Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
CVE-2024-9249 - Foxit PDF Readere - This "Out-of-bounds Read" vulnerability in Foxit PDF Reader's PDF File Parser allows attackers to read data beyond intended limits, potentially accessing sensitive information and executing arbitrary code. It requires user interaction and has a CVSS score of 7.8. Users are advised to update to the latest version to mitigate these risks.
CVE-2024-7400 and CVE-2024-6654 – ESET Products for Windows macOS - On September 20, 2024, ESET patched two local privilege escalation vulnerabilities: CVE-2024-7400 allows low-privileged attackers to delete arbitrary files, impacting ESET NOD32 Antivirus, Internet Security, Endpoint Security, and others. CVE-2024-6654 lets users create a symlink, potentially disrupting ESET’s security tools. Affected versions include ESET Cyber Security 7.0 to 7.4.1600.0 and ESET Endpoint Antivirus for macOS 7.0 to 7.5.50.0.
CVE-2024-47076, CVE-2024-47175, CVE-2024-47176, CVE-2024-47177 - Four Common Unix Printing System - On September 27, 2024, four critical vulnerabilities were disclosed in the OpenPrinting CUPS system on Linux. They allow remote attackers to execute arbitrary code by exploiting insecure printer configurations. The flaws enable attackers to replace IPP URLs or inject malicious data through CUPS components, potentially leading to remote code execution. Patches are in development, and users are advised to disable the vulnerable service or restrict UDP port 631 traffic until updates are available.
Potential Threats
Detecting Voldemort Backdoor using YARA - On August 2024, Proofpoint identified a campaign delivering custom malware called “Voldemort”. This malware uses a distinctive attack chain that incorporates both common and rare command-and-control methods (e.g. Google Sheets) while impersonating government agencies. The attack was initially mistaken for a red team exercise but was later confirmed to involve genuine threat actors.
Vulnerability in NVIDIA Toolkit Affects Cloud AI - On September 26, 2024, Wiz reported a critical vulnerability in NVIDIA's Container Toolkit, tracked as CVE-2024-0132, affecting container images with default settings. This Time-of-Check Time-of-Use (TOCTOU) flaw could allow unauthorised access to the host's file system, leading to potential unauthorised code execution, service disruptions, elevated privileges, and data manipulation. Users are advised to address this vulnerability promptly due to its CVSS score of 9 out of 10.
Jupiter X Core Plugin Vulnerabilities Impact 90,000+ WordPress Sites - On September 26, 2024, Wordfence reported vulnerabilities in the Jupiter X Core WordPress plugin, affecting 90,000 sites. These flaws include an arbitrary file upload, enabling remote code execution, and an authentication bypass, potentially leading to account takeovers. Users are urged to update to version 4.7.8 to secure their sites.
General News
Global News Agency AFP Confirms Cyberattack - AFP disclosed a cyberattack on the 28th of September 2024, that briefly impacted its news systems. France’s cybersecurity agency ANSSI is assisting in investigating the breach. Despite the attack, AFP's global reporting continued uninterrupted.
Microsoft Enhances Recall Security After Controversy - Microsoft has updated its Recall feature for Copilot+ PCs to enhance security and address privacy concerns. Key improvements include user control, encryption, and Virtualization-based Security (VBS) Enclaves. Recall data is encrypted and stored locally, requiring users to opt in. Snapshots are not shared with Microsoft or third parties.
