Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
CVE-2024-37085 - VMware ESXi Authentication Bypass Vulnerability - This vulnerability affects VMware ESXi and related products. It allows attackers with sufficient Active Directory (AD) permissions to gain full access to ESXi hosts by exploiting a flaw that occurs when the 'ESXi Admins' group is deleted and re-created. It has a CVSS score of up to 7.2.
CVE-2024-39584 - Dell BIOS Vulnerability – This vulnerability impacts the BIOS of Alienware and select Dell series laptops, including Alienware Area 51m R2, Aurora R15 AMD, and various m15, m17, x14, x15, and x17 series models. It allows attackers with administrative privileges to bypass Secure Boot and execute unauthorised code due to a default cryptographic key flaw. The vulnerability is severe, but no active exploits are known as of now.
PoC for Critical RCE Vulnerability in WordPress Plugin (CVE-2024-6386) - On August 26, 2024, Wordfence released a proof-of-concept (PoC) exploit for a critical Remote Code Execution (RCE) vulnerability affecting the WordPress Multilingual Plugin (WPML) up to version 4.6.12. This flaw, caused by improper input validation in the Twig templating engine, allows authenticated users with Contributor-level access to execute arbitrary code on the server.
Potential Threats
Voldemort Backdoor Uses Google Sheets for C2 - Reported on August 30, 2024, the Voldemort backdoor uses Google Sheets as a command-and-control server. Delivered via phishing emails impersonating tax authorities, it executes commands and exfiltrates data through Google Sheets, making detection difficult. The campaign has targeted over 70 organisations across various sectors.
Corona Mirai Botnet Exploits CVE-2024-7029 - Reported on August 28, 2024, the Corona Mirai botnet exploits a command injection vulnerability in AVTECH IP cameras, allowing for remote code execution. This flaw enables the botnet to spread and launch DDoS attacks. No patch is available yet.
Citrine Sleet Exploits Chromium Zero-Day for FudModule Rootkit - Microsoft reported on August 30, 2024, that Citrine Sleet targets the cryptocurrency sector by exploiting CVE-2024-7971 in Chromium and CVE-2024-38106 in Windows to deploy the FudModule rootkit for persistent access.
General News
NHS Scotland Staff Mobile Numbers Exposed - On August 29, 2024, NHS Scotland revealed that staff mobile numbers were compromised in a cyber incident linked to a third-party supplier. NHS Grampian reported that only generic text messages were affected, with no personal data or patient information at risk.
Microsoft Patches Vulnerability in 365 Copilot - On September 2, 2024, Microsoft addressed a critical flaw in Microsoft 365 Copilot that allowed ASCII smuggling to exfiltrate sensitive data. Users are advised to update their software and be cautious with links to mitigate risks.
German Air Traffic Control Agency Confirms Cyberattack - On September 2, 2024, Deutsche Flugsicherung confirmed a cyberattack affecting its administrative IT systems but assured that air traffic control operations and flight safety were not impacted.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
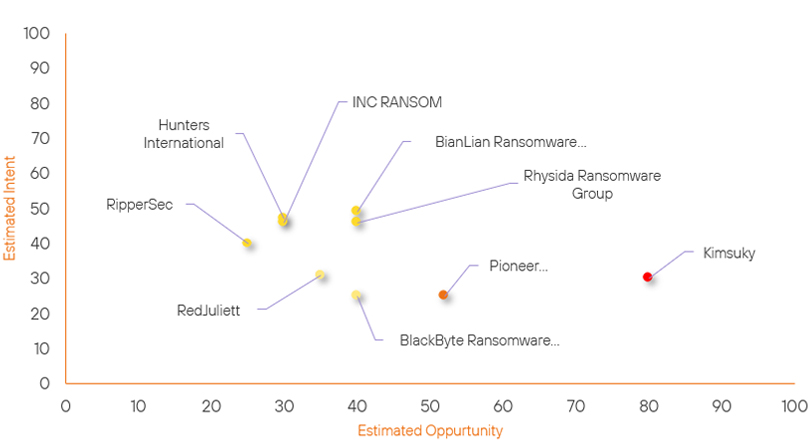
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Pioneer Kitten | New | → | Moderate | (52) | ↑ 52 | (25) | ↑ 25 |
| Rhysida Ransomware Group | Basic | → | Basic | (40) | → 0 | (46) | ↑ 5 |
| RipperSec | Basic | → | Basic | (25) | → 0 | (40) | ↑ 5 |
| Hunters International | Basic | → | Basic | (30) | → 0 | (47) | ↑ 5 |
| BlackByte Ransomware Gang | Basic | → | Basic | (40) | ↑ 5 | (25) | → 0 |
| Kimsuky | High | → | High | (80) | ↑ 1 | (30) | → 0 |
| BianLian Ransomware Group | Basic | → | Basic | (40) | ↓ 5 | (49) | → 0 |
| INC RANSOM | Basic | → | Basic | (30) | ↓ 5 | (46) | → 0 |
| RedJuliett | Basic | → | Basic | (35) | ↓ 5 | (31) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| BlueDelta | ▲ | noblox.js | ▲ | CVE-2024-43044 | ▲ | Transportation | ▲ |
| RansomHub Ransomware Group | ▲ | Zero Day Exploit | ▲ | CVE-2024-7971 | ▲ | Air Traffic Control | ▲ |
| Chinese Hackers | ▲ | Brandjacking | ▲ | CVE-2023-3883 | ▲ | Electronics | ▲ |
| North Korean Hackers | ▲ | RansomHub Ransomware | ▲ | CVE-2023-22527 | ▲ | Radar | ▲ |
| DEV-0139 | ▲ | Credential Stuffing | ▲ | CVE-2024-6670 | ▲ | Pharmaceuticals | ▲ |
Prominent Information Security Events
CrushFTP CVE-2024-4040.
