection and multifactor authentication (MFA)
Qakbot Returns With New BackConnect Module.
Source: Insikt Group, Walmart Global Tech | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: SHA256 - 22c5858ff8c7815c34b4386c3b4c83f2b8bb23502d153f5d8fb9f55bd784e764
IOC: SHA256 - 98d38282563c1fd09444724eacf5283626aeef36bcb3efa9d7a667db7314d81f
IOC: Domain - upd5[.]pro
On January 20, 2025, security researchers Joshua Platt, Jason Reaves, and Jonathan McCay published a write-up detailing the resurgence of Qakbot, a modular information-stealing malware active since 2007. According to the researchers, despite the takedown of Qakbot’s operation in May 2024, Qakbot operators resumed activity with new techniques and capabilities, such as a new BackConnect malware module.
Based on the write-up, the researchers analysed a DLL file (PixelSignal.dll) associated with Zloader and hosted on the domain vector123[.]xyz, which resolved to the IP address 80.66.89[.]100. According to the researchers, 80.66.89[.]100 hosted a ZIP archive named “pack.dat”. Additionally, they identified a second IP address (146.19.128[.]138) hosting the same ZIP archive. At the time of writing, both IP addresses return an error message.
The legitimate OneDriveStandaloneUpdater.exe sideloaded the malicious winhttp.dll, which then decrypted settingsbackup.dat using the RC4 algorithm with a hard-coded key. The researchers identified the decrypted PE file as the new BackConnect (BC) module.
According to the researchers, Qakbot’s new BC module shows ties to the BlackBasta ransomware operations due to overlapping infrastructure.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2025-0411 – Upgrade to 7-Zip version 24.09 or later.
- CVE-2025-23006 – Update SMA1000 firmware to version 12.4.3-02854 and higher
- Ivanti CVE’s –
- CVE-2024-8963 - Upgrade the Ivanti CSA 4.6 to CSA 5.0. CSA 4.6 Patch 518 customers may also update to Patch 519. But as this product has entered End-of-Life, the strongly recommended path is to upgrade to CSA 5.0. Customers already on CSA 5.0 do not need to take any further action.
- CVE-2024-9379 - Upgrade to CSA 5.0.2
- CVE-2024-8190 - Upgrade the Ivanti CSA 4.6 to CSA 5.0. CSA 4.6 Patch 518 customers may also update to Patch 519. But as this product has entered End-of-Life, the preferred path is to upgrade to CSA 5.0. Customers already on CSA 5.0 do not need to take any further action.
- CVE-2024-9380 - Upgrade to CSA 5.0.2
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
