Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
CVE-2024-38811 - VMware Fusion Code Execution Vulnerability - This vulnerability affects VMware Fusion versions 13.x before 13.6. It allows attackers with standard user privileges to execute arbitrary code within the context of the Fusion application by exploiting an insecure environment variable. If successfully exploited, the vulnerability can lead to system compromise without requiring elevated privileges. It has a CVSS score of up to 8.8.
PoC for High-Severity Vulnerability in Linux Kernel's Netfilter (CVE-2024-26581) - On September 7, 2024, Google released a PoC for a high-severity flaw in the Linux kernel's Netfilter, specifically affecting the "nft_set_rbtree" function in nftables. This issue involves improper memory handling during transaction rollbacks, causing a use-after-free condition. Local authenticated attackers can exploit this to leak sensitive data, escalate privileges, and execute unauthorised code.
CVE-2024-40766 - SonicWall SSLVPN Access Control Vulnerability - This vulnerability affects SonicWall Firewall devices running SonicOS versions 7.0.1-5035 and earlier. It is an improper access control issue that could allow unauthorised access and potentially cause the firewall to crash, compromising network security. It has a CVSS score of 9.4.
Potential Threats
SpyAgent Mobile Malware Targets Crypto Wallets - Reported on September 5, 2024, McAfee's Mobile Research Team discovered SpyAgent, a mobile malware for Android that steals cryptocurrency wallet recovery phrases. Disguised as banking or government apps, it scans photos, text messages, and contacts for mnemonic keys. SpyAgent spreads via phishing and deceptive APK downloads, requesting extensive permissions and sending stolen data to a remote server.
PyPI Packages Vulnerable to "Revival Hijack" - Reported on September 4, 2024, JFrog found over 22,000 PyPI packages at risk from a "Revival Hijack" attack, where deleted package names are reused to deploy malicious payloads. Unlike typosquatting, this method targets automated environments like CI/CD pipelines.
DarkCracks Malware Framework Discovered - On September 4, 2024, XLab published a detailed analysis of DarkCracks, an advanced stealthy payload delivery and upgrade framework. DarkCracks exploits compromised GLPI and WordPress sites as downloaders and C2 servers, targeting public service systems such as school websites and public transportation.
General News
Payment Gateway Data Breach - On September 4, 2024, it was reported that a payment gateway data breach exposed sensitive information of approximately 17 million credit card holders. The breach involved compromised payment details, potentially leading to financial loss and identity theft.
Rambo Attack Exposes Air-Gapped Systems - On September 4, 2024, researchers revealed "Rambo," a new attack technique that extracts data from air-gapped systems via electromagnetic signals, bypassing traditional security measures.
Predator Spyware Resurfaces with New Infrastructure - On September 4, 2024, Recorded Future reported that Predator spyware has resurfaced with new infrastructure, continuing its operations of targeting and exfiltrating sensitive information.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
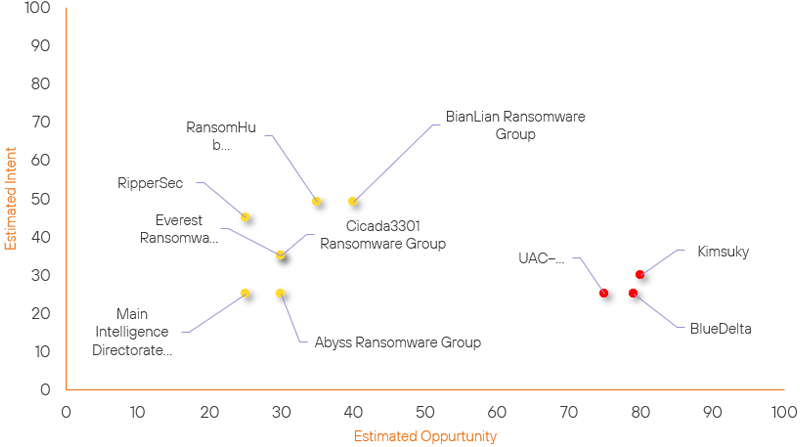
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| UAC–0056 | New | → | High | (75) | ↑ 75 | (25) | ↑ 25 |
| Cicada3301 Ransomware Group | New | → | Basic | (30) | ↑ 30 |
(35) | ↑ 35 |
| Everest Ransomware Group | New | → | Basic | (30) | ↑ 30 | (35) | ↑ 35 |
| Main Intelligence Directorate (GRU) | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| Abyss Ransomware Group | Basic | → | Basic | (30) | ↑ 5 | (25) | → 0 |
