Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Microsoft Patch Tuesday: Two New Actively Exploited Vulnerabilities - On July 9, 2024, Microsoft patched 142 vulnerabilities in its products and services, including the following actively exploited CVEs tracked as CVE-2024-38080 and CVE-2024-38112. Both vulnerabilities were patched in the latest security update.
GitLab CVE-2024-6385 – GitLab warned today that a critical vulnerability in its product's GitLab Community and Enterprise editions allows attackers to run pipeline jobs as any other user. The flaw patched in today's security update is tracked as CVE-2024-6385.
Vulnerability in RADIUS Protocol Allows Unauthorized Access – A critical vulnerability in the InkBridge Remote Authentication Dial-In User Service (RADIUS) protocol, tracked as CVE-2024-3596, allows threat actors to authenticate unauthorised users to local networks and bypass multi-factor authentication.
Potential Threats
Malicious APK File Impersonating Banco Santander - On July 10, 2024, security researcher Germán Fernández shared a sample of a malicious Android application package (APK) impersonating Banco Santander on MalwareBazaar. Banco Santander, also known as Santander Group, is a major financial services company headquartered in Spain.
New FishXProxy Phishing Kit Discovered - FishXProxy, a new phishing toolkit, lowers the barrier to conducting sophisticated phishing attacks, as reported by SlashNext Security on July 11, 2024. FishXProxy offers a complete solution for creating and managing phishing sites that are accessible even to those with minimal technical skills. FishXProxy includes advanced features such as antibot configurations, Cloudflare Turnstile integration, a built-in redirector, and page expiration settings.
WordPress calendar plugin Targeted - Hackers are trying to exploit a vulnerability in the Modern Events Calendar WordPress plugin on more than 150,000 websites to upload arbitrary files to a vulnerable site and execute code remotely. The vulnerability exploited is identified as CVE-2024-5441 and received a CVSS score of 8.8
General News
Breach of AT&T Customer Data Part of Ongoing Compromises of Snowflake Customer Instances - According to an advisory on July 12, 2024, AT&T revealed that it had discovered a breach of its data in April 2024 that involved data being illegally downloaded from a third-party platform, which the company later confirmed to CNN to be Snowflake.
Customer Data Exposed Following Fujitsu Cyberattack - On July 9, 2024, Japanese information and communications technology (ICT) company Fujitsu notified customers of a cyberattack that compromised personal and business data.
Hackers use PoC exploits in attacks 22 minutes after release – Threat actors rapidly weaponise proof-of-concept (PoC) exploits, sometimes within 22 minutes of their public release. This is according to Cloudflare's 2024 Application Security report, which covers activity from May 2023 to March 2024 and highlights emerging threat trends.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
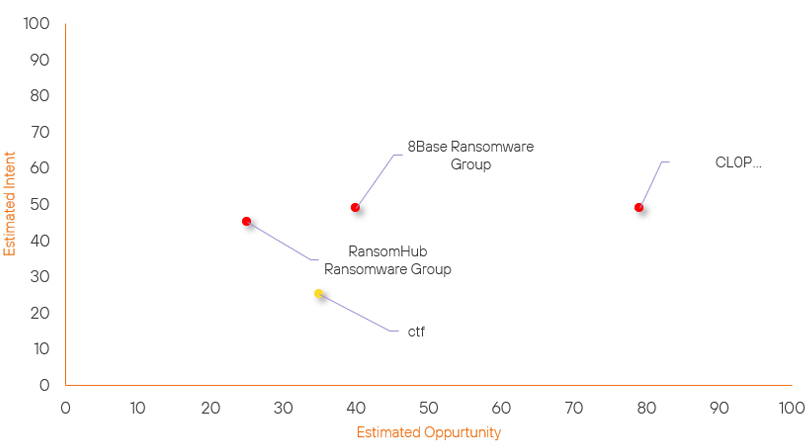
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| ctf | New | → | Basic | ↑ 35 | (35) | ↑ 25 | (25) |
| RansomHub Ransomware Group | Basic | → | Basic | → 0 | (25) | ↑ 10 | (45) |
| 8Base Ransomware Group | Basic | → | Basic | ↑ 5 | (40) | → 0 | (49) |
| CL0P Ransomware Group | High | → | High | ↓ 1 | (79) | → 0 | (49) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| NullBulge | ▲ | RansomHub Ransomware | ▲ | CVE-2024-38112 | ▲ | Data Centers | ▲ |
| Lazarus Group | ▲ | DNS Redirection | ▲ | CVE-2024-6387 (regreSSHion) | ▲ | Internet Hosting | ▲ |
| OilAlpha | ▲ | Zero Day Exploit | ▲ | CVE-2024-27198 | ▲ | AT&T | ▲ |
| Handala | ▲ | Domain Hijacking | ▲ | CVE-2024-39929 | ▲ | Walt Disney | ▲ |
| ShinyHunters | ▲ | SSH-Snake | ▲ | CVE-2023-50164 | ▲ | Evolve Bank & Trust | ▲ |
Prominent Information Security Events
GitLab CVE-2024-6385.
