Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
NVIDIA Updates for GPU and vGPU Vulnerabilities - On 22 October 2024, NVIDIA addressed critical vulnerabilities allowing unauthorised code execution and data access. CVE-2024-0126 affects GPU drivers, while CVE-2024-0117 to CVE-2024-0121 impact Windows GPU drivers. CVE-2024-0127 concerns the vGPU kernel driver, and CVE-2024-0128 poses a risk of information disclosure in the vGPU Manager. No known exploits exist.
OS Downgrade Vulnerability Discovered in Microsoft Windows Kernel - On 28 October 2024, The Hacker News reported an OS downgrade vulnerability in Microsoft Windows, linked to CVE-2024-21302 and CVE-2024-38202. This flaw allows attackers to bypass Driver Signature Enforcement, enabling the loading of unsigned kernel drivers and potentially deploying rootkits. Currently, there are no known exploitations.
VMware fixes flawed patch for critical vCenter Server RCE - On 21 October 2024, VMware patched two critical vulnerabilities, CVE-2024-38812 and CVE-2024-38813, in its vCenter Server and Cloud Foundation. CVE-2024-38812, a heap overflow flaw, could allow remote code execution via a malicious packet, while CVE-2024-38813 could enable privilege escalation to the root. Currently, there are no reports of exploitation. VMware recommends updating to the latest versions to mitigate risks.
Potential Threats
AWS CDK Vulnerability - On October 24, 2024, Aqua Security disclosed a critical vulnerability in the Amazon Web Services (AWS) Cloud Development Kit (CDK) that could enable threat actors to gain administrative access to affected user accounts. This vulnerability impacts all CDK versions before v2.149.0. To date, no exploitations have been confirmed.
BlackBasta Ransomware Group Targets Microsoft Teams Users - The Black Basta Ransomware Group has shifted its tactics to Microsoft Teams, posing as IT support to target employees across various sectors. According to a report by ReliaQuest on 25 October 2024, the group sends spam emails offering to resolve issues, tricking employees into installing remote access tools like AnyDesk or Quick Assist to deploy ransomware.
Threat Actors Abuse Docker Remote APIs in New Cryptomining Campaign to Deploy SRBMiner - On 22 October 2024, Trend Micro reported a campaign where threat actors exploit misconfigured Docker remote API servers to deploy SRBMiner, a cryptocurrency miner. By using Google gRPC over HTTP/2, they bypass security measures and mine cryptocurrencies like Ripple (XRP). This campaign specifically targets the vulnerable remote management features of the Docker API.
General News
LinkedIn Fined $335 Million for Data Misuse - LinkedIn was penalised by Ireland's privacy regulator for using member data for ad targeting without consent.
SEC Charges 4 Companies Over Misleading SolarWinds Cyber Attack Disclosures - The SEC has filed charges against Avaya, Check Point, Mimecast, and Unisys for providing misleading information regarding the impact of the 2020 SolarWinds cyberattack.