NCSC and FBI Warn of State-Backed Hacker Group - The NCSC and FBI warned about Iranian state-backed hackers conducting spear-phishing attacks to steal credentials. These attackers impersonate trusted contacts and target sensitive accounts.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
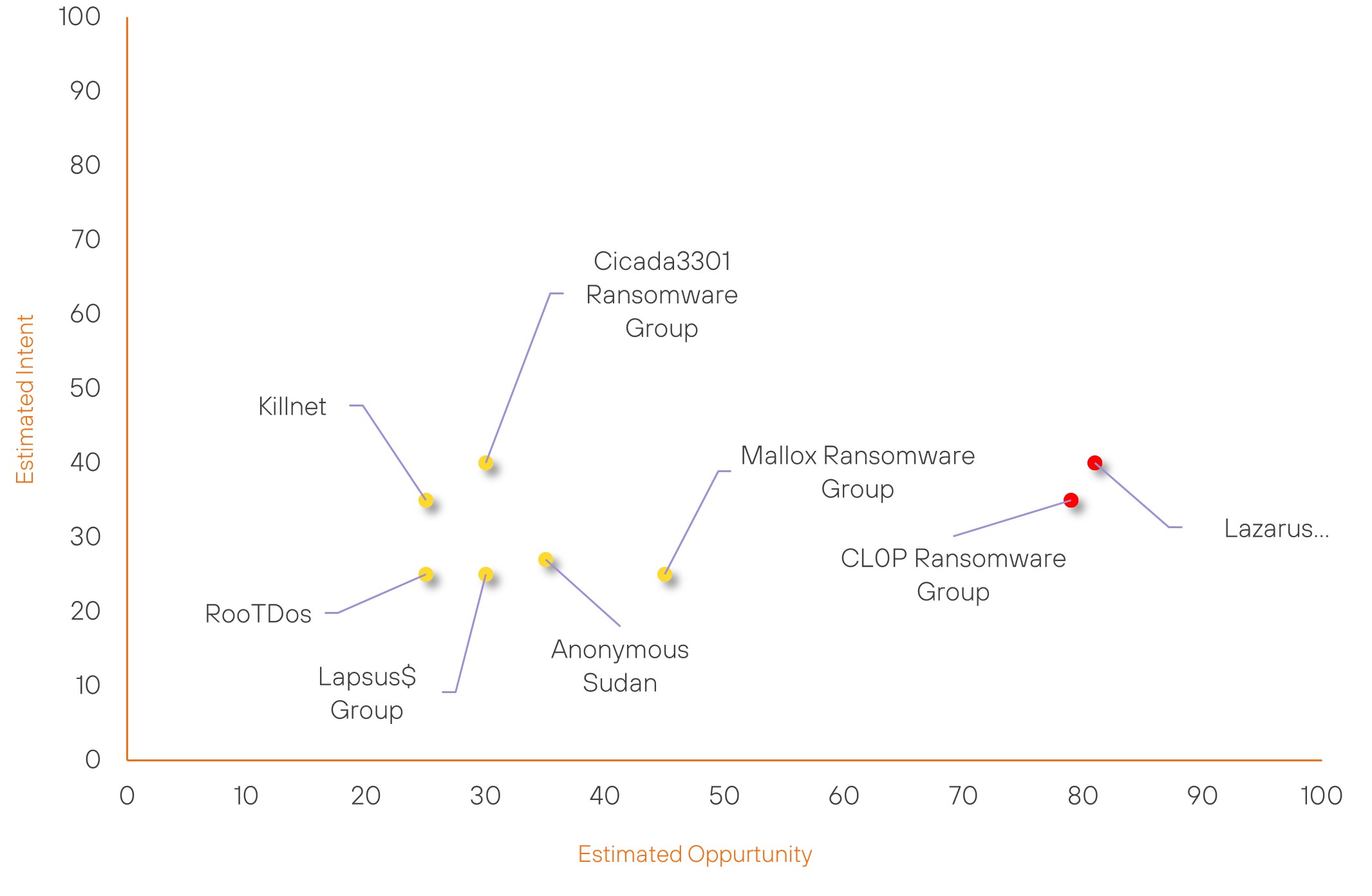
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| RooTDos | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| Mallox Ransomware Group | Basic | → | Basic | (45) | ↑ 15 | (25) | → 0 |
| Cicada3301 Ransomware Group | Basic | → | Basic | (30) | → 0 | (40) | ↑ 5 |
| Lazarus Group | High | → | High | (81) | ↓ 1 | (40) | → 0 |
| Anonymous Sudan | Basic | → | Basic | (35) | → 0 | (27) | ↓ 1 |
| Killnet | Basic | → | Basic | (25) | ↓ 5 | (25) | → 0 |
| Lapsus$ Group | Basic | → | Basic | (30) | ↓ 5 | (25) | → 0 |
| CL0P Ransomware Group | High | → | High | (79) | → 0 | (35) | ↓ 5 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Medusa Ransomware Group | ▲ | Cryptojacking | ▲ | CVE-2023-29689 | ▲ | Consumer Electronics | ▲ |
| Kimsuky | ▲ | Zero Day Exploit | ▲ | CVE-2024-26808 | ▲ | Sony | ▲ |
| TIDrone | ▲ | LockBit Ransomware | ▲ | CVE-2024-28987 | ▲ | Verizon | ▲ |
| @ZachLowe_NBA | ▲ | T1068 (Exploitation for Privilege Escalation) | ▲ | CVE-2024-5932 | ▲ | ▲ | |
| Handala | ▲ | TA0002 (Execution) | ▲ | CVE-2024-6769 | ▲ | Cloud Computing | ▲ |
Prominent Information Security Events
CVE-2024-7400 and CVE-2024-6654 – ESET Products for Windows and macOS
Source: Insikt Group, Security Week | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-7400 | CVVS Score: 8.5 | Recorded Future Risk Score: Medium – 38
CVE-2024-6654 | CVVS Score: 6.8 | Recorded Future Risk Score: Medium – 34
On September 23, 2024, ESET announced patches for two local privilege escalation vulnerabilities affecting multiple Windows and macOS products.
CVE-2024-7400
This high-severity vulnerability impacts ESET's handling of file operations during the removal of detected files. An attacker with low privileges could exploit this flaw to delete arbitrary files and escalate their privileges.
ESET has fixed the issue in the Cleaner module 1251, which was distributed automatically to customers, and advises users to ensure their products are regularly updated.
As of now, ESET reports that there are no known exploits for this vulnerability in the wild.
CVE-2024-6654