Source: Insikt Group, The Hacker News | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-37085 | CVVS Score: 7.2 | Recorded Future Risk Score: Critical - 89
IOC: SHA256: 0296e2ce999e67c76352613a718e11516fe1b0efc3ffdb8918fc999dd76a73a5
IOC: SHA256: 543991ca8d1c65113dff039b85ae3f9a87f503daec30f46929fd454bc57e5a91
IOC: SHA256: 31f4cfb4c71da44120752721103a16512444c13c2ac2d857a7e6f13cb679b427
IOC: IP: 204.79.197.219
CVE-2024-37085 allows a malicious actor with sufficient Active Directory (AD) permissions to gain full access to an ESXi host that was previously configured to use AD for user management. This can be achieved by re-creating the configured AD group (default name: 'ESXi Admins') after that group has been deleted from AD, effectively bypassing authentication mechanisms.
Successfully exploiting this vulnerability can lead to high impacts on confidentiality, integrity, and availability of systems. Attackers can gain administrative privileges on the ESXi hosts, which could allow them to perform unauthorised actions or deploy further attacks. This activity has been seen in relation to the BlackByte ransomware group, we have included known IOCs from a known ongoing campaign using this exploit.
This vulnerability impacts several versions of VMware ESXi, including:
- VMware ESXi 7.0 Update 2a
- VMware ESXi 7.0 Update 2
- VMware ESXi 7.0 Update 1d
- VMware Cloud Foundation 4.4.1.1
Organisations using affected VMware products are strongly advised to apply the necessary patches to mitigate this vulnerability and secure their systems against potential exploitation.
Corona Mirai Botnet Spreads via Zero-Day
Source: Insikt Group, Akamai | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
IOC: SHA256: 8ac82a770cffbbc8fba73554d7caa117ef6d37ffee468665b95bc406449f91b5
IOC: SHA256: b0f7ef937d77061515907c54967a44da3701e0d2af143164bbf44bb4fc6f26af
IOC: IP: 147.78.103.177
IOC: IP: 185.216.70.142
On August 28, 2024, Akamai reported a new botnet campaign exploiting CVE-2024-7029, a zero-day vulnerability in AVTECH IP cameras that allows remote code execution (RCE).
The attack leverages this vulnerability in the brightness function of the cameras to spread a variant of the Mirai botnet known as Corona Mirai, which has been active since 2020. This variant connects to hosts via Telnet and also exploits other vulnerabilities like CVE-2017-17215 and CVE-2014-8361.
After initial infection, the malware spreads across systems, displaying "Corona" on compromised devices and establishing command and control connections. If successfully exploited, this vulnerability can significantly compromise system integrity, confidentiality, and availability. Infected devices may be used for various malicious activities, including Denial of Service (DoS) attacks and other botnet-related purposes.
Users of AVTECH IP cameras are strongly urged to secure their devices, which may include network segmentation, firewall rules to limit incoming connections, and monitoring for unusual activity.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- CVE-2024-37085 – Apply the necessary patches
- CVE-2024-39584 – Update to the latest patched BIOS versions released by Dell
- CVE-2024-6386 – Users of the WPML plugin are strongly advised to update to version 4.6.13 or later.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
