Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Microsoft SharePoint Vulnerability CVE-2024-38094 Exploited to Breach Corporate Network - Threat actors exploited the CVE-2024-38094 vulnerability in Microsoft SharePoint to gain unauthorised access to a company’s network. According to the report by Rapid7 on October 30, 2024, the compromise remained undetected for two weeks during which the attackers maintained control over a Microsoft Exchange service account with domain administrator privileges.
Veeam Backup & Replication Vulnerability, CVE-2024-40711, Exploited - Threat actors are exploiting CVE-2024-40711, a deserialisation of untrusted data vulnerability in Veeam Backup & Replication (VBR) servers, to deploy a new ransomware dubbed Frag. CVE-2024-40711 can allow threat actors to execute arbitrary code if exploited. A proof-of-concept (PoC) exploit code for CVE-2024-40711 is publicly available on GitHub.
Synology Discloses Zero-Click Vulnerability Tracked as CVE-2024-10443 - On November 5, 2024, Synology released patches for CVE-2024-10443, a zero-click vulnerability affecting DiskStation and BeeStation network-attached storage (NAS) devices. The vulnerability resides in the SynologyPhotos component, allowing attackers to achieve root-level remote code execution (RCE) without user interaction.
Potential Threats
Gootloader’s Delivery Method Shifts From SEO Poisoning to Fake PDF Converter Sites - On November 7, 2024, a security researcher who tracks Gootloader, published a write-up detailing a shift in its delivery method. Over time, the threat actors started using search engine optimisation (SEO) poisoning to attract specific targets and delivered other payloads through Gootloader, such as ransomware and remote access trojans (RATs). SEO poisoning is a method where threat actors manipulate search engine results to drive users to harmful websites, often leading to malware or phishing attacks.
CopyRh(ight)adamantys Phishing Campaign Deploys Rhadamanthys Stealer Globally - On November 6, 2024, Check Point Research reported an ongoing phishing campaign dubbed “CopyRh(ight)adamantys”, since July 2024, targeting organisations globally. This campaign impersonates well-known companies in phishing emails claiming copyright violations. Recipients are directed to download a password-protected file from a link which redirects to Dropbox or Discord to access another password-protected archive.
New Android Banking Trojan ToxicPanda Targets Over 16 Banks - A new banking trojan tracked as “ToxicPanda”, was used to target sixteen banking institutions across Europe and Latin America. ToxicPanda's main goal is to initiate money transfers from compromised Android devices.
General News
American CRM Providers Forth and Centrex Disclose Data Breach Affecting 1.5 Million Individuals - Set Forth, Inc. (Forth) and Centrex Software, Inc. (Centrex) notified approximately 1.5 million clients of a data breach that compromised their personally identifiable information (PII).
Cyberattack disables tracking systems and panic alarms on British prison vans - A cyberattack on a telematics company has left British prison vans without tracking systems or panic alarms, although there is no evidence criminals have attempted to exploit the situation. Microlise, the directly impacted company, informed the London Stock Exchange of the incident last week.
