Executive Summary -
Highlights of Cyber Threat Intelligence Digest
Vulnerabilities
CVE-2024-41869 Use-After-Free Vulnerability in Acrobat and Acrobat Reader - On September 10, 2024, Adobe released a secondary patch for a critical-severity vulnerability in Acrobat and Acrobat Reader, tracked as CVE-2024-41869. Although Adobe issued an initial patch on August 13, 2024, it did not fully resolve CVE-2024-41869, which meant that the flaw could still be exploited.
Ivanti Patches Actively Exploited Command Injection Vulnerability (CVE-2024-8190) - On September 13, 2024, Ivanti reported an actively exploited vulnerability affecting its Cloud Services Appliance (CSA), tracked as CVE-2024-8190. Ivanti CSA is a secure gateway that enables remote access and authentication for enterprise networks.
Intel Discloses UEFI and RAID Software Vulnerabilities in Servers, Workstations, and Mobile Devices - These vulnerabilities affect products including Intel Atom, Xeon, Pentium, Celeron, and Core processor families and extend to servers, workstations, mobile devices, and embedded systems.
Potential Threats
WhatsApp's "View Once" Feature Actively Exploited by Threat Actors - A privacy flaw in WhatsApp's "View once" media feature allows threat actors to bypass its protections and view or save messages intended to be seen only once. Meta has acknowledged the issue and said that updates to address this flaw are being rolled out, particularly for WhatsApp Web.
Scattered Spider Targets Cloud Infrastructure Using Smishing and Vishing Attacks - According to a report by EclecticIQ on September 10, 2024, the threat actors use vishing and smishing attacks targeting companies' IT service desks and identity administrators to gain unauthorised access and manipulate multi-factor authentication settings.
Large-Scale Phishing Campaign Uses HTTP Response Header Refresh Entry - A new phishing campaign uses HTTP response header refresh to target businesses, government, and educational organisations. According to a report by Palo Alto on September 11, 2024, this large-scale phishing attack used over 2,000 malicious URLs daily from May to July 2024. These attacks exploit the server’s response header to redirect users to a malicious page without their interaction automatically.
General News
Data on nearly 1 million NHS patients leaked online following ransomware attack on London hospitals - The stolen data, which was published in June by the Qilin ransomware gang, includes requests for appointments as well as for pathology and histology tests. It features in many cases details of symptoms for sensitive medical conditions that patients may not yet know have been exposed.
Fortinet says hackers accessed ‘limited’ number of customer files on third-party drive - The file drive “included limited data related to a small number of Fortinet customers,” and the company said it has communicated directly with customers “as appropriate.”
Hackers have sights set on four Microsoft vulnerabilities, CISA warns - The four bugs - CVE-2024-38226, CVE-2024-43491, CVE-2024-38014 and CVE-2024-38217 - were part of the 79 vulnerabilities included in the monthly security release from Microsoft.
Threat Actor Weekly Graph
Over the past 7 days, we have been tracking the following intent and opportunity changes within our Threat Actor Landscape.
Intent represents the potential targets of a group. When a group is observed attacking a different organisation or entity, their intent will increase.
Opportunity represents the various methods and technologies these groups may use. For example, if a group started using a new attack vector, such as a new kind of ransomware, their opportunity would increase.
Both intent and opportunity are scored out of 100 and are responsible for scoring the group’s severity. These updates can be seen below.
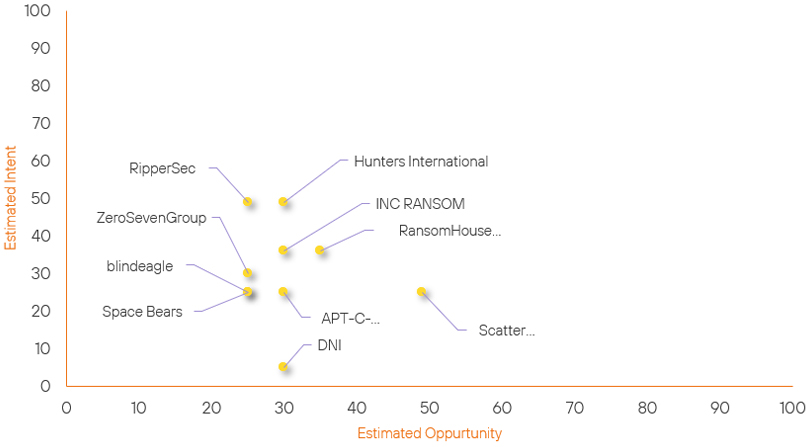
| ● Limited Severity | ● Basic Severity | ● Moderate Severity | ● High Severity |
| Threat Actor | Severity Change | Opportunity Change | Intent Change | ||||
|---|---|---|---|---|---|---|---|
| Scattered Spider | New | → | Basic | (49) | ↑ 49 | (25) | ↑ 25 |
| ZeroSevenGroup | New | → | Basic | (25) | ↑ 25 | (30) | ↑ 30 |
| blindeagle | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| Space Bears | New | → | Basic | (25) | ↑ 25 | (25) | ↑ 25 |
| DNI | New | → | Basic | (30) | ↑ 30 | (5) | ↑ 5 |
| APT-C-36 | Basic | → | Basic | (30) | ↑ 5 | (25) | → 0 |
| RipperSec | Basic | → | Basic | (25) | → 0 | (49) | ↑ 4 |
| Hunters International | Basic | → | Basic | (30) | → 0 | (49) | ↑ 2 |
| RansomHouse Group | Basic | → | Basic | (35) | → 0 | (36) | ↓ 5 |
| INC RANSOM | Basic | → | Basic | (30) | → 0 | (36) | ↓ 10 |
Global Trends Powered by Recorded Future
Within each category, we have provided the current top five globally trending items. Each item is linked to how actively trending it is and is marked with a small symbol.
