Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
Zoom Discloses Critical Vulnerabilities - Zoom has disclosed critical vulnerabilities, including a buffer overflow (CVE-2024-45421) that allows privilege escalation and an input validation flaw (CVE-2024-45419) leading to unauthorised access to sensitive data. Users should update to version 6.2.0 or later to mitigate these risks.
Apple Releases Urgent Patches for Exploited Zero-Day Vulnerabilities - Apple has released urgent patches for two zero-day vulnerabilities (CVE-2024-44308 and CVE-2024-44309) affecting Intel-based Macs and other devices. These flaws could allow remote code execution and cross-site scripting attacks. Users should install updates immediately to prevent exploitation.
Oracle Patches CVE-2024-21287 in Agile PLM - Oracle released a patch for CVE-2024-21287, a zero-day vulnerability in its Agile PLM software that was actively exploited. The flaw allows remote attackers to download files without requiring login credentials. Discovered by CrowdStrike, this vulnerability compromises the PLM application’s security permissions. Oracle advises all users to update to supported versions to mitigate risks.
Potential Threats
NodeStealer Malware Steals Credit Card Data from Facebook Ads - On November 19, 2024, The Hacker News reported that NodeStealer malware targets Facebook ad accounts by stealing user credentials through fraudulent tools and social media campaigns. Once infected, attackers can access sensitive business data, including financial and ad campaign details. The malware uses evasion techniques to avoid detection. Users are advised to implement strong authentication and monitor accounts for suspicious activity.
Mysterious Elephant APT Delivers Asyncshell Malware Using Hajj-Themed Phishing Campaign - APT-K-47, or Mysterious Elephant, is using Hajj-themed lures to deliver Asyncshell malware. The group uses phishing and a malicious CHM file to execute a decoy document while secretly running the malware. The updated Asyncshell allows remote control of systems and command execution, with enhanced encryption for command-and-control communications. Financial institutions are urged to strengthen security measures and monitor for suspicious activity.
Ghost Tap Attack Exploits NFC Payments to Steal Money - On November 21, 2024, Cybersecurity News reported on the 'Ghost Tap' attack, where cybercriminals exploit NFC technology in mobile payments like Google Pay and Apple Pay to steal credit card information. The malware relays NFC data to a 'mule' device for unauthorised transactions, bypassing traditional security. Experts urge financial institutions to enhance fraud detection and security measures to combat this growing threat.
General News
Cyberattacks Cost British Businesses $55 Billion in 5 Years - According to Reuters, cyberattacks have cost UK businesses £44 billion ($55.3 billion) over the past five years. Over half of businesses were affected, with data breaches being particularly costly, averaging £4.53 million ($5.7 million) per breach. These incidents highlight the significant financial impact of cybercrime and the need for stronger cybersecurity measures.
Hackers Breach US Firm via Russian Wi-Fi in 'Nearest Neighbor Attack - BleepingComputer reports that Russian hackers used a "nearest neighbour attack" to breach a U.S. firm. They accessed the company's network through a compromised nearby Wi-Fi, leveraging valid credentials to exfiltrate sensitive data.
