Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Veeam Discloses Four Vulnerabilities in Backup Enterprise Manager - Veeam issued patches for several critical vulnerabilities in its Backup Enterprise Manager on May 21, 2024. All these vulnerabilities have been fixed in version 12.1.2.172.
Cisco Updates Patch for CVE-2022-20760 Affecting ASA and FTD Software – Cisco issued a final update to an advisory initially published on April 27, 2022; this concerns a high-severity vulnerability, tracked as CVE-2022-20760. Cisco has released updates that address the vulnerability and updates should be applied.
GitLab Patches High-Severity Vulnerability in Web IDE - On May 22, 2024, GitLab patched several vulnerabilities affecting GitLab Community Edition (CE) and Enterprise Edition (EE). GitLab recommends users of both Community and Enterprise Editions update their systems to versions 17.0.1, 16.11.3, and 16.10.6 to mitigate potential exploitation.
Potential Threats
CISA Warns of Actively Exploited Apache Flink Vulnerability, CVE-2020-17519 - On May 23, 2024, the US Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2020-17519, a critical vulnerability affecting versions 1.11.0, 1.11.1, and 1.11.2 of Apache Flink, to its Known Exploited Vulnerabilities (KEV) catalogue.
New ShrinkLocker Ransomware Adopts BitLocker to Target Entities in the Government, Healthcare, and Manufacturing Sectors – A new ransomware variant dubbed ShrinkLocker has adopted BitLocker, Microsoft’s legitimate encryption technology, to target corporate systems.
Researchers Discover DNSBomb DDoS Attacks that Manipulate DNS Traffic - SOCRadar reported a new Distributed Denial of Service (DDoS) attack vector dubbed DNSBomb that targets critical internet infrastructure. Researchers from Tsinghua University found that DNSBomb uses the recursive function of DNS resolvers to amplify traffic, which can reach up to 8.7 Gbps. The analysis showed that DNSBomb could achieve a bandwidth amplification factor of over 20,000 times the original traffic.
General News
Amid funding cuts, backlog of unanalysed vulnerabilities in gov't database is growing - The National Vulnerability Database has been forced to limit its operations due to funding shortages and an influx of vulnerabilities.
Alarm over Russian-directed sabotage operations growing across Europe - Security agencies and governments across Europe are increasingly warning about the threat posed by Russia-directed saboteurs operating on their territories.
UK to propose mandatory reporting for ransomware attacks and licensing regime for all payments - Officials in Britain are set to propose a major overhaul of how the country responds to ransomware attacks by requiring all victims to report incidents to the government, and then obliging those victims to seek a license before making any extortion payments.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
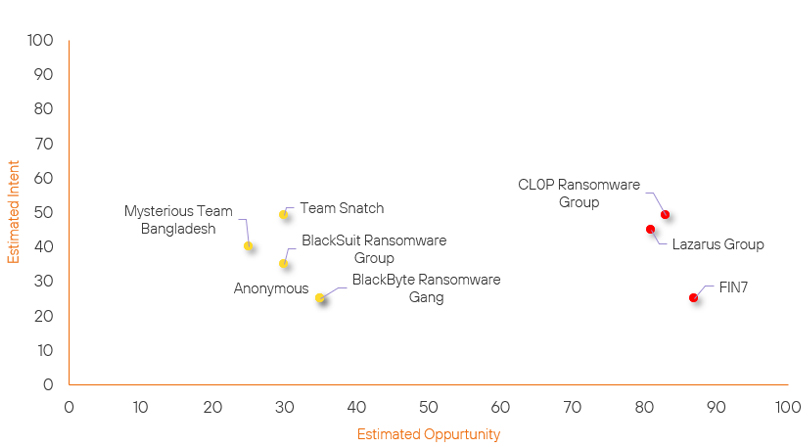
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| BlackSuit Ransomware Group | Basic | → | Basic | → 0 | (30) | ↑ 5 | (35) |
| CL0P Ransomware Group | High | → | High | ↑ 1 | (83) | → 0 | (49) |
| FIN7 | High | → | High | ↓ 2 | (87) | → 0 | (25) |
| Lazarus Group | High | → | High | → 0 | (81) | ↓ 4 | (45) |
| BlackByte Ransomware Gang | Basic | → | Basic | ↓ 5 | (35) | → 0 | (25) |
| Team Snatch | Basic | → | Basic | ↓ 5 | (30) | → 0 | (49) |
| Mysterious Team Bangladesh | Basic | → | Basic | → 0 | (25) | ↓ 5 | (40) |
| Anonymous | Basic | → | Basic | → 0 | (35) | ↓ 10 | (25) |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| RansomHub Ransomware Group | ▲ | DDoS | ▲ | CVE-2024-2961 | ▲ | Services | ▲ |
| Islamic Cyber Team | ▲ | ShrinkLocker | ▲ | CVE-2024-27842 | ▲ | Software and IT services | ▲ |
| APT36 | ▲ | Cyber Espionage | ▲ | CVE-2018-5274 | ▲ | Internet Archive | ▲ |
| LockBit Gang | ▲ | Deed RAT | ▲ | CVE-2023-5035 | ▲ | Real Estate | ▲ |
| 8Base Ransomware Group | ▲ | Improper Access Control | ▲ | CVE-2024-14144 | ▲ | Government of India | ▲ |
Prominent Information Security Events
Veeam Backup Enterprise Manager Vulnerabilities.
