Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Vulnerability in Phoenix SecureCore UEFI Firmware Impacts Multiple Intel Processor Families – Eclypsium Automata discovered and reported on June 20, 2024, about a critical vulnerability in Phoenix SecureCore Unified Extensible Firmware Interface (UEFI) firmware, tracked as CVE-2024-0762, that resides in Intel Core desktop and mobile processors.
PoC and Temporary Fix for Critical JavaScript Sandbox Escape – On June 19, 2024, GitHub user Marven11 published a proof-of-concept (PoC) and fix for CVE-2024-28397. CVE-2024-28397 is a critical JavaScript sandbox escape vulnerability affecting the js2py Python package versions up to 0.74 running under Python 3.
SolarWinds Serv-U Vulnerability Exploited in the Wild – The exploited flaw, tracked as CVE-2024-28995, is a high-severity directory transversal vulnerability that allows attackers to read sensitive files on the host machine. SolarWinds disclosed the bug on June 6, when it announced that Serv-U 15.4.2 hotfix 1 and previous versions, including Serv-U FTP Server, Serv-U Gateway, and Serv-U MFT Server, are affected. The flaw was addressed in Serv-U 15.4.2 hotfix 2.
Potential Threats
Exploit Kit for Windows CVE-2024-30078 for sale and PoC available - CVE-2024-30078 is a critical vulnerability in Windows Wi-Fi Driver that allows a remote, unauthenticated threat actor to execute malicious code with SYSTEM privilege on a target system. According to Microsoft, threat actors can set up a malicious Wi-Fi network and trick victims within radio range into connecting to it.
Threat Actors Use Rafel RAT to Target Android Devices For Espionage and Ransomware – Several threat actors have been distributing Rafel RAT, an open-source remote administration tool, for espionage and ransomware operations targeting Android devices. Checkpoint reported about these activities on June 20, 2024, and noted the advanced persistent threat (APT) group APT-C-35 previously distributed the malware throughout April and May 2024.
New OPIX Ransomware Reported by Broadcom - A new ransomware variant called OPIX encrypts user files using a random character string and adds the ". OPIX" extension to them. According to a June 13, 2024, Broadcom report, OPIX is commonly spread through social engineering tactics like phishing emails and drive-by downloads.
General News
US Bans Kaspersky Antivirus Software - On June 20, 2024, the U.S. Department of Commerce's Bureau of Industry and Security (BIS) announced a ban on Kaspersky Lab's U.S. subsidiary from offering its security software in the country due to national security concerns.
More than 12,000 Santander employees in US affected by Snowflake breach - More than 12,000 U.S.-based employees of banking giant Santander had information leaked in a breach in May connected to the cloud storage provider Snowflake. Santander informed regulators of the breach on Wednesday, warning that the information of 12,786 employees was accessed during an incident the company believes began on April 17.
"Researchers" exploit Kraken exchange bug, steal $3 million in crypto – The Kraken crypto exchange disclosed today that alleged security researchers exploited a zero-day website bug to steal $3 million in cryptocurrency and then refused to return the funds.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
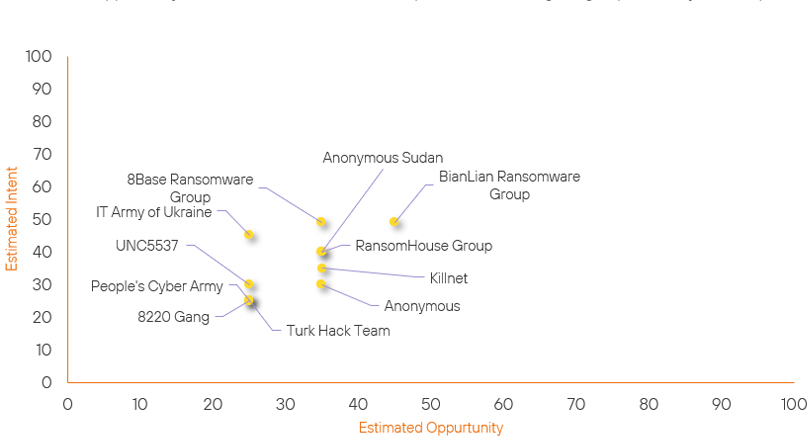
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| UNC5537 | New | → | Basic | ↑ 25 | (25) | ↑ 30 | (30) |
| People's Cyber Army | New | → | Basic | ↑ 25 |
(25) | ↑ 25 | (25) |
| 8220 Gang | New | → | Basic | ↑ 25 | (25) | ↑ 25 | (25) |
| IT Army of Ukraine | Basic | → | Basic | → 0 | (25) | ↑ 20 | (45) |
| Anonymous | Basic | → | Basic | → 0 | (35) | ↑ 5 | (30) |
| BianLian Ransomware Group | Basic | → | Basic | ↑ 5 | (45) | → 0 | (49) |
| RansomHouse Group | Basic | → | Basic | → 0 | (35) | ↓ 5 | (40) |
| 8Base Ransomware Group | Basic | → | Basic | ↓ 5 | (35) | → 0 | (49) |
| Anonymous Sudan | Basic | → | Basic | → 0 | (35) | ↓ 9 | (40) |
| Killnet | Basic | → | Basic | → 0 | (35) | ↓ 10 | (35) |
| Turk Hack Team | Basic | → | Basic | → 0 | (25) | ↓ 20 | (25) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| LockBit Gang | ▲ | Lockbit 3.0 | ▲ | CVE-2024-32896 | ▲ | U.S. Government | ▲ |
| BlackSuit Ransomware | ▲ | Adware | ▲ | CVE-2024-0762 | ▲ | Jollibee | ▲ |
| StarsX Team | ▲ | BlackSuit Ransomware | ▲ | CVE-2024-28995 | ▲ | BTCTurk | ▲ |
| RedJuliett | ▲ | Backdoor | ▲ | CVE-2024-27812 | ▲ | Google Mail | ▲ |
| HUNT3R | ▲ | Gh0st RAT | ▲ | CVE-2024-27815 | ▲ | Android | ▲ |
Prominent Information Security Events
Vulnerability in Phoenix SecureCore UEFI Firmware (CVE-2024-0762).
