Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Microsoft Patches Zero-Click Outlook Vulnerability – One of the vulnerabilities that Microsoft addressed as part of its June 2024 Patch Tuesday allowed for remote code execution (RCE) without user interaction. This security defect allows attackers to bypass Outlook registry block lists and create malicious DLL files, Microsoft says in its advisory. Outlook 2016, Office LTSC 2021, 365 Apps for Enterprise, and Office 2019 are affected.
Critical Vulnerability in Veeam Recovery Orchestrator – On June 13, 2024, security researcher Sina Kheirkhah published a write-up and proof-of-concept (PoC) tool for CVE-2024-29855. CVE-2024-29855 is a critical vulnerability in Veeam Recovery Orchestrator (VRO) that allows unauthenticated threat actors to gain administrative access to the VRO web UI.
Fortinet Patches Code Execution Vulnerability in FortiOS – Fortinet announced patches for multiple vulnerabilities in FortiOS and other products, including several flaws leading to code execution. The most severe of the issues is CVE-2024-23110 (CVSS score of 7.4), which collectively tracks multiple stack-based buffer overflow security defects in the platform’s command line interpreter.
Potential Threats
Ransomware Group Exploits PHP Vulnerability - On June 10, 2024, cybersecurity firm Imperva published a write-up detailing a threat actor exploiting CVE-2024-4577 to deliver TellYouThePass ransomware. CVE-2024-4577 is a critical remote code execution (RCE) vulnerability affecting Windows-based PHP installations with Common Gateway Interface (CGI) mode enabled.
Phishing Campaign Deploys WARMCOOKIE Windows Backdoor Using Job Recruitment Lures – Since late April 2024, phishing campaigns have used job and recruitment-themed lures to deploy a newly identified backdoor called WARMCOOKIE. Elastic Security Labs reported on the campaigns on June 12, 2024, noting while WARMCOOKIE is a relatively simple malware, it can be used to perform reconnaissance and deploy additional payloads on infected systems.
JetBrains Patches CVE-2024-37051, Affecting all IntelliJ-Based IDEs - On June 11, 2024, JetBrains patched a critical-severity vulnerability, tracked as CVE-2024-37051, affecting its IntelliJ-based integrated development environments (IDEs) versions 2023.1 and later.
General News
Black Basta ransomware gang may have exploited Windows flaw before it was patched - The group operating the notorious Black Basta ransomware may have exploited a recently patched Windows vulnerability as a zero-day, researchers have found.
Microsoft Delaying Recall Feature to Improve Security - Microsoft has decided to postpone the launch of the Windows Recall feature preview following concerns raised by security and privacy experts over the AI technology. Recall enables Windows users to easily find something they know they have seen before on their PC by taking screenshots at regular intervals to capture the user’s activities.
New York Times says data breach affected freelance visual contributors – The New York Times sent out breach notification letters this week to several freelancers that had information involved in an incident uncovered last week.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
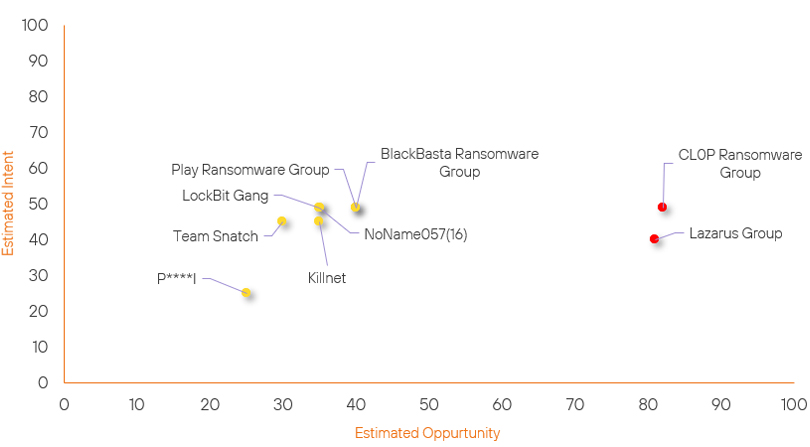
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| P****I | New | → | Basic | ↑ 25 | (25) | ↑ 25 | (25) |
| BlackBasta Ransomware | Basic | → | Basic | ↑ 5 |
(40) | → 0 | (49) |
| CL0P Ransomware Group | High | → | High | ↓ 1 | (82) | → 0 | (49) |
| Killnet | Basic | → | Basic | → 0 | (35) | ↓ 4 | (45) |
| Team Snatch | Basic | → | Basic | → 0 | (30) | ↓ 4 | (45) |
| Play Ransomware Group | Basic | → | Basic | ↓ 5 | (40) | → 0 | (49) |
| Lazarus Group | High | → | High | → 0 | (81) | ↓ 5 | (40) |
| NoName057(16) | Basic | → | Basic | ↓ 10 | (35) | → 0 | (49) |
| LockBit Gang | Moderate | → | Basic | ↓ 18 | (35) | → 0 | (49) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Scattered Spider | ▲ | Spear Phishing | ▲ | CVE-2024-3080 | ▲ | Google Chrome | ▲ |
| ShinyHunters | ▲ | DISGOMOJI Malware | ▲ | CVE-2024-4577 | ▲ | Broadcom | ▲ |
| DarkVault Ransomware Group | ▲ | 2FA Bypass | ▲ | CVE-2024-24919 | ▲ | Linux | ▲ |
| Desert Falcons | ▲ | Disinformation | ▲ | CVE-2024-6045 | ▲ | Key Tronic Corporation | ▲ |
| HUNT3R | ▲ | BianLian | ▲ | CVE-2022-0847 | ▲ | LVMH Moët Hennessy Louis Vuitton S.E. | ▲ |
Prominent Information Security Events
JetBrains Patches CVE-2024-37051, Affecting all IntelliJ-Based IDEs.