Texas-based oilfield supplier faces disruptions following ransomware attack - A key supplier for oilfields said a ransomware attack last week has caused disruptions and limited access to certain systems. In a regulatory filing on Thursday evening, Newpark Resources said it discovered the ransomware attack on October 29 that affected internal information systems.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
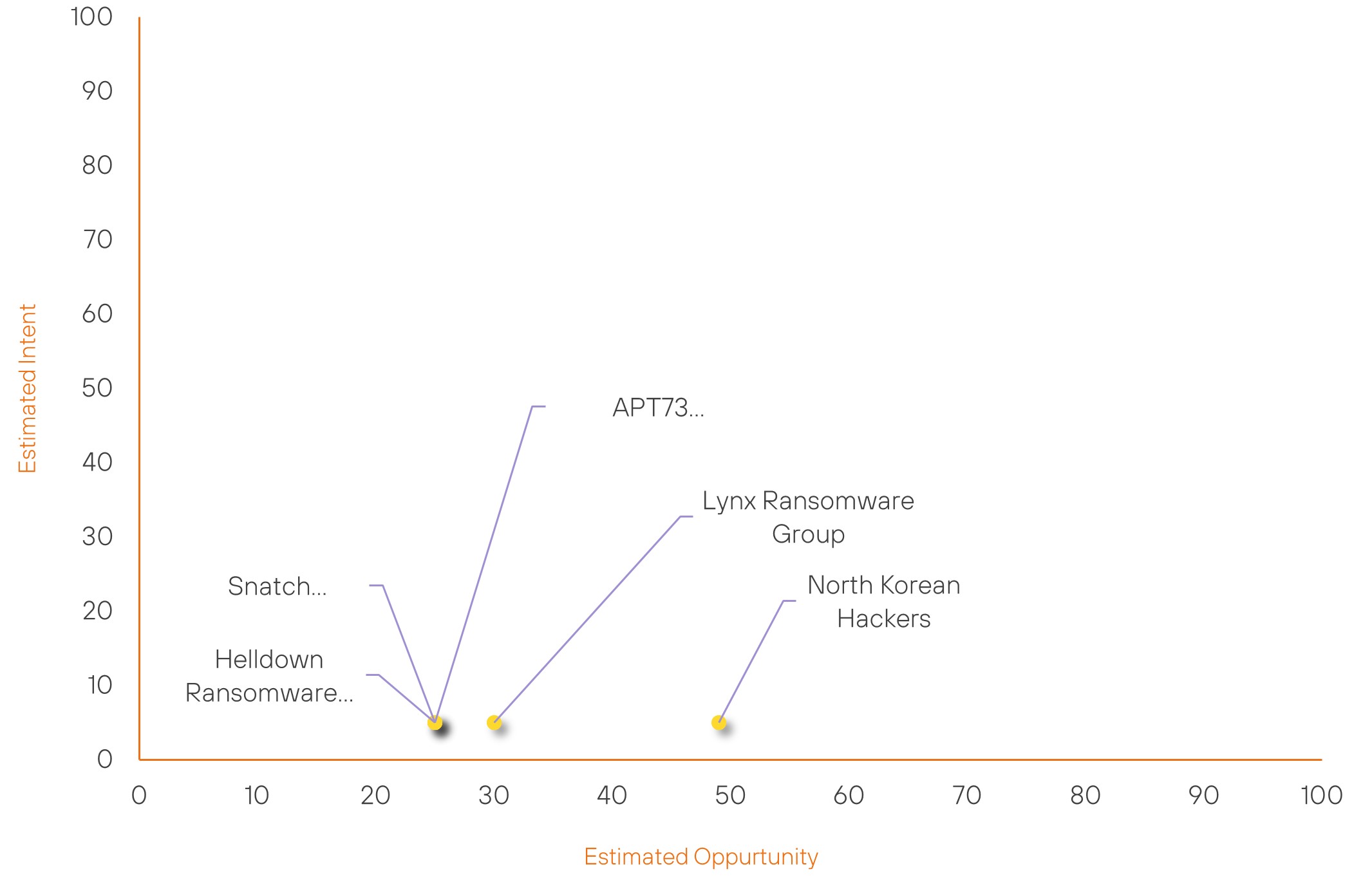
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| North Korean Hackers | New | → | Basic | (49) | ↑ 49 | (5) | ↑ 5 |
| Lynx Ransomware Group | New | → | Basic | (30) | ↑ 30 | (5) | ↑ 5 |
| Helldown Ransomware Group | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
| Snatch Ransomware Gang | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
| APT73 Ransomware Group | New | → | Basic | (25) | ↑ 25 | (5) | ↑ 5 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Iranian Hackers | ▲ | Phishing | ▲ | CVE-2024-40711 | ▲ | Retail | ▲ |
| Hanzala | ▲ | Brute Ratel C4 | ▲ | CVE-2017-0199 | ▲ | eCommerce | ▲ |
| Hellcat Ransomware Group | ▲ | REMCOS RAT | ▲ | CVE-2024-10914 | ▲ | Mortgage Companies | ▲ |
| LUNAR SPIDER | ▲ | Denial-of-Service | ▲ | CVE-2024-38094 | ▲ | HSBC | ▲ |
| Handala | ▲ | JS Loader | ▲ | CVE-2024-28888 | ▲ | HP | ▲ |
Prominent Information Security Events
Gootloader’s Delivery Method Shifts From SEO Poisoning to Fake PDF Converter Sites.