This medium-severity vulnerability affects ESET Cyber Security versions 7.0 to 7.4.1600.0 and Endpoint Security for macOS versions 7.0 – 7.5.50.0. It allows a low-privileged user to plant a symlink, potentially leading to a denial-of-service attack that could disrupt the functioning of ESET's security tools and slow down the system.
ESET addressed this vulnerability in Cyber Security version 7.5.74.0 and Endpoint Security for macOS version 8.0.7200.0. Like CVE-2024-7400, there are currently no reports of in-the-wild exploitation attempts.
Vulnerability in NVIDIA Toolkit Affects Cloud AI
Source: Insikt Group, Wiz Research | Validated Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-0132 | CVVS Score: 7.7 | Recorded Future Risk Score: High – 79
On September 26, 2024, Wiz Research disclosed a critical security vulnerability, CVE-2024-0132, in the NVIDIA Container Toolkit, which is widely used for enabling AI applications to access GPU resources. This vulnerability allows attackers controlling a vulnerable container image to escape the container and gain full access to the host system, posing serious risks to sensitive data and infrastructure.
This vulnerability impacts all versions of the NVIDIA Container Toolkit up to v1.16.1 and the NVIDIA GPU Operator up to v24.6.1. It poses significant risks, particularly in environments that permit third-party container images, such as single-tenant or orchestrated environments like Kubernetes.
Organisations should prioritise upgrading to the latest versions to mitigate risks, focusing on container hosts that may run untrusted images. Note that internet exposure is not a factor; initial access could occur through social engineering or supply chain attacks.
Wiz researchers initiated this investigation due to concerns over shared GPU resources in AI service providers, leading to the discovery of vulnerabilities in the NVIDIA Container Toolkit that could facilitate container breakout attacks.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-9249 – Upgrade Foxit PDF reader to version 1.16.2 or later.
- CVE-2024-7400 and CVE-2024-6654 – Upgrade to the latest versions of ESET for both Mac and Windows
- CVE-2024-47076, CVE-2024-47175, CVE-2024-47176, and CVE-2024-47177 – Due to the recent disclosure of these vulnerabilities, remediation efforts are still underway, and patches are being developed.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