Microsoft Launches Recall for Windows Insiders with Copilot+ PCs - On November 22, BleepingComputer reported that Microsoft began rolling out its "Recall" feature for Windows Insiders with Copilot+ PCs. The AI-powered tool captures screenshots of active windows, allowing users to search through them later. It is an opt-in feature with privacy controls, offering encryption and malware protection to ensure data security while enhancing productivity.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
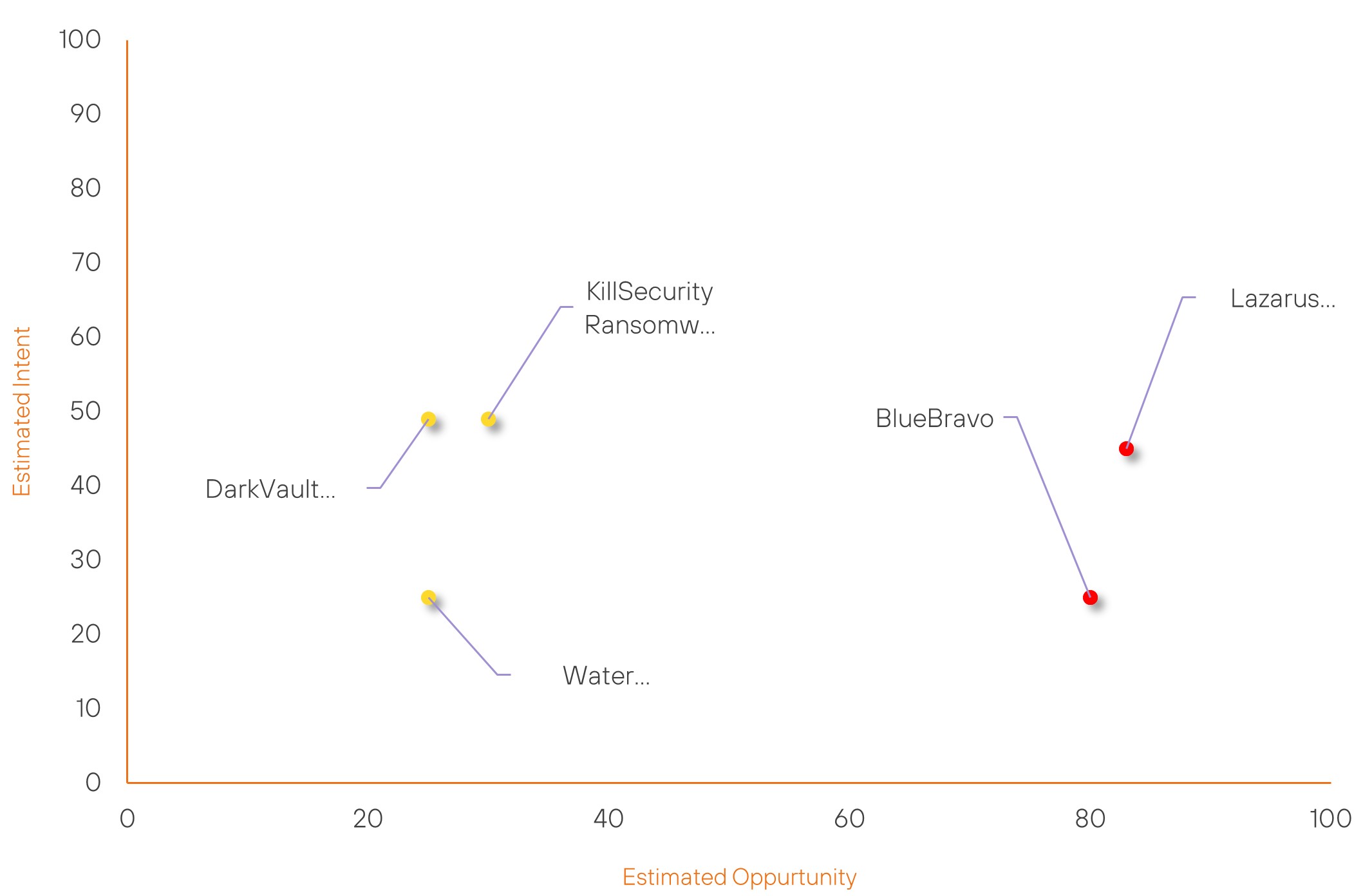
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Lazarus Group | High | → | High | (83) | → 0 | (45) | ↓ 4 |
| BlueBravo | High | → | High | (80) | ↑ 1 | (25) | → 0 |
| KillSecurity Ransomware Group | New | → | Basic | (30) | ↑ 30 | (49) | ↑ 49 |
| DarkVault Ransomware Group | New | → | Basic | (25) | ↑ 25 | (49) | ↑ 49 |
| Water Barghest | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Safepay Ransomware Group | ▲ | Adware | ▲ | CVE-2024-9474 | ▲ | Palo Alto Networks Firewall | ▲ |
| Hanzala | ▲ | Cobalt Strike | ▲ | CVE-2024-0012 | ▲ | Electric power | ▲ |
| Helldown Ransomware Group | ▲ | Insider Threat | ▲ | CVE-2024-42057 | ▲ | Telegram | ▲ |
| BlueDelta | ▲ | LockBit Ransomware | ▲ | CVE-2024-1212 | ▲ | Computers | ▲ |
| TAG-112 | ▲ | NodeStealer | ▲ | CVE-2024-8069 | ▲ | Central Bank | ▲ |
Prominent Information Security Events
Zoom Discloses Critical Vulnerabilities
Source: Insikt Group, Cybersecurity News | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
IOC: CVE-2024-45419 | CVVS Score: 6.9 | Recorded Future Risk Score: Medium – 30
IOC: CVE-2024-45420 | CVVS Score: 5.3 | Recorded Future Risk Score: Medium – 26
IOC: CVE-2024-45421 | CVVS Score: 7.7 | Recorded Future Risk Score: High – 66
IOC: CVE-2024-45418| CVVS Score: 5.3 | Recorded Future Risk Score: Medium – 35
Zoom disclosed several security vulnerabilities impacting its Workplace Apps, SDKs, and Rooms Clients across various platforms.
Two critical vulnerabilities stand out due to their severity, potentially enabling privilege escalation, sensitive data disclosure, and arbitrary code execution.
- CVE-2024-45419: An input validation flaw that could enable unauthorised access to sensitive information.
- CVE-2024-45421: A buffer overflow vulnerability that allows authenticated users to escalate privileges through network access.