Source: JetBrains, Insikt Group | Vulnerability Intelligence from Insikt Group
Intelligence Cards: Intelligence & Reports
CVE-2024-37051 | CVVS Score: 7.5 | Recorded Future Risk Score: Medium – 56
On June 11, 2024, JetBrains patched a critical severity vulnerability, tracked as CVE-2024-37051, affecting its IntelliJ-based integrated development environments (IDEs) versions 2023.1 and later. At the time of writing, there have been no reports of this vulnerability being exploited in the wild. CVE-2024-37051 is an information disclosure flaw arising from the improper handling of access tokens to third-party sites.
Exploiting this vulnerability requires the JetBrains GitHub plugin to be enabled within IntelliJ-based IDEs, allowing threat actors to gain unauthorised access to GitHub repositories linked with affected IDEs. This could potentially lead to unauthorised code modifications and data exfiltration.
The patched versions for IntelliJ-based IDEs include:
- Aqua: 2024.1.2
- CLion: 2023.1.7, 2023.2.4, 2023.3.5, 2024.1.3, 2024.2 EAP2
- DataGrip: 2024.1.4
- DataSpell: 2023.1.6, 2023.2.7, 2023.3.6, 2024.1.2
- GoLand: 2023.1.6, 2023.2.7, 2023.3.7, 2024.1.3, 2024.2 EAP3
- IntelliJ IDEA: 2023.1.7, 2023.2.7, 2023.3.7, 2024.1.3, 2024.2 EAP3
- MPS: 2023.2.1, 2023.3.1, 2024.1 EAP2
- PhpStorm: 2023.1.6, 2023.2.6, 2023.3.7, 2024.1.3, 2024.2 EAP3
- PyCharm: 2023.1.6, 2023.2.7, 2023.3.6, 2024.1.3, 2024.2 EAP2
- Rider: 2023.1.7, 2023.2.5, 2023.3.6, 2024.1.3
- RubyMine: 2023.1.7, 2023.2.7, 2023.3.7, 2024.1.3, 2024.2 EAP4
- RustRover: 2024.1.1
- WebStorm: 2023.1.6, 2023.2.7, 2023.3.7, 2024.1.4
JetBrains also recommends the following action in response to this vulnerability:
- JetBrains strongly recommend updating to the latest version available for your IDE.
- If you have actively used GitHub pull request functionality in the IDE, we strongly advise that you revoke any GitHub tokens being used by the plugin. Given that the plugin can use OAuth integration or Personal Access Token (PAT), please check both and revoke as necessary.
Critical Vulnerability in Veeam Recovery Orchestrator.
Source: Insikt Group, Summoning Team | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
CVE-2024-29855| CVVS Score: 9.0 | Recorded Future Risk Score: High – 79
On June 13, 2024, security researcher Sina Kheirkhah (sinsinology on GitHub and @SinSinology on X, formerly known as Twitter) published a write-up and proof-of-concept (PoC) tool for CVE-2024-29855.
CVE-2024-29855 is a critical vulnerability in Veeam Recovery Orchestrator (VRO) and is an authentication bypass vulnerability caused by a hard-coded JWT secret. The vulnerability allows unauthenticated users to access the Veeam Recovery Orchestrator web interface as any user, including administrators. This vulnerability affects VRO versions 7.0.0.337 and 7.1.0.205 and older. On June 10, 2024, Veeam released VRO version 7.1.0.230 to fix CVE-2024-29855.
Veeam also provided a patch that updates the existing vulnerable VRO versions for those who cannot upgrade immediately.
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular, we would like to highlight and recommend applying the following patches should they apply:
- JetBrains - Update the latest patch versions for the impacted IDEs, evaluate GitHub tokens, and revoke them where necessary.
- Veeam - Ensure that Veeam Recovery Orchestrator deployments are updated to one of the versions above or have had the latest patch applied.
- Outlook - Ensure that impacted products mentioned above are fully updated and patched according to their latest update.
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing these searching and hunting activities within your environment.