Source: Veeam, Insikt Group | Vulnerability Intelligence from Insikt Group
Intelligence Cards: Intelligence & Reports
CVE-2024-29849 | CVVS Score: 9.8 | Recorded Future Risk Score: High – 79
CVE-2024-29850 | CVVS Score: 8.8 | Recorded Future Risk Score: High - 67
CVE-2024-29851 | CVVS Score: 7.2 | Recorded Future Risk Score: Medium – 31
CVE-2024-29852 | CVVS Score: 2.7 | Recorded Future Risk Score: Medium – 32
Veeam issued patches for several critical vulnerabilities in its Backup Enterprise Manager on May 21, 2024. All these vulnerabilities have been fixed in version 12.1.2.172. According to Veeam, deploying Veeam Backup Enterprise Manager is optional, and environments without it installed are not affected by these flaws.
Details surrounding the four vulnerabilities are as follows:
- CVE-2024-29849 allows unauthenticated threat actors to log in to the web interface as any user and has a CVSS score of 9.8.
- CVE-2024-29850 allows account takeover via NTLM relay.
- CVE-2024-29851 allows a high-privileged user to steal the NTLM hash of the Veeam Backup Enterprise Manager service account if that service account is anything other than the default Local System account.
- CVE-2024-29852 allows high-privileged users to read backup session logs.
Backup Enterprise Manager instances installed on dedicated servers can be updated to version 12.1.2.172 without having to upgrade Veeam Backup & Replication immediately.
If upgrading is not possible, Veeam recommends halting the Backup Enterprise Manager. The software can be installed if not in use.
Trojanised Minesweeper clone.
Source: Insikt Group, CERT-UA | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
CERT-UA reported that the threat actor “UAC-0188” targeted multiple financial and insurance entities across Europe and the United States between February and March 2024. UAC-0188 used trojanised Minesweeper code, concealing malicious Python scripts and facilitating the unauthorised installation of the SuperOps Remote Monitoring and Management (RMM) software.
SuperOps RMM, a legitimate tool used by IT service providers, was exploited to gain unauthorised remote access and control over compromised systems.
The victim is sent an email with a link to Dropbox from which an executable (.SCR) file of around 33MB will be downloaded. The said file was created using PyInstaller and contains, among other things, the legitimate Python code of the game "Minesweeper" as well as a 28MB base64-encoded string.
Further, as a result of string concatenation and decoding, a ZIP archive will be obtained, from which, using a statically set password, an MSI file representing a legitimate SuperOps RMM program will be extracted and executed. Running this program on a PC will give third parties unauthorised remote access to the computer.
We have provided a list of. Known IOC’s for this potential attack vector below:
| a46317e7c238be03b317840d7c0e3636 | 10a6c318be4f1a2f56eedd855e7e5fd4a883a17022b933cd58fa73c184363019 | Medical_Analyses_from_20.05.2024.scr |
| c2784067546e9a9865397bfd868cf71d | 4a3192769a62c5491838720bf66ea445a5d21668e5dc5a9943548d744ecc9113 | 4qrjbatw.py |
| 0d2968cf9bb938bad91d59bec617ef28 | 57162522bdf6cab0c596672a0e21ecdbdbf9c967b77848f9a25f3e5be3291be1 | image.jpg |
| a5c49a5691a0a30f76d2d140fdc377af | 30e5f5b2ec76b99e3ac5fbbb8e484047cefe7a04b39f8e31b60c6b1e86f349e4 | data.zip |
| d2caf4d50fdf083cda1a5f781e4f1bdf | dee0e820c2582badd477ccfbe197d6a5803b86b0c1b25503449d9691b6f6166a | 7A99IAJSMFI8_2KGVBADXSI68_windows_x64.msi |
| a027d7045c669e365d0ef01768223329 | 46337cb1cc51378858d5e47713b450c063f994c7909fcb010053a70cb9a592fe | info_statement_ID00000235135381.scr |
| 3c74cf1cc59462e98cfec647d42c5dca | 690ce2375759e1c31998011265d31c063615413495cf3596beffe3c11dbaaf06 | Document_ChaseStatement0003241353491(1).scr |