Delta Sues CrowdStrike for $500 Million Over July Outage - Delta Air Lines has filed a $500 million lawsuit against CrowdStrike, claiming that the cybersecurity firm cut corners, leading to a significant outage in July 2024. Delta alleges that the outage disrupted operations and caused substantial financial losses.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
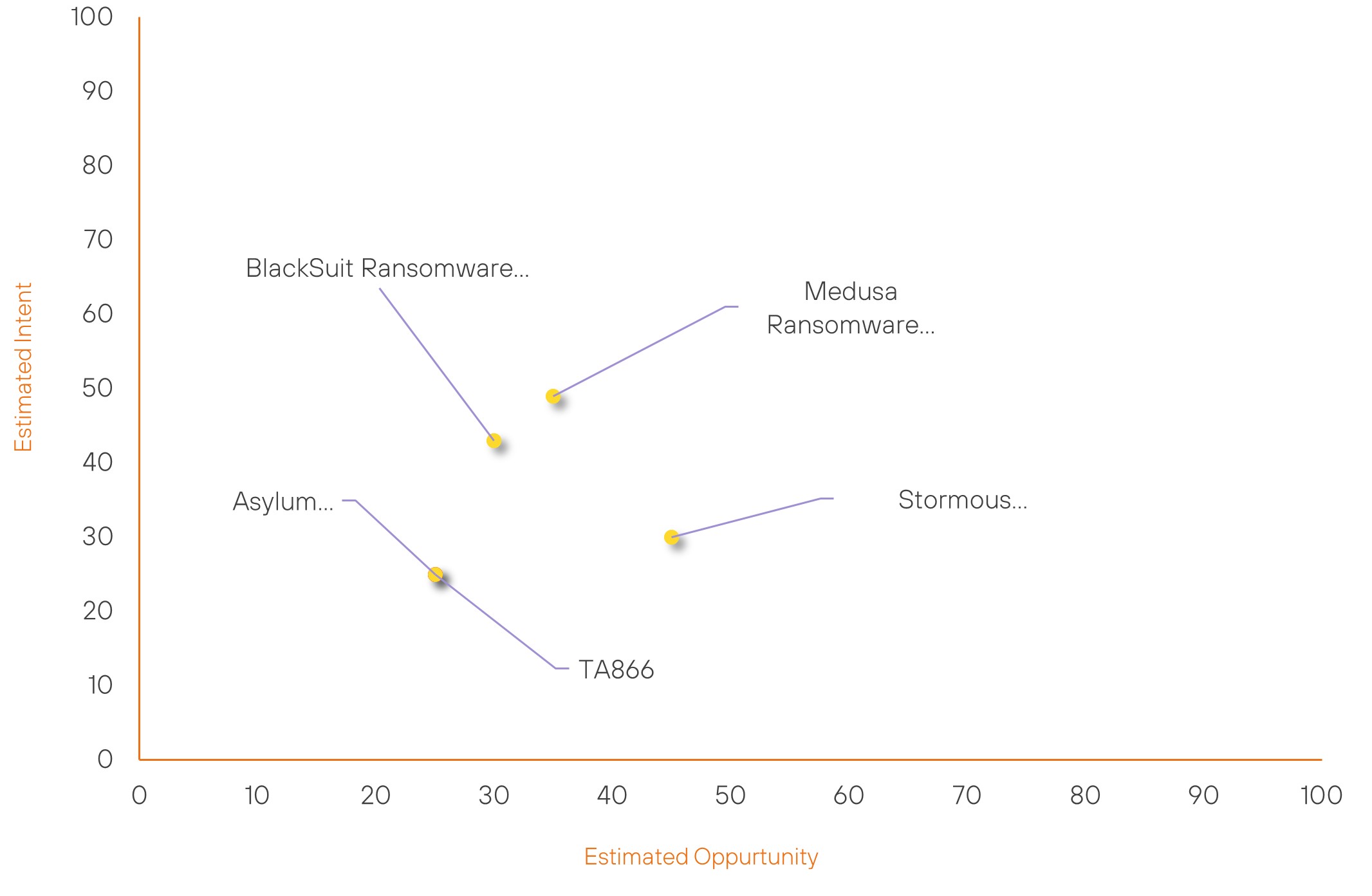
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Asylum Ambuscade | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| TA866 | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| Medusa Ransomware Group | Basic | → | Basic | (35) | ↓ 5 | (49) | → 0 |
| Stormous Ransomware Group | Basic | → | Basic | (45) | ↑ 5 | (30) | → 0 |
| BlackSuit Ransomware Group | Basic | → | Basic | (30) | → 0 | (43) | ↑ 5 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Salt Typhoon | ▲ | Powershell Attack | ▲ | CVE-2024-1040 | ▲ | DER SPIEGEL | ▲ |
| Handala | ▲ | HOMESTEEL | ▲ | CVE-2024-40766 | ▲ | Communications | ▲ |
| APT34 OilRig | ▲ | Automated Exfiltration | ▲ | CVE-2024-9264 | ▲ | Telecommunication | ▲ |
| Lazarus Group | ▲ | Cobalt Strike | ▲ | CVE-2024-38094 | ▲ | Wireless Networking | ▲ |
| UAC-0218 | ▲ | Data Exfiltration | ▲ | CVE-2024-38812 | ▲ | Consumer Electronics | ▲ |
Prominent Information Security Events
OS Downgrade Vulnerability Discovered in Microsoft Windows Kernel.