Source: Insikt Group, GitLab | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-6385| CVVS Score: 9.6 | Recorded Future Risk Score: High – 79
GitLab released security patches on July 10, 2024, to address vulnerabilities in the Community Edition (CE) and Enterprise Edition (EE) versions 17.1.2, 17.0.4, and 16.11.6 and advised all admins to upgrade all installations immediately.
"We strongly recommend that all installations running a version affected by the issues described below are upgraded to the latest version as soon as possible," it warned. "GitLab.com and GitLab Dedicated are already running the patched version."
This vulnerability impacts all GitLab CE/EE versions from 15.8 to 16.11.6, 17.0 to 17.0.4, and 17.1 to 17.1.2. Under certain circumstances that GitLab has yet to disclose, attackers can exploit it to trigger a new pipeline as an arbitrary user. GitLab pipelines are a Continuous Integration/Continuous Deployment (CI/CD) system feature that lets users automatically run processes and tasks in parallel or sequentially to build, test, or deploy code changes.
GitLab also patched a similar bug late last month (CVE-2024-5655, CVSS score: 9.6) that could also be weaponised to run pipelines as other users.
Microsoft Patch Tuesday Actively Exploited Vulnerabilities.
Source: Insikt Group, Microsoft, CheckPoint | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
CVE-2024-38080| CVVS Score: 7.8 | Recorded Future Risk Score: Critical - 99
CVE-2024-38112| CVVS Score: 9.6 | Recorded Future Risk Score: Critical – 99
On July 9, 2024, Microsoft patched 142 vulnerabilities in its products and services, including the following actively exploited CVEs tracked as CVE-2024-38080 and CVE-2024-38112.
CVE-2024-38080 is an elevation of privilege flaw affecting Windows Hyper-V. Successful exploitation allows threat actors to execute arbitrary code with SYSTEM-level permissions, leading to system compromise.
CVE-2024-38112 is a spoofing flaw affecting Windows Microsoft HTML (MSHTML) platform. Successful exploitation requires the victim to execute a malicious file crafted by the threat actor, enabling them to manipulate the target environment. This manipulation leads to the spoofing of content and gaining unauthorised access to sensitive user information.
Both of the actively exploited vulnerabilities above have been patched in the latest security update. As a result of their disclosure, we have tracked a significant spike in mentions of both vulnerabilities, which may lead to an increase in attempts to utilise this vulnerability.
On July 9, 2024, Check Point Research (@_CPResearch_ on X, formerly known as Twitter) published a write-up detailing a new campaign in which threat actors exploited CVE-2024-38112 to execute remote code on Windows systems.
According to Check Point Research’s write-up, the infection chain begins with a victim receiving a malicious Internet Shortcut file (.url) disguised as a link to a PDF file. When the victim opens the .url file, it launches Internet Explorer instead of a modern browser like Chrome or Edge, redirecting to a threat actor-controlled site using the multipart HTML document prefix “mhtml”. This prefix makes the URL appear legitimate despite containing hidden characters that lead to a malicious .hta file. When the victim attempts to open the file, believing it to be a PDF, it downloads and executes the malicious .hta file. This allows threat actors to exploit Internet Explorer’s vulnerabilities and achieve remote code execution (RCE) on the victim’s machine.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- Microsoft – Apply the latest Security Updates
- GitLab – Apply the latest patch to vulnerable versions where applicable
We also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