| 8eb0fdc88fb9820108636d21dbdc7b4d | 2ad14276e4678c1f9d63bcfaa0658228e95cc92e16c78f46fa8f767cb7d5ab3d | 2d94hf6q.py |
| 65f9c3b459cdd5db1a8cad007ca12155 | f91a54d4e13e94c0e1b74b1b074a222ce50e258fc63dbbb9f2e651c9485771be | img00.jpg |
| f6a1ed6f81498ee3bdb3842c3f93ddea | 987751d2052b4e04e619b431239f286a789a647c0b99cc702d402110bdcdf8a5 | data.zip |
| a6205a0cf9bec9aa4753939dbe41ec0b | 9ff032282abcc4f82dbb71052033f7a5bfbc334dad0e6ddb65fecb8de30a1865 | DGEY39OGHDS0_1XLVGTIHXL1J4_windows_x64.msi |
| 1c5d4add00c4170283d4d4f338ac8871 | 5a223bf043e552e85f8fe91693221c34aafdfd2b3867e733f756f288a38410a1 | CCleaner1.zip |
| 70d376d638868eefb81ffdc480744bf1 | 1cb846e9cf851247ea3955f7c3a310bd87209eff37a031c0c072f1f05bd5c38b | 1SIQ42DK7TWCG_1IXOK8MU075KW_windows_x64.msi |
| 7c18d18c4f933e4aa056e86e900adf5e | dfcd0510f07ca6c2979c4953f6e88447fda360b6a4ff995fd1bb3dc9e0aa9edb | ImportantSecurityUpdate.vbs |
| 8181331b4ae052d895aa91e06b938dc3 | 8519569df6b704ff4c1070929395b40933dee93604d087072edbaa3a107491d5 | 8181331b4ae052d895aa91e06b938dc3 |
| a3a28d0e8b567a2f485d7e3dce2e8fd4 | d60bc54742e1e4f49b2ae74080ef293150f38d7e6e624008ef53a7a8dc30d42a | BankOfAmerica_Statement_0543922.scr |
| 8cb4012458d390b9a2866278473c696b | 08d39909da1a5b36350493982cf05771445b7f63f11007642fd450cee07b7cde | ChaseOnline_Statement_ID034241356941.txt |
| a46317e7c238be03b317840d7c0e3636 | 10a6c318be4f1a2f56eedd855e7e5fd4a883a17022b933cd58fa73c184363019 | Medical_Analyses_from_20.05.2024.scr |
| c2784067546e9a9865397bfd868cf71d | 4a3192769a62c5491838720bf66ea445a5d21668e5dc5a9943548d744ecc9113 | 4qrjbatw.py |
| 0d2968cf9bb938bad91d59bec617ef28 | 57162522bdf6cab0c596672a0e21ecdbdbf9c967b77848f9a25f3e5be3291be1 | image.jpg |
| a5c49a5691a0a30f76d2d140fdc377af | 30e5f5b2ec76b99e3ac5fbbb8e484047cefe7a04b39f8e31b60c6b1e86f349e4 | data.zip |
| d2caf4d50fdf083cda1a5f781e4f1bdf | dee0e820c2582badd477ccfbe197d6a5803b86b0c1b25503449d9691b6f6166a | 7A99IAJSMFI8_2KGVBADXSI68_windows_x64.msi |
| a027d7045c669e365d0ef01768223329 | 46337cb1cc51378858d5e47713b450c063f994c7909fcb010053a70cb9a592fe | info_statement_ID00000235135381.scr |
| 3c74cf1cc59462e98cfec647d42c5dca | 690ce2375759e1c31998011265d31c063615413495cf3596beffe3c11dbaaf06 | Document_ChaseStatement0003241353491(1).scr |
Network:
patient-docs-mail[.]com
support2@patient-docs-mail[.]com
acmaiiykmm@protonmail[.]com
hxxps://anotepad[.]com/notes/2d94hf6q
hxxps://anotepad[.]com/notes/2st44b98
hxxps://anotepad[.]com/notes/4qrjbatw
hxxps://anotepad[.]com/notes/cwknw3qs
hxxps://anotepad[.]com/notes/k55a4dq3
hxxps://anotepad[.]com/notes/txb53br5
hxxps://www[.]dropbox[.]com/scl/fi/s6il9o10zmecnrurvw3m8/document_chasestatement0003241353491[.]scr?rlkey=i3gjtul68q9zeeuyw0esi1vm0&dl=1
hxxps://www[.]dropbox[.]com/scl/fi/w864v8x6a53zuaphg01t3/chaseonlinestatement032445381[.]scr?rlkey=ez6lq3jwgu9trx1meprytyhac&dl=1
yemmyusa[.]com
Host:
C:\Program Files\superopsrmm\conf\assetinfo.conf
C:\Program Files\superopsrmm\conf\serverkey.txt
C:\Program Files\superopsrmm\logs\superops.log
Remediation Actions
Following the information provided above, we would recommend that the technologies mentioned above be fully patched and up to date. In particular, we would like to highlight and recommend applying the following patches should they apply:
- Veeam – Backup Enterprise Manager instances installed on dedicated servers should be updated to version 12.1.2.172
- Gitlab – Both Community and Enterprise Editions should be updated to versions 17.0.1, 16.11.3, and 16.10.6
We would also recommend proactively checking your environment for the software versions mentioned above and hunting for any known IOCs related to them.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing these searching and hunting activities within your environment.