Source: Insikt Group, Gootloader | TTP Instance
Intelligence Cards: Intelligence & Reports
IOC: Domain: pdf-online-tools[.]com
IOC: Domain: berumenlaw[.]com
IOC: Domain: teamsapps[.]com
IOC: Domain: pdfdocx[.]com
IOC: Domain: unitepdf[.]com
IOC: Domain: erapdf[.]com
IOC: Domain: pdf[.]gdn
IOC: Domain: convertwordtopdf[.]io
IOC: Domain: berumenlaw[.]com
IOC: SHA256: 9c236eabb385b9402120bb087f0fbaa1b7ec11a897290ac6196d82197bd24ab0
IOC: SHA256: fbfb4a676c09566fa60e05cc51654d6de133aa8add30ae7dbfb1a20f95aeb16c
On November 7, 2024, a security researcher, who tracks Gootloader, published a write-up detailing a shift in its delivery method. Gootloader is a JavaScript-based loader that emerged in 2020, primarily known for delivering the Gootkit banking trojan. The threat actors use "drive-by download" attacks on compromised websites to deliver Gootloader. Over time, the threat actors started using search engine optimisation (SEO) poisoning to attract specific targets and delivered other payloads through Gootloader, such as ransomware and remote access trojans (RATs). SEO poisoning is a method where threat actors manipulate search engine results to drive users to harmful websites, often leading to malware or phishing attacks.
According to the security researcher, they observed threat actors using fake PDF-to-DOCX conversion sites to deliver Gootloader in early November 2024 instead of its previous method of SEO poisoning. The threat actors promoted PDF-to-DOCX conversion sites through Google ads by "ADWAVE LTD".
The Google ads direct victims to a WordPress site (pdfdocx[.]com) with a form where they can upload a PDF to convert to a DOCX file. The WordPress site checks whether the victim comes from an English-speaking country and has not accessed the site from the same network within the past 24 hours. If the victim meets these conditions, the site provides a download link (hxxps://pdfdocx.com/[guid]) for a ZIP archive, which contains a malicious JavaScript (. JS) file instead of the expected DOCX file. When the victim opens the JavaScript file, it triggers the installation of Gootloader on their system.
CopyRh(ight)adamantys Phishing Campaign Deploys Rhadamanthys Stealer Globally.
Source: Insikt Group, Checkpoint | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: IP: 15[.]235[.]176[.]166
IOC: IP: 198[.]135[.]48[.]191
IOC: IP: 95[.]169[.]204[.]214
IOC: IP: 139[.]99[.]17[.]158
IOC: IP: 103[.]68[.]109[.]208
IOC: IP: 15[.]235[.]138[.]155
On November 6, 2024, Check Point Research reported an ongoing phishing campaign dubbed “CopyRh(ight)adamantys”, since July 2024, targeting organisations globally. This campaign impersonates well-known companies in phishing emails claiming copyright violations. Recipients are directed to download a password-protected file from a link on appspot[.]com, which redirects to Dropbox or Discord to access another password-protected archive. This download initiates the malware installation through DLL side-loading, where a legitimate executable is used to load a malicious DLL containing the Rhadamanthys stealer.
The malware, identified as version 0.7 of Rhadamanthys, employs a multi-stage infection process, connecting to a C2 server and downloading additional modules, including data-theft tools embedded in WAV files.
According to Check Point, threat actors conduct the campaign for financial gain. They actively employ automated tools to create and manage phishing emails and sender accounts, targeting various organisations. This approach enables them to broaden the infection’s reach effectively.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-38094 – Apply the Security Update to SharePoint Server 2019, Enterprise 2016, SharePoint Server Subscription Edition.
- CVE-2024-40766 – Update to the latest version of Veeam Backup & Replication available.
- CVE-2024-10443 – Update to the latest version of BeePhotos for BeeStation and Synology Photos
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
