Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
PHP Addresses Critical CVE – On June 6, 2024, the PHP development team addressed a critical remote code execution (RCE) vulnerability affecting all PHP versions for Windows. This vulnerability, tracked as CVE-2024-4577, was discovered on May 7, 2024.
Google Addresses 37 Vulnerabilities in Android – On June 3, 2024, Google addressed 37 security vulnerabilities affecting Android devices. These vulnerabilities span various components, including the Framework, System, Kernel, Arm, Imagination Technologies, MediaTek, and Qualcomm closed-source components. Google reported no active exploitation of these vulnerabilities in the wild.
CVE-2024-0099 allows Buffer Overflow affecting NVIDIA GPU Display Driver – NVIDIA vGPU software for Linux contains a vulnerability in the Virtual GPU Manager, where the guest OS could cause buffer overrun in the host. A successful exploit of this vulnerability might lead to information disclosure, data tampering, escalation of privileges, and denial of service.
Potential Threats
High-Severity Azure Service Tag Vulnerability Enables Firewall Bypass - On June 3, 2024, Tenable reported a vulnerability in Azure's use of Service Tags, which allows threat actors to bypass firewall rules by forging requests from trusted services. This vulnerability affects multiple Azure services, including Application Insights, DevOps, Machine Learning, and Logic Apps.
Write-up and PoC for Privilege Escalation Vulnerability in macOS PackageKit Framework – On June 3, 2024, software developer Mykola Grymalyuk (@khronokernel) published a write-up and proof-of-concept (PoC) script for CVE-2024-27822. This is a privilege escalation vulnerability affecting Apple’s PackageKit.framework , which manages software packages on macOS systems.
New Linux Variant of TargetCompany Ransomware Targets VMware ESXi - On June 5, 2024, Trend Micro reported that a new Linux variant of TargetCompany ransomware targeting VMware ESXi. The new variant first checks if it runs in a VMware ESXi environment by executing the uname command. If the system name matches vmkernel, it encrypts files with specific VM-related extensions.
General News
Microsoft reverses course, makes Recall feature opt-in - Microsoft announced changes on Friday to its controversial Recall feature that will allow users to proactively opt-in to the tool before it is activated on devices. Recall allows the company’s new line of Windows 11 Copilot+ devices to screenshot every action a person takes on their PC.
New York Times source code stolen using exposed GitHub token - Internal source code and data belonging to The New York Times was leaked on the 4chan message board after being stolen from the company's GitHub repositories in January 2024.
UNC5537 Targets Snowflake Customer Instances – On June 10th, Mandiant published a new report in relation to the recent suspected Snowflake breaches. While initially, reports suggested the breaches occurred due to a breach of Snowflake's enterprise environment. Mandiant has since reported that every incident they investigated that was associated with this campaign was traced back to compromised customer credentials. These attacks targeted accounts that did not have MFA enabled.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
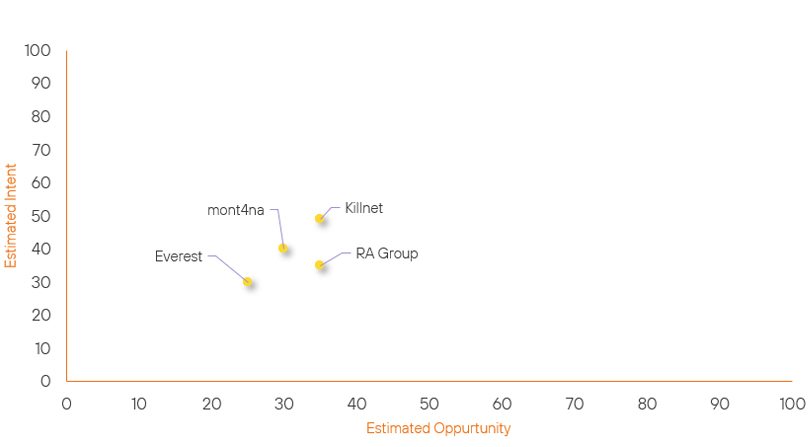
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Everest | New | → | Basic | ↑ 25 | (25) | ↑ 30 | (30) |
| mont4na | Basic | → | Basic | → 0 | (30) | ↑ 5 | (40) |
| Killnet | Basic | → | Basic | → 0 | (35) | ↑ 4 | (49) |
| RA Group | Basic | → | Basic | ↓ 5 | (35) | → 0 | (35) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| INC RANSOM | ▲ | Disinformation | ▲ | CVE-2024-4577 | ▲ | The New York Times Company | ▲ |
| Russian Hackers | ▲ | Cryptojacking | ▲ | CVE-2024-29849 | ▲ | Kadokawa | ▲ |
| HUNT3R | ▲ | Network Denial of Service | ▲ | CVE-2012-1823 | ▲ | Luxury Goods | ▲ |
| ShinyHunters | ▲ | Fog Ransomware | ▲ | CVE-2024-30043 | ▲ | CoinGecko | ▲ |
| HackNet | ▲ | OS Command Injection | ▲ | CVE-2024-24919 | ▲ | GitHub | ▲ |
Prominent Information Security Events
Google Addresses 37 Vulnerabilities.