The spikes in references are calculated over 60 days and are normalised to ensure they aren’t disproportionate when compared to bigger entities that will naturally have more baseline mentions.
▲- Spike – This indicates a large increase in reporting volume and a high diversity in the event descriptions,
▲- Rise – This indicates a small increase in reporting volume with little diversity in the descriptions.
| Attackers | Methods | Vulnerabilities | Targets | ||||
|---|---|---|---|---|---|---|---|
| BianLian Ransomware Group | ▲ | RustDoor | ▲ | CVE-2024-43461 | ▲ | Python | ▲ |
| RansomHub Ransomware Group | ▲ | Cyber Spying | ▲ | CVE-2024-29847 | ▲ | 23andMe | ▲ |
| Rhysida Ransomware Group | ▲ | EVEREST Ransomware | ▲ | CVE-2024-38080 | ▲ | Kawasaki Motors Europe | ▲ |
| Krasser | ▲ | Lockbit Ransomware | ▲ | CVE-2024-8503 | ▲ | Fortinet | ▲ |
| RedDelta | ▲ | Fileless Malware | ▲ | Fileless Malware | ▲ | Cisco Duo | ▲ |
Prominent Information Security Events
Large-Scale Phishing Campaign Uses HTTP Response Header Refresh Entry
Source: Insikt Group, Palo Alto | Validated Intelligence Event
Intelligence Cards: Intelligence & Reports
IOC: 195[.]19[.]93[.]5
IOC: edreams[.]onelink[.]me
IOC: opodo[.]onelink[.]me
IOC: hk6[.]8ik8rq[.]ru
IOC: 2127394249@docusign[.]com
IOC: 2127394249@businessimageprint[.]com
A new phishing campaign uses HTTP response header refresh to target organisations in the business, government, and educational sectors. According to a report by Palo Alto on September 11, 2024, this large-scale phishing attack used over 2,000 malicious URLs daily from May to July 2024.
Unlike typical phishing schemes embedded within the HTML content of a webpage, these attacks exploit the server’s response header to automatically redirect users to a malicious page without their interaction.
The infection chain starts with a phishing email containing a malicious URL disguised as a legitimate domain. When the victim clicks the link, the HTTP response header triggers an automatic redirection to a secondary URL before the initial page even loads.
This redirection is invisible to the user due to the immediate execution of the refresh entry in the response header. The user is then redirected to a final landing page, typically a spoofed login page mimicking a well-known service, such as Microsoft Outlook.
The page is pre-filled with the victim's email address to increase credibility, prompting them to enter their credentials, which are then harvested by the threat actor.
Adobe Issues Secondary Patch for Use-After-Free Vulnerability CVE-2024-41869 in Acrobat and Acrobat Reader
Source: Insikt Group, Adobe | Vulnerability Intelligence
Intelligence Cards: Intelligence & Reports
CVE-2024-41869 | CVVS Score: 7.8 | Recorded Future Risk Score: High – 79
On September 10, 2024, Adobe released a secondary patch for a critical severity vulnerability in Acrobat and Acrobat Reader, tracked as CVE-2024-41869. Cybersecurity researcher Haifei Li identified and disclosed the flaw on June 23, 2024, through the EXPMON sandbox platform.
Although Adobe issued an initial patch on August 13, 2024, it did not fully resolve CVE-2024-41869, which meant that the flaw could still be exploited. However, at the time of writing, there have been no reports of this vulnerability having been exploited in the wild.
CVE-2024-41869 is a use-after-free flaw that arises from improper memory management. To exploit the vulnerability, threat actors must send a maliciously crafted PDF file that, when opened by the victim, triggers the use-after-free condition. This allows arbitrary code embedded in the PDF to execute on the compromised system.
Adobe recommends updating Acrobat and Acrobat Reader to the latest software versions to mitigate the risk of exploitation.
Remediation Actions
Following the information provided above, we recommend that the technologies mentioned above be fully patched and updated. We want to highlight and recommend applying the following patches should they apply:
- CVE-2024-41869 – Update to the latest version provided by Adobe
- CVE-2024-8190 – CSA 4.6 Patch 518 customers can update to Patch 519. But as this product has entered End-of-Life, the recommended path by Ivanti is to upgrade to CSA 5.0
- Intel UEFI and Raid Vulnerabilities – Intel has advised customers to install the latest firmware and microcode updates to address these vulnerabilities.
If you are currently an Acumen Cyber Vulnerability Management customer, we will be proactively performing the searching and hunting activities within your environment.