These vulnerabilities impact several Zoom products, including Workplace Apps, Zoom Rooms Clients, the Zoom Video SDK, and the Zoom Meeting SDK, in versions before 6.2.0.
The report further details four additional vulnerabilities:
- CVE-2024-45422: Improper input validation in Zoom Apps.
- CVE-2024-45420: Uncontrolled resource consumption in Zoom Apps.
- CVE-2024-45418: Symbolic link following in Zoom Apps for macOS.
- CVE-2024-45417: Uncontrolled resource consumption in Zoom Apps for macOS.
Zoom strongly advises all users to update to version 6.2.0 or later to address these issues and mitigate potential risks.
NodeStealer Malware Steals Credit Card Data from Facebook Ads
Source: Insikt Group, The Hacker News | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: Internet Domain Name: nhansudaihoi13.org
IOC: Internet Domain Name: tocaoonline.org
IOC: SHA256: 768510fa9eb807bba9c3dcb3c7f87b771e20fa3d81247539e9ea4349205e39eb
IOC: SHA256: 69730f2c2bb9668a17f8dfa1f1523e0e1e997ba98f027ce98f5cbaa869347383
On November 21, The Hacker News reported on a campaign involving "NodeStealer," a malware targeting Facebook business accounts. NodeStealer compromises accounts by extracting login credentials and session cookies, allowing attackers to gain unauthorised access to tools like Facebook Ad Manager. This enables fraudulent activities such as running fake ads or siphoning financial resources.
The malware is distributed through phishing campaigns, where users are lured into downloading malicious software disguised as legitimate business tools. Once installed, NodeStealer exfiltrates sensitive data to a command-and-control server, bypassing detection with advanced evasion techniques.
Attackers leverage compromised accounts to launch large-scale scams, emphasising the sophistication of this threat. Facebook has been actively working to detect and counter these attacks, urging users to secure accounts with multi-factor authentication and to avoid downloading software from untrusted sources.
Organisations and individuals should also monitor account activity for unauthorised changes and employ endpoint security solutions to detect malware.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-45419 and CVE-2024-45421 – Update to version 6.2.0 or later to mitigate risks.
- CVE-2024-44308 and CVE-2024-44309 – Users should install updates immediately to prevent exploitation.
- CVE-2024-21287 – Oracle advises all users to update to supported versions to mitigate risks.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
