Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
VMware patches 3 zero days – On May 14, 2024, VMware patched four vulnerabilities, three of which were zero-day vulnerabilities, tracked as CVE-2024-22267, CVE-2024-22269, CVE-2024-22270, and CVE-2024-22268, affecting its Workstation and Fusion products.
Apple Patches Safari Web Browser Vulnerability CVE-2024-27834 – On May 13, 2024, Apple patched a zero-day vulnerability, tracked as CVE-2024-27834, affecting its Safari web browser on macOS Monterey and macOS Ventura systems.
Adobe Patches 12 Critical Vulnerabilities In Acrobat and Reader – Adobe issued a security update on May 14, 2024, for its Acrobat and Reader software on both Windows and macOS platforms addressing 12 critical vulnerabilities that could potentially allow arbitrary code execution and memory leaks if they are exploited.
Potential Threats
Threat Actors Use Dropbox in Two-Stage Spearphishing Campaign - On May 17, 2024, Kaspersky reported on a phishing scheme that uses two separate phishing accounting-related emails to lure victims into entering their login credentials.
New Android Banking Trojan Masquerades as Google Play Update App – The Antidot Android Banking Trojan masqueraded as a legitimate Google Play update application in a new campaign, Cyble reported on May 16, 2024. Infections started when users downloaded what appeared to be a Google Play update.
FIN7 Uses Malicious Google Ads to Aid Deployment - On May 8, 2024, eSentire reported that, in April 2024, it observed the cybercriminal group FIN7 abusing trusted brand names and sponsored Google Ads to distribute malicious MSIX payloads and infect victims with NetSupportRAT and DiceLoader.
General News
New UK system will see ISPs benefit from same protections as government networks - Launched at the CyberUK conference in Birmingham, the Share and Defend system will provide a list of malicious domains to a range of communications providers so the domains can be added to blocklists.
New backdoors on a European government's network appear to be Russian - Two previously unknown backdoors likely deployed by a Russian state hacking group have been discovered compromising the foreign affairs ministry of a European country.
New 'Siren' mailing list aims to share threat intelligence for open source projects - The Open Source Security Foundation (OpenSSF) announced a new email mailing list named Siren that aims to spread threat intelligence related to open source projects.
Since the discovery of the Log4j issue, the security of open-source projects has become a critical national security concern. The recent situations around XZUtils and OpenJS have reignited concerns about how the open-source community is handling cybersecurity.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
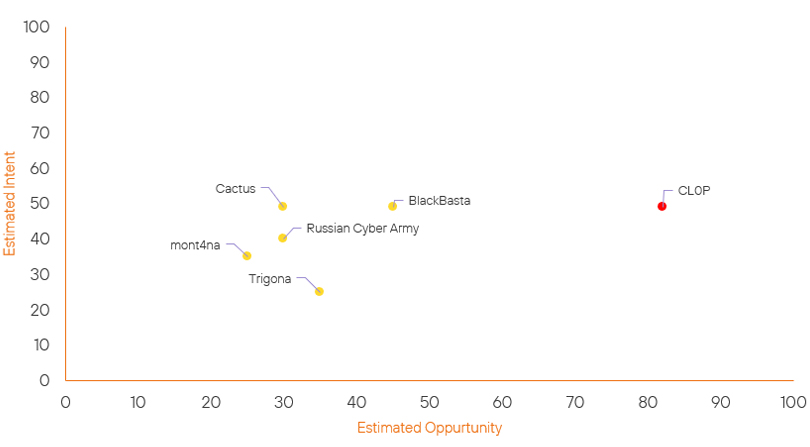
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Киберармия России (Russian Cyber Army) | Basic | → | Basic | → 0 | (30) | ↑ 5 | (40) |
| mont4na | Basic | → | Basic | → 0 | (25) | ↑ 5 | (35) |
| Cactus Ransomware Group | Basic | → | Basic | → 0 | (30) | ↑ 4 | (49) |
| CL0P Ransomware Group | High | → | High | ↓ 1 | (82) | → 0 | (49) |
| BlackBasta Ransomware Group | Basic | → | Basic | ↓ 1 | (45) | → 0 | (49) |
| Trigona Ransomware Group | Basic | → | Basic | → 0 | (35) | ↓ 5 | (25) |
Prominent Information Security Events
VMware Zero-Day Patches.