Source: Phoenix, Insikt Group, Eclypsium | Vulnerability Intelligence from Insikt Group
Intelligence Cards: Intelligence & Reports
CVE-2024-0762 | CVVS Score: 7.5 | Recorded Future Risk Score: Medium – 64
Eclypsium Automata discovered and reported on June 20, 2024, about a critical vulnerability in Phoenix SecureCore Unified Extensible Firmware Interface (UEFI) firmware, tracked as CVE-2024-0762, that resides in Intel Core desktop and mobile processors.
The issue stems from mishandling Trusted Platform Module (TPM) configurations in UEFI, potentially allowing buffer overflow and malicious code execution. Threat actors can exploit CVE-2024-0762 to gain elevated privileges and execute code within UEFI, similar to tactics seen in firmware backdoors such as BlackLotus, evading security measures.
This vulnerability affects various Phoenix Technologies' SecureCore firmware versions across Intel processor families including the ones listed below:
- Securecore For Intel Alder Lake
- Securecore For Intel Coffee Lake
- Securecore For Intel Comet Lake
- Securecore For Intel Ice Lake
- Securecore For Intel Jasper Lake
- Securecore For Intel Kaby Lake
- Securecore For Intel Meteor Lake
- Securecore For Intel Raptor Lake
- Securecore For Intel Tiger Lake
This CVE can also affect Lenovo ThinkPad models, among others.
Phoenix Technologies released fixes for CVE-2024-0762 on May 14, 2024, while Lenovo have released updated firmware. Both of these fixes should be applied as soon as possible to mitigate the vulnerability.
Windows Wi-Fi Driver Vulnerability (CVE-2024-30078) Exploit for Sale and PoC available.
Source: Insikt Group, Microsoft MSRC | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
CVE-2024-30078| CVVS Score: 8.8 | Recorded Future Risk Score: High – 79
On June 14, 2024, “Sentinel”, a member of the underground forum XSS, advertised an exploit kit for CVE-2024-30078. CVE-2024-30078 is a critical vulnerability in Windows Wi-Fi Driver that allows a remote, unauthenticated threat actor to execute malicious code with SYSTEM privilege on a target system.
Based on the underground forum advertisement, the CVE-2024-30078 exploit kit can infect a victim’s device through two methods: a compromised access point (router) and a Wi-Fi network saved on a target’s device. The second method requires the threat actor to be within the target victim's radio range.
In the same underground forum advertisement, on June 17, 2024, XSS forum member “vei” shared an open-source proof-of-concept (PoC) script for CVE-2024-30078. The PoC, developed by security researcher Alperen Ugurlu, detects CVE-2024-30078 in web servers and executes a specified command on vulnerable servers. Currently, the PoC, which was initially found on GitHub, has been removed. The PoC used Nessus to scan for specific endpoints and provide the actual command to execute on vulnerable targets.
According to Microsoft, threat actors can set up a malicious Wi-Fi network and trick victims within radio range into connecting to it. Once a victim’s device connects to the network, the threat actors can send specially crafted packets to their device to exploit CVE-2024-30078 and achieve remote code execution (RCE).
CVE-2024-30078 affects all versions of Windows, including Windows Server. On June 11, 2024, Microsoft released a patch to fix CVE-2024-30078.
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular, we would like to highlight and recommend applying the following patches should they apply:
- SecureCore - Update to the latest firmware for impacted machines running SecureCore UEFI.
- Windows WIFI Driver - Ensure that the associated patch is applied, especially on machines that are accessible through public locations.
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
