Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Velvet Ant Exploits CVE-2024-20399 in Cisco Nexus Switch Devices - The Chinese threat group known as Velvet Ant exploited a zero-day vulnerability, tracked as CVE-2024-20399, in Cisco NX-OS Software to deploy an unspecified malware on the switches of victim entities, according to Sygnia’s July 1, 2024 report. Cisco has patched an NX-OS zero-day exploited in April attacks to install previously unknown malware as root on vulnerable switches.
Remote Code Execution Vulnerability in Ghostscript Exploited – CVE-2024-29510 is described as a format string injection in the uniprint device, the security defect could allow an attacker to bypass the -dSAFER sandbox and execute code remotely. Codean Labs recommends updating to the latest version if Ghostscript is in use.
Critical CocoaPods Flaws Exposed Apps to Supply Chain Attacks – On July 1, 2024, E.V.A Information Security identified two critical-severity vulnerabilities and one high-severity vulnerability in CocoaPods, a dependency manager tool used for managing third-party libraries in Swift and Objective-C projects for iOS and MacOS applications.
Potential Threats
Hackers abused API to verify millions of Authy MFA phone numbers - Twilio has confirmed that an unsecured API endpoint allowed the verification of the phone numbers of millions of Authy multi-factor authentication users, potentially putting them at risk of SMS phishing and SIM swapping attacks. In late June, the threat group “ShinyHunters” leaked a CSV file containing what they claim are 33 million phone numbers registered with the Authy service.
New Eldorado RaaS Targets VMware ESXi, Linux, and Windows - As of June 2024, a new Ransomware-as-a-Service (RaaS) model known as Eldorado has claimed sixteen victims. First launched and promoted by a Russian threat actor named “$$$” on the dark web market Ramp Forum in March 2024, Eldorado targets VMware ESXi, Linux, and Windows systems.
BlueDelta Employs Outlook-Themed Credential Harvesting Page - On July 2nd, 2024, Insikt researchers detected a new BlueDelta credential harvesting page registered and hosted using the free hosting company InfinityFree. The webpage, themed to impersonate a Microsoft Outlook login portal, displayed a form to capture victims' email credentials and forward them to a PHP script. Once the form is submitted, the webpage redirects the victim to the legitimate mail server login page, masking the credential capture from the victim.
General News
NCA and Global Partners Take Down 593 Unauthorized Cobalt Strike Instances - The National Crime Agency (NCA) led an international operation that disrupted multiple instances of unauthorised use involving Cobalt Strike, such as cracked and/or pirated versions of it.
MikroTik Botnet Caused Record Breaking DDoS Attack on OVH Cloud - On July 2, 2024, French cloud computing company OVHcloud reported that it mitigated a record-breaking distributed denial of service (DDoS) attack that peaked at 840 million packets per second (Mpps).
Cloudflare DNS Service Disruption – Over 300 networks in 70 countries experienced disruptions to the Cloudflare DNS resolver service 1.1.1.1 due to a Border Gateway Protocol (BGP) hijacking incident and a subsequent route leak.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
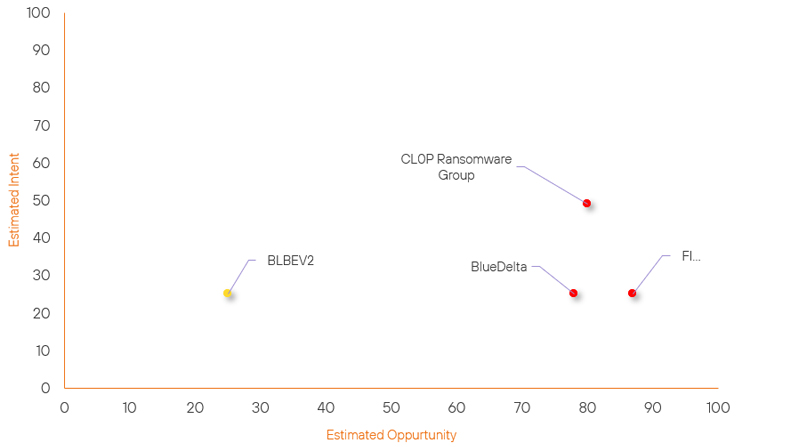
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| BLBEV2 | New | → | Basic | ↑ 25 | (25) | ↑ 25 | (25) |
| BlueDelta | High | → | High | ↑ 1 | (78) | → 0 | (25) |
| CL0P Ransomware Group | High | → | High | ↓ 2 | (80) | → 0 | (49) |
| FIN7 | High | → | High | → 0 | (87) | ↓ 5 | (25) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Stormous Ransomware Group | ▲ | Keylogger | ▲ | CVE-2024-36401 | ▲ | OpenAI | ▲ |
| ShinyHunters | ▲ | Malicious Link | ▲ | CVE-2024-27292 | ▲ | Roblox | ▲ |
| HUNT3R | ▲ | BianLian | ▲ | CVE-2024-2408 | ▲ | Authy Inc. | ▲ |
| Medusa Ransomware Group (Frozen Spider) | ▲ | Disinformation | ▲ | CVE-2024-21412 | ▲ | eCommerce | ▲ |
| Volcano Demon | ▲ | Malicious Code | ▲ | CVE-2024-6387 (regreSSHion) | ▲ | Hotels and entertainment services | ▲ |
Prominent Information Security Events
Vulnerabilities in CocoaPods Could Lead to Supply Chain Attacks.