Source: Insikt Group, The Hacker News | Validated Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-21302 | CVVS Score: 6.7 | Recorded Future Risk Score: Medium – 64
CVE-2024-38202 | CVVS Score: 6.9 | Recorded Future Risk Score: Medium – 64
On October 28, 2024, The Hacker News reported an OS downgrade vulnerability in Microsoft Windows associated with CVE-2024-21302 and CVE-2024-38202. A new technique allows attackers to bypass Microsoft’s Driver Signature Enforcement (DSE) on fully patched systems, enabling the loading of unsigned kernel drivers and the deployment of custom rootkits that can evade detection.
Researcher Alon Leviev highlighted that this method serves as an alternative to Bring Your Own Vulnerable Driver (BYOVD) attacks by downgrading critical components like the OS kernel. Although Microsoft addressed these vulnerabilities earlier in 2024, Leviev's technique exploits the Windows Downdate tool to revert DSE patches on Windows 11.
The exploit takes advantage of a race condition to load malicious unsigned drivers by deceiving the system’s code integrity checks. While Virtualization-Based Security (VBS) could mitigate such attacks, it is often configured without UEFI lock, which allows attackers to disable it via registry modifications. In the absence of UEFI lock and with the "Mandatory" setting not enforced, DSE protections can be circumvented. Leviev emphasised the need for security systems to detect and prevent downgrade procedures, even for components outside defined security boundaries.
Affected Systems:
- Microsoft Windows 10
- Microsoft Windows 11
- Microsoft Windows Server 2016
- Microsoft Windows Server 2019
BlackBasta Ransomware Group Targets Microsoft Teams Users.
Source: Insikt Group, Bleeping Computer | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: File Name: AntispamAccount.exe
IOC: File Name: AntispamUpdate.exe
IOC: File Name: AntispamConnectUS.exe.
IOC: Entra ID Tenants: securityadminhelper.onmicrosoft.com
IOC: Entra ID Tenants: supportserviceadmin.onmicrosoft.com
On October 25, 2024, ReliaQuest reported on the Black Basta Ransomware Group, which has shifted its focus to Microsoft Teams, impersonating IT support to target employees across various sectors. This group distributes phishing emails claiming to resolve IT issues, tricking users into installing remote access tools like AnyDesk and Quick Assist, which facilitates the deployment of ransomware.
The Black Basta Group's tactics leverage Microsoft Teams for social engineering, effectively exploiting a trusted platform. Once installed, the remote access tools allow the attackers to breach networks, leading to potential data encryption and ransom demands. Reports indicate that the group’s activity has increased, highlighting the importance of employee training and awareness regarding phishing attempts and suspicious communications. Organisations are urged to implement robust security measures and monitor for unauthorised remote access.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned be fully patched and updated. We also want to highlight and recommend applying the following patches where applicable:
- CVE-2024-0117 to CVE-2024-012, CVE-2024-0126 to CVE-2024-0128 - Users are advised to apply the available patches.
- CVE-2024-21302 and CVE-2024-38202 - Apply recent security patches, enable VBS with UEFI Lock and Mandatory Mode and monitor for unauthorised downgrades.
- CVE-2024-38812 and CVE-2024-38813 - Updating to the latest versions.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing related searching and hunting activities within your environment.