| RansomHub Ransomware Group | Basic | → | Basic | (35) | ↑ 5 | (49) | → 0 |
| RipperSec | Basic | → | Basic | (25) | → 0 | (45) | ↑ 5 |
| BlueDelta | High | → | High | (79) | ↑ 1 | (25) | → 0 |
| Kimsuky | High | → | High | (80) | ↑ 1 | (30) | → 0 |
| BianLian Ransomware Group | Basic | → | Basic | (40) | ↓ 10 | (49) | → 0 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| Main Intelligence Directorate (GRU) | ▲ | QuasarRAT | ▲ | CVE-2024-36401 | ▲ | AVIS, INC. | ▲ |
| APT-C-36 | ▲ | WhisperGate | ▲ | CVE-2024-40766 | ▲ | Cisco Systems Inc | ▲ |
| RedDelta | ▲ | Disinformation | ▲ | CVE-2024-26230 | ▲ | Consumer Goods | ▲ |
| DEV-0586 (Cadet Blizzard) | ▲ | Identity Theft | ▲ | CVE-2024-40711 | ▲ | POS devices | ▲ |
| Moroccan Black Cyber Army | ▲ | Rootkit | ▲ | CVE-2024-20017 | ▲ | ▲ | |
Prominent Information Security Events
CVE-2024-38811 - VMware Fusion Code Execution Vulnerability
Source: Insikt Group, The Hacker News | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-38811 | CVVS Score: 8.8 | Recorded Future Risk Score: High – 74
On September 5, 2024, VMware released a critical security update to address CVE-2024-38811, a high-severity vulnerability in VMware Fusion. The vulnerability is caused by an insecure environment variable, which allows a standard user to execute arbitrary code within the Fusion application, potentially leading to full system compromise.
Exploiting this vulnerability could severely affect system confidentiality, integrity, and availability, allowing unauthorised access and control over the affected systems.
This issue highlights the ongoing need for vigilance in securing software environments, particularly those that handle critical or sensitive information. The vulnerability’s potential to allow arbitrary code execution underscores the importance of timely updates and proactive security measures.
Affected Products:
- VMware Fusion 13.0
- VMware Fusion 13.1
- VMware Fusion 13.2
- VMware Fusion 13.3
- VMware Fusion 13.4
- VMware Fusion 13.5
Organisations using the affected versions of VMware Fusion are strongly encouraged to apply the necessary patches as soon as possible to mitigate risks and safeguard their systems.
SpyAgent Mobile Malware Targets Crypto Wallets
Source: Insikt Group, McAfee | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: SHA256: 4cf35835637e3a16da8e285c1b531b3f56e1cc1d8f6586a7e6d26dd333b89fcf
IOC: SHA256: 34c2a314dcbb5230bf79e85beaf03c8cee1db2b784adf77237ec425a533ec634
IOC: SHA256: 149bd232175659434bbeed9f12c8dd369d888b22afaf2faabc684c8ff2096f8c
On September 4, 2024, McAfee’s Mobile Research Team uncovered SpyAgent, a sophisticated Android malware campaign targeting cryptocurrency users. Active since January 2024, SpyAgent steals mnemonic keys—12-word phrases essential for recovering cryptocurrency wallets—by disguising itself as legitimate apps, such as banking and government applications.
The malware spreads through phishing campaigns and deceptive APK downloads, with over 280 fake apps identified, mainly targeting users in South Korea. Once installed, SpyAgent scans photos, messages, and contacts on infected devices to extract sensitive information.
This campaign highlights critical vulnerabilities within the Android ecosystem and underscores the need for heightened security measures, such as careful scrutiny of app permissions and sources.
The rise in cryptocurrency usage has made such attacks increasingly attractive to cybercriminals, reflecting broader trends in targeting financial information via mobile platforms.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- CVE-2024-38811 – Update to the latest version
- CVE-2024-26581 – Update to kernel version 6.8-rc4 or later
- CVE-2024-40776 – Update to the latest version
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