Source: VMware, Insikt Group | Vulnerability Intelligence from Insikt Group
Intelligence Cards: Intelligence & Reports
CVE-2024-22267 | CVVS Score: 9.3 | Recorded Future Risk Score: High – 76
CVE-2024-22268 | CVVS Score: 7.1 | Recorded Future Risk Score: Medium - 43
CVE-2024-22269 | CVVS Score: 7.1 | Recorded Future Risk Score: Medium – 45
CVE-2024-22270 | CVVS Score: 7.1 | Recorded Future Risk Score: Medium – 50
On May 14, 2024, VMware patched four vulnerabilities, three of which were zero-day vulnerabilities affecting its Workstation and Fusion products. These vulnerabilities reside in VMware Workstation versions 17.x and VMware Fusion versions 13.x. At the time of writing, there have been no reports of these vulnerabilities being exploited in the wild.
Details surrounding the four vulnerabilities are as follows:
- CVE-2024-22267 is a use-after-free flaw in the Bluetooth device within >VMware Workstation and Fusion products, rated with a severity score of 9.3 (critical). Exploiting this vulnerability requires threat actors to have local administrative privileges on a virtual machine.
- CVE-2024-22269 is an information disclosure flaw in the Bluetooth device within VMware Workstation and Fusion products, rated with a severity score of 7.1 (high). Exploiting this vulnerability requires threat actors to have local administrative privileges on a virtual machine, enabling them to access sensitive data in hypervisor memory within the virtual machine's environment.
- CVE-2024-22270 is an information disclosure flaw in the Host Guest File Sharing (HGFS) functionality within VMware Workstation and Fusion products, rated with a severity score of 7.1 (high). Exploiting this vulnerability requires threat actors to have local administrative privileges on a virtual machine, enabling them to access sensitive data in hypervisor memory within the virtual machine's environment.
- CVE-2024-22268 is a heap buffer-overflow flaw in the Shader functionality within VMware Workstation and Fusion products, rated with a severity score of 7.1 (high). Exploiting this vulnerability requires the activation of the virtual machine's 3D graphics feature. This activation could enable threat actors with non-administrative access to send specially crafted graphics commands to the 3D graphics processing unit (GPU), potentially leading to system instability and a denial-of-service (DoS) condition.
VMware urges administrators to update the affected products to the latest versions, version 17.5.2 for VMware Workstation, and version 13.5.2 for VMware Fusion. A temporary solution for those unable to install updates immediately involves disabling Bluetooth support for virtual machines until updates can be applied.
Adobe Critical Vulnerabilities In Acrobat and Reader.
Source: Adobe | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
Adobe issued a security update on May 14, 2024, for its Acrobat and Reader software on both Windows and macOS platforms addressing 12 critical vulnerabilities that could potentially allow arbitrary code execution and memory leaks if they are exploited.
The vulnerabilities affected versions before 24.002.20759 and 20.005.30635/30636 in Acrobat DC, Acrobat Reader DC, Acrobat 2020, and Acrobat Reader 2020. The CVEs patched have been listed below, along with their vulnerability type:
- CVE-2024-30284 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-30310 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34094 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34095 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34096 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34097 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34098 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34099 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-34100 - Arbitrary code execution (CVSS: 7.8)
- CVE-2024-30311 - Memory leak (CVSS: 5.5)
- CVE-2024-30312 - Memory leak (CVSS: 5.5)
- CVE-2024-34101 - Memory leak (CVSS: 3.5)
Adobe advises users to update their software installations to the latest versions to mitigate these risks.
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular, we would like to highlight and recommend applying the following patches should they apply:
- VMware – Update to version 17.5.2 for VMware Workstation, and version 13.5.2 for VMware Fusion.
- Adobe – Update the latest version of Acrobat and Reader on all platforms
- Safari – Update Safari to the latest version provided by Apple.
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing these searching and hunting activities within your environment.