Source: Insikt Group, EVA Information Security | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-38368| CVVS Score: 9.3 | Recorded Future Risk Score: High - 79
CVE-2024-38366| CVVS Score: 10.0 | Recorded Future Risk Score: High – 79
On July 1, 2024, E.V.A Information Security identified two critical-severity vulnerabilities and one high-severity vulnerability in CocoaPods, a dependency manager tool used for managing third-party libraries in Swift and Objective-C projects for iOS and MacOS applications. At the time of writing, there have been no reports of these vulnerabilities being exploited in the wild.
The first vulnerability, CVE-2024-38368, is an authorisation flaw arising from improper validation of ownership claims. Exploitation could allow threat actors to assert ownership over unclaimed software packages. This could lead to the injection of malicious code into the source code of iOS and macOS applications that rely on these packages.
The second vulnerability, tracked as CVE-2024-38366, is a remote code execution (RCE) flaw arising from an insecure email verification process. Exploitation could enable threat actors to execute arbitrary code on the Trunk server, potentially leading to manipulation of packages.
CocoaPods was first developed and released in 2011. Its current issues can be traced to 2014 when it replaced its GitHub-based authentication system with a new "Trunk" server, which also doubled as the platform's centralised repository and distribution platform. Though this change promised benefits to security, scalability, and developer quality of life, the migration process wasn’t smooth, and one outcome was that ownership over all pods was reset.
"As part of the integration, some APIs were exposed, including the Web page, to let business owners that were authenticated via their GitHub account claim their own pods," recalls Reef Spektor, E.V.A vice president of research. Essentially users reclaimed their pods by simply calling dibs.
Many authors didn't reclaim their pods at all, leaving thousands of dependencies "orphaned." Over time, more were abandoned as authors reneged on their ownership. Thousands of pods remain ownerless today, and the public API endpoint for claiming pods was still accessible until 2023. Anyone in possession of this knowledge could have at any point from 2014 to 2023, claimed anyone else's pod for themselves, modified it however they wished, and pushed that modification to any Apple apps that use it.
There has been no evidence that attackers have exploited any of the issues uncovered by the researchers and patched by CocoaPods in October.
Eldorado Ransomware-as-a-Service.
Source: Insikt Group, Group-IB | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: SHA256: dc4092a476c29b855a9e5d7211f7272f04f7b4fca22c8ce4c5e4a01f22258c33
IOC: SHA256: b2266ee3c678091874efc3877e1800a500d47582e9d35225c44ad379f12c70de
IOC: SHA256: cb0b9e509a0f16eb864277cd76c4dcaa5016a356dd62c04dff8f8d96736174a7
IOC: SHA256: 7f21d5c966f4fd1a042dad5051dfd9d4e7dfed58ca7b78596012f3f122ae66dd
IOC: SHA256: 1375e5d7f672bfd43ff7c3e4a145a96b75b66d8040a5c5f98838f6eb0ab9f27b
IOC: IP: 173[.]44[.]141[.]152
A new Ransomware-as-a-Service (RaaS) model known as Eldorado has claimed sixteen victims across the US, Italy, and Croatia, as of June 2024. Eldorado targets VMware ESXi, Linux, and Windows systems. According to a Group-IB report on July 3, 2024, Eldorado was developed independently of any previously leaked source codes.
Eldorado was developed using the Go programming language to ensure cross-platform functionality. It employs the ChaCha20 algorithm to encrypt files and Rivest Shamir Adleman-Optimal Asymmetric Encryption Padding (RSA-OAEP) to encrypt private keys. Eldorado can encrypt data on network shares using the SMB protocol and delete shadow volume copies on Windows to hinder data recovery efforts. It also selectively avoids encrypting files with extensions such as DLL, LNK, SYS, and EXE, as well as critical system directories to ensure that the infected systems remain operational.
Group-IB has observed that most Eldorado attacks targeted real estate organisations, followed by the education, healthcare, and manufacturing sectors.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- Ghostscript – Update to the latest version.
- Cisco Nexus – Apply the latest update from Cisco to the impact devices.
We also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