Source: Android, Insikt Group | Vulnerability Intelligence from Insikt Group
Intelligence Cards: Intelligence & Reports
On June 3, 2024, Google addressed 37 security vulnerabilities affecting Android devices. These vulnerabilities span various components, including the Framework, System, Kernel, Arm, Imagination Technologies, MediaTek, and Qualcomm closed-source components.
Google reported no active exploitation of these vulnerabilities in the wild. A list of the respective vulnerabilities can be seen below:
Framework Vulnerabilities:
CVE-2023-21266 (High-Severity) - Elevation of Privilege (EoP)
CVE-2024-31310 (High-Severity) - EoP
CVE-2024-31312 (High-Severity) - Information Disclosure (ID)
CVE-2024-31314 (High-Severity) - Denial of Service (DoS)
CVE-2024-31316 (High-Severity) - EoP
CVE-2024-31317 (High-Severity) - EoP
CVE-2024-31318 (High-Severity) - EoP
CVE-2024-31319 (High-Severity) - EoP
CVE-2024-31322 (High-Severity) - EoP
CVE-2024-31324 (High-Severity) - EoP
CVE-2024-31325 (High-Severity) - EoP
CVE-2024-31326 (High-Severity) – EoP
Framework Vulnerabilities:
CVE-2023-21266 (High-Severity) - Elevation of Privilege (EoP)
CVE-2024-31310 (High-Severity) - EoP
CVE-2024-31312 (High-Severity) - Information Disclosure (ID)
CVE-2024-31314 (High-Severity) - Denial of Service (DoS)
CVE-2024-31316 (High-Severity) - EoP
CVE-2024-31317 (High-Severity) - EoP
CVE-2024-31318 (High-Severity) - EoP
System Vulnerabilities:
CVE-2023-21113 (High-Severity) - EoP
CVE-2023-21114 (High-Severity) - EoP
CVE-2024-31311 (High-Severity) - EoP
CVE-2024-31313 (High-Severity) - EoP
CVE-2024-31315 (High-Severity) - EoP
CVE-2024-31323 (High-Severity) - EoP
CVE-2024-31327 (High-Severity) - EoP
Kernel Vulnerability:
CVE-2024-26926 (High-Severity) - EoP
Arm Components:
CVE-2024-0671 (High-Severity) - Mali
CVE-2024-1065 (High-Severity) - Mali
Imagination Technologies:
CVE-2024-23695 (High-Severity) - PowerVR-GPU
CVE-2024-23696 (High-Severity) - PowerVR-GPU
CVE-2024-23697 (High-Severity) - PowerVR-GPU
CVE-2024-23698 (High-Severity) - PowerVR-GPU
CVE-2024-23711 (High-Severity) - PowerVR-GPU
MediaTek Components:
CVE-2024-20065 (High-Severity) - Telephony
CVE-2024-20066 (High-Severity) - Modem
CVE-2024-20067 (High-Severity) - Modem
CVE-2024-20068 (High-Severity) - Modem
CVE-2024-20069 (High-Severity) - Modem
Qualcomm Closed-Source Components:
CVE-2023-43538 (Critical-Severity) - Closed-source Component
CVE-2023-43542 (High-Severity) - Closed-source Component
CVE-2023-43551 (Critical-Severity) - Closed-source Component
CVE-2023-43556 (Critical-Severity) - Closed-source Component
CVE-2024-23363 (High-Severity) - Closed-source Component
The above CVEs impact the Android version from 12 (including 12L) up to version 14. Google has recommended that devices be updated to the latest security patch as soon as possible.
CVE-2024-4577 – PHP Windows.
Source: Insikt Group, PHP, ShadowServer | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
CVE-2024-4577 | CVVS Score: 9.8 | Recorded Future Risk Score: High – 79
On June 6, 2024, the PHP development team addressed a critical remote code execution (RCE) vulnerability affecting all PHP versions for Windows. This vulnerability, tracked as CVE-2024-4577, was discovered by on May 7, 2024.
This vulnerability allows threat actors to execute arbitrary code on remote PHP servers via an argument injection attack. PHP is a popular web development language widely used on Windows and Linux servers.
The Shadowserver Foundation has detected multiple IP addresses scanning for vulnerable servers. Currently, there have been no reports of the CVE-2024-4577 vulnerability being exploited in the wild. Due to the increase in mentions regarding this vulnerability, we may start to see further attempts to exploit this.
We recommend upgrading to the latest PHP patch versions: PHP 8.3.8, PHP 8.2.20, and PHP 8.1.29 as soon as possible.
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular, we would like to highlight and recommend applying the following patches should they apply:
- PHP – Update to the latest patch versions listed above.
- Android – Apply the latest security update for the impacted versions of Android and impacted devices.
- Azure – Evaluate the usage of Service Tags within the impacted services.
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing these searching and hunting activities within your environment.
